The Complete Vulnerability Assessment Process Best Practices Revealed

Vulnerability Assessment Best Practices Learn about the top 10 vulnerability assessment best practices, essential strategies, and proven methods. discover how to minimize risks, improve compliance, and protect your data from new risks now!. Learn what vulnerability assessments are, why they matter, and how they align with it risk and vulnerability management. explore the step by step process, best practices, and how manageengine vulnerability manager plus helps secure your it environment.

Business Vulnerability Assessment Best Practices Economy Gdp Learn what vulnerability assessment is, the key types and five step process, and how to build an effective va program. includes 2026 statistics and compliance mapping. In this comprehensive guide, we’ll explore vulnerability assessment methodology, the different types of vulnerability assessments, the best tools available, and best practices for conducting these assessments. Learn how to conduct a vulnerability assessment by following our step by step guide. master the vulnerability assessment process now. Learn how to conduct a vulnerability assessment to prevent security weaknesses. discover best practices and tools for vulnerability testing.
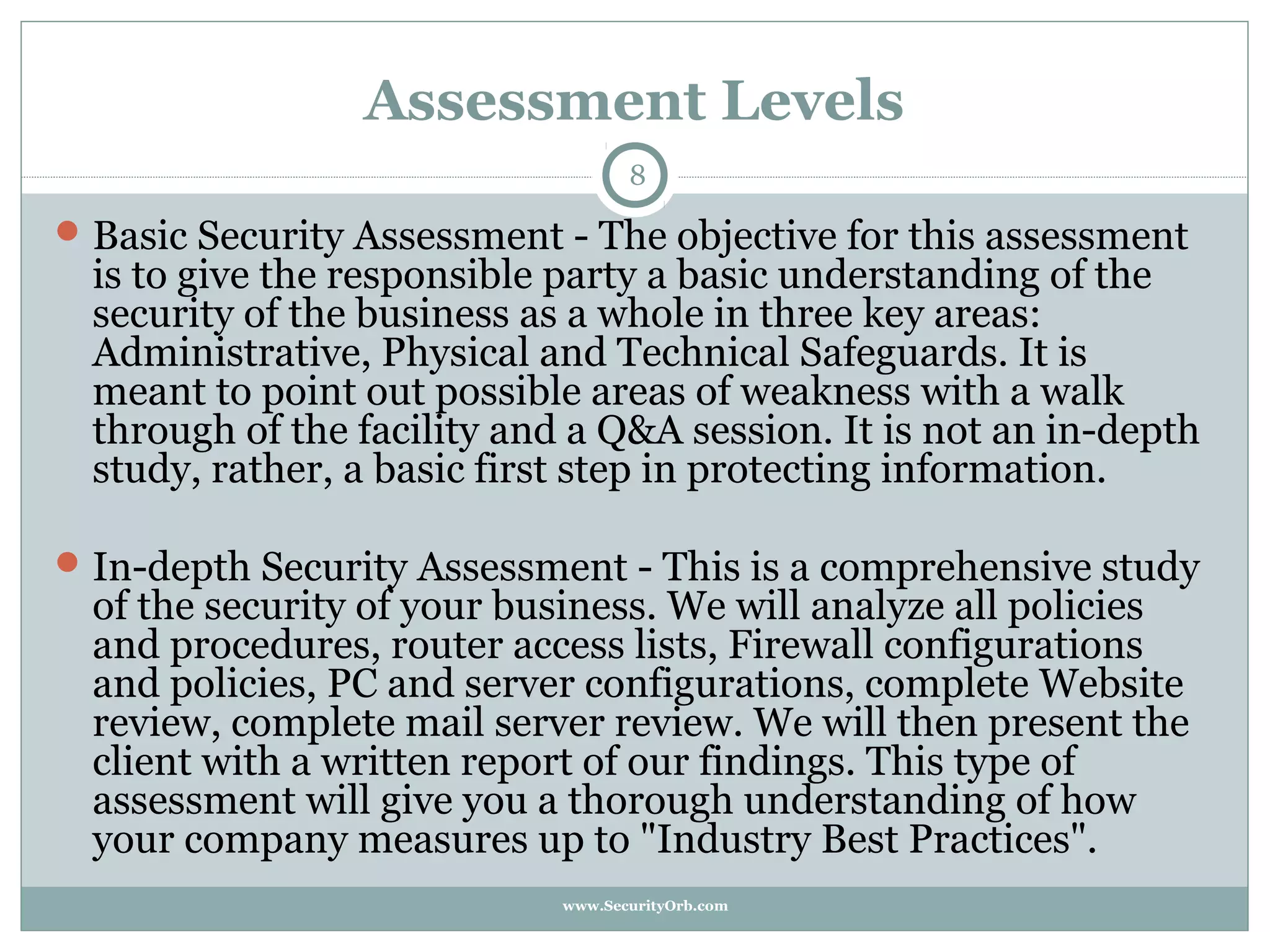
The Security Vulnerability Assessment Process Best Practices Ppt Learn how to conduct a vulnerability assessment by following our step by step guide. master the vulnerability assessment process now. Learn how to conduct a vulnerability assessment to prevent security weaknesses. discover best practices and tools for vulnerability testing. While executing a vulnerability assessment does come with its challenges, adopting certain best practices can significantly ease the process and increase its effectiveness. Conducting a vulnerability assessment is an essential part of any organization’s security strategy. by following these steps, you can identify potential vulnerabilities in your systems, networks, and applications, and take action to mitigate them before attackers do. Vulnerability assessment is a process that identifies security weaknesses of any it system, network, application, or cloud environment. it is a proactive approach to detect and fix security gaps before any cyber criminals exploit them. Vulnerability scanning is a critical component of a comprehensive cybersecurity strategy. by prioritizing vulnerabilities based on asset criticality, conducting consistent and comprehensive scans, and leveraging external tools and expertise, organizations can effectively identify and address weaknesses in their systems, networks, and applications.
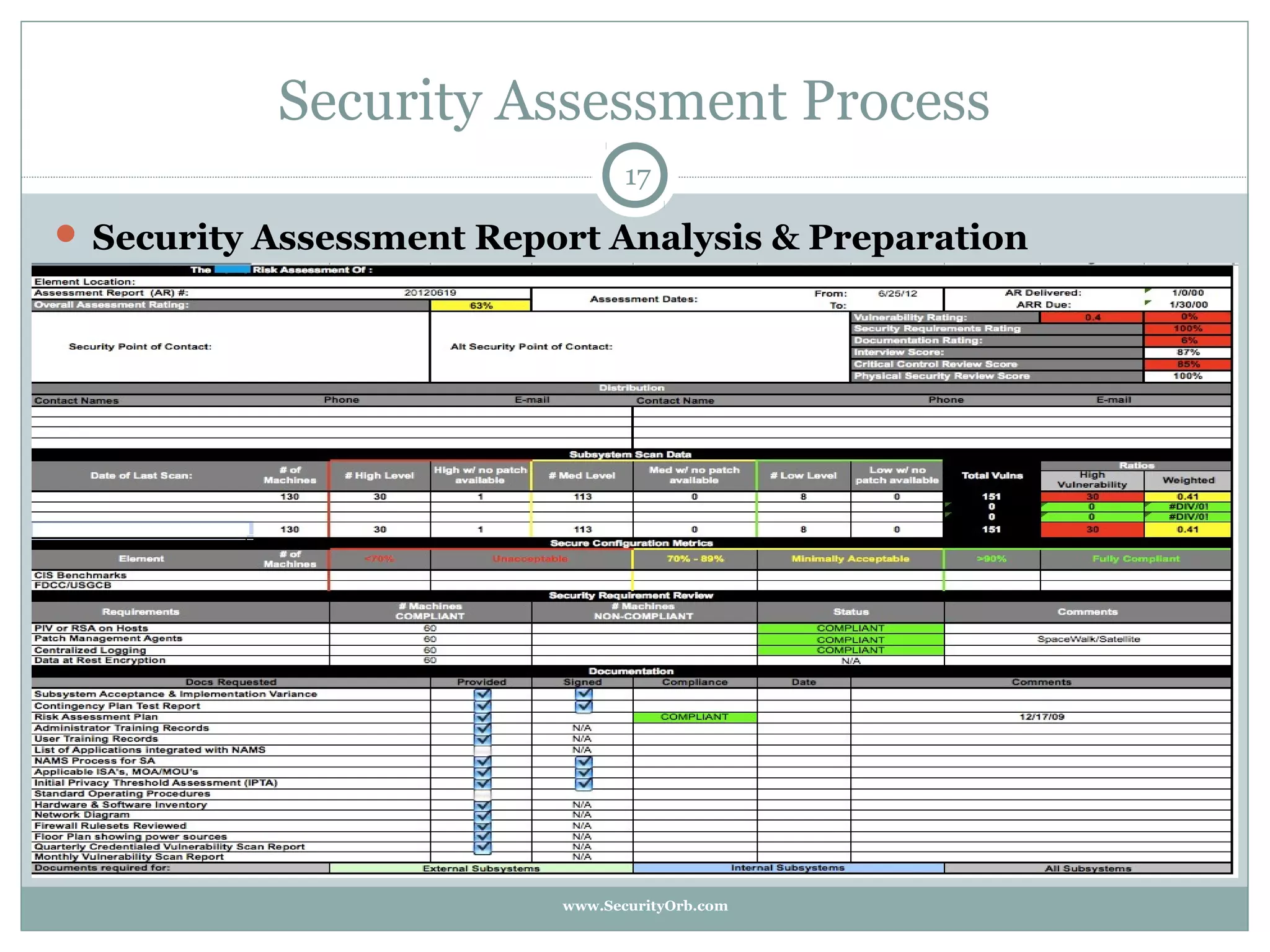
The Security Vulnerability Assessment Process Best Practices Ppt While executing a vulnerability assessment does come with its challenges, adopting certain best practices can significantly ease the process and increase its effectiveness. Conducting a vulnerability assessment is an essential part of any organization’s security strategy. by following these steps, you can identify potential vulnerabilities in your systems, networks, and applications, and take action to mitigate them before attackers do. Vulnerability assessment is a process that identifies security weaknesses of any it system, network, application, or cloud environment. it is a proactive approach to detect and fix security gaps before any cyber criminals exploit them. Vulnerability scanning is a critical component of a comprehensive cybersecurity strategy. by prioritizing vulnerabilities based on asset criticality, conducting consistent and comprehensive scans, and leveraging external tools and expertise, organizations can effectively identify and address weaknesses in their systems, networks, and applications.
Comments are closed.