The Dangers Of Malicious Browser Extensions Mycrypto Blog
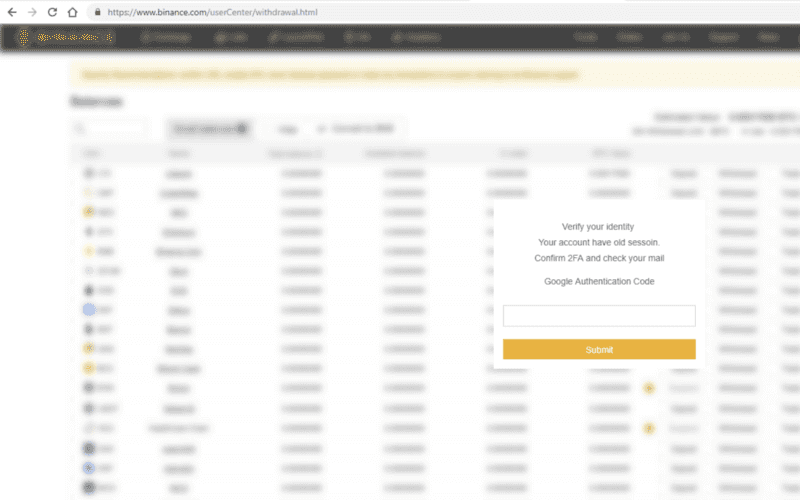
The Dangers Of Malicious Browser Extensions Mycrypto Blog When you first install the browser extension it asks for write access to multiple domains including github, exmo, coinbase, binance, hitbtc, localbitcoins, and more. it requests access to all open tabs and your cookies — these permissions are abused a lot to steal your assets from various exchanges and wallet services. what does it do?. When you first install the browser extension it asks for write access to multiple domains including github, exmo, coinbase, binance, hitbtc, localbitcoins, and more. it requests access to all.
The Dangers Of Malicious Browser Extensions Mycrypto Blog Whilst there are many different attack vectors for everyday cryptocurrency users that are not limited to malicious browser extensions, the following will be addressing only the malicious browser extensions. By analyzing real world examples and examining attack techniques employed by malicious extensions, the study highlights the evolving threat landscape posed by browser extensions in the year 2025. In this blog, i will introduce the structure of a browser extension and the vulnerabilities that are present in the ecosystem. i will then discuss the progression of security in the extension space, highlighting the attack surface and its relationship with mitigations that have been implemented. Extension security continues to evolve, but differences in browser architecture and the extension review processes ultimately shape how each browser detects and mitigates malicious extension risk.
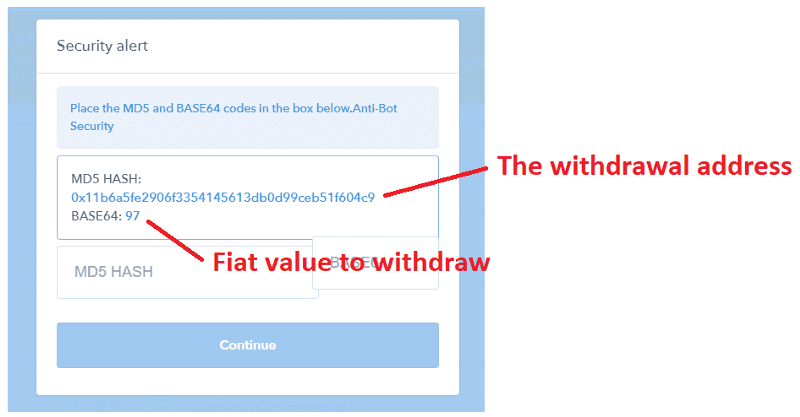
The Dangers Of Malicious Browser Extensions Mycrypto Blog In this blog, i will introduce the structure of a browser extension and the vulnerabilities that are present in the ecosystem. i will then discuss the progression of security in the extension space, highlighting the attack surface and its relationship with mitigations that have been implemented. Extension security continues to evolve, but differences in browser architecture and the extension review processes ultimately shape how each browser detects and mitigates malicious extension risk. Researchers have discovered a campaign of malicious browser extensions that were available in the official chrome and edge web stores. As the use of fake browser extensions to scam crypto users continues to increase, mycrypto, in collaboration with phishfort, investigated the attacks. mycrypto is a platform that claims to keep “an eye on the type of attacks that come to cryptocurrency users” daily. Malicious browser extensions can steal sensitive data, track user behavior, and inject unwanted advertisements. and at worst, they can even take over a user’s browser entirely. in this blog, we’ll take a deep dive into what malicious browser extensions can do and how to mitigate their risks. Browser extensions are an increasingly popular vehicle for threat actors. they give attackers access to a vast amount of sensitive information, with people often trusting these add ons,.
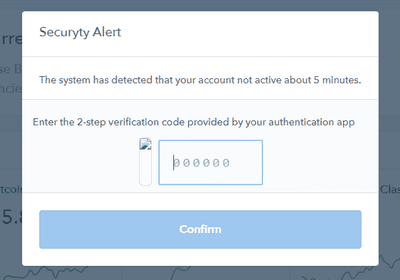
The Dangers Of Malicious Browser Extensions Mycrypto Blog Researchers have discovered a campaign of malicious browser extensions that were available in the official chrome and edge web stores. As the use of fake browser extensions to scam crypto users continues to increase, mycrypto, in collaboration with phishfort, investigated the attacks. mycrypto is a platform that claims to keep “an eye on the type of attacks that come to cryptocurrency users” daily. Malicious browser extensions can steal sensitive data, track user behavior, and inject unwanted advertisements. and at worst, they can even take over a user’s browser entirely. in this blog, we’ll take a deep dive into what malicious browser extensions can do and how to mitigate their risks. Browser extensions are an increasingly popular vehicle for threat actors. they give attackers access to a vast amount of sensitive information, with people often trusting these add ons,.

Malicious Browser Extensions Are Stealing Sensitive Authentication Data Malicious browser extensions can steal sensitive data, track user behavior, and inject unwanted advertisements. and at worst, they can even take over a user’s browser entirely. in this blog, we’ll take a deep dive into what malicious browser extensions can do and how to mitigate their risks. Browser extensions are an increasingly popular vehicle for threat actors. they give attackers access to a vast amount of sensitive information, with people often trusting these add ons,.

New Report Unveiling The Threat Of Malicious Browser Extensions
Comments are closed.