The Forensic Analysis Process Chapter 2 Learn Computer Forensics 2nd

Chapter 5 Introduction To Computer Forensics Pdf Oettinger introduces the five main phases of forensic analysis: pre investigation considerations, understanding case information and legal issues, data acquisition, data analysis, and reporting. In this chapter, we have discussed the forensic analysis process. you now know how to prepare to conduct a digital forensic examination, from getting the proper equipment to the training and getting certification.

Learn Computer Forensics Aurora University Bookstore We will now discuss the forensic analysis process. as a forensic investigator, you will need to create a strategy that will enable you to conduct an efficient investigation. you also need to make sure you are familiar with your tools and the results that they will provide. Study with quizlet and memorize flashcards containing terms like what are the five subsets of the forensic analysis process?, what is the purpose of the pre investigation phase?, what are common ongoing costs in digital forensics? and more. You will also learn how criminal investigations are performed online while preserving data such as e mails, images, and videos that may be important to a case. you will further explore networking and understand network topologies, ip addressing, and network devices. Starting with an overview of forensics and all the open source and commercial tools needed to get the job done, you'll learn core forensic practices for searching databases and analyzing data over networks, personal devices, and web applications.
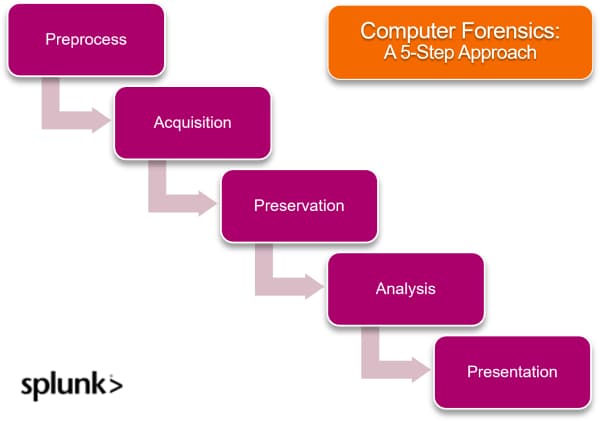
Computer Forensics Everything You Need To Know Splunk You will also learn how criminal investigations are performed online while preserving data such as e mails, images, and videos that may be important to a case. you will further explore networking and understand network topologies, ip addressing, and network devices. Starting with an overview of forensics and all the open source and commercial tools needed to get the job done, you'll learn core forensic practices for searching databases and analyzing data over networks, personal devices, and web applications. Learn computer forensics from a veteran investigator and technical trainer and explore how to properly document digital evidence collected about this audiobook investigate the core. We will now discuss the forensic analysis process. as a forensic investigator, you will need to create a strategy that will enable you to conduct an efficient investigation. you also need to make sure you are familiar with your tools and the results that they will provide. In this chapter, we have discussed the forensic analysis process. you now know how to prepare to conduct a digital forensic examination, from getting the proper equipment to training and getting certification. The forensic analysis process. a chapter from learn computer forensics – 2nd edition second edition by william oettinger.
Chapter 12 Computer Forensics Pdf Learn computer forensics from a veteran investigator and technical trainer and explore how to properly document digital evidence collected about this audiobook investigate the core. We will now discuss the forensic analysis process. as a forensic investigator, you will need to create a strategy that will enable you to conduct an efficient investigation. you also need to make sure you are familiar with your tools and the results that they will provide. In this chapter, we have discussed the forensic analysis process. you now know how to prepare to conduct a digital forensic examination, from getting the proper equipment to training and getting certification. The forensic analysis process. a chapter from learn computer forensics – 2nd edition second edition by william oettinger.

Module 2 Computer Forensics Investigation Process Lab Assessment In this chapter, we have discussed the forensic analysis process. you now know how to prepare to conduct a digital forensic examination, from getting the proper equipment to training and getting certification. The forensic analysis process. a chapter from learn computer forensics – 2nd edition second edition by william oettinger.
Comments are closed.