The Complete Guide To Ssh Secure Shell Protocol

Ssh Secure Shell Pdf This guide provides an in depth overview of ssh, including its configuration, public private key based authentication, advanced features, x11 forwarding, and best practices for secure usage. Ssh provides a secure channel over an unsecured network by encrypting the data exchanged between the client and the server. this guide will take you through the comprehensive details of ssh, from its history and key features to advanced configurations and security best practices.
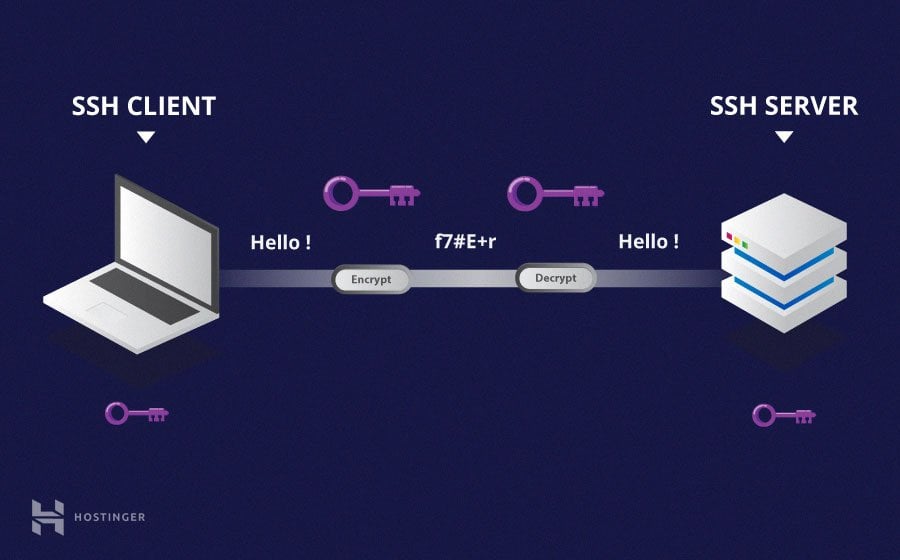
Secure Shell Protocol Ssh Msblab Learn ssh from the ground up with this complete guide covering client setup, ssh keys, configuration, server hardening, and real world troubleshooting. master secure remote access with learn linux tv. It is widely used for remote login and other secure network services. in this comprehensive guide, we will delve into the fundamentals of ssh, explore its configuration and advanced techniques, discuss security best practices, and offer troubleshooting tips for common ssh issues. Complete guide to the ssh (secure shell) protocol. learn how ssh key exchange works, authentication methods (password vs public key), port forwarding, tunneling, and the three ssh sub protocols. visual diagrams and examples included. Ssh (secure shell protocol) is a cryptographic network protocol for secure remote access to systems tagged with ssh.

Ssh Guide For It Professionals Pdf Complete guide to the ssh (secure shell) protocol. learn how ssh key exchange works, authentication methods (password vs public key), port forwarding, tunneling, and the three ssh sub protocols. visual diagrams and examples included. Ssh (secure shell protocol) is a cryptographic network protocol for secure remote access to systems tagged with ssh. Ssh (secure shell) is the standard way to remotely manage linux servers. it encrypts all traffic between your machine and the server — commands, file transfers, and even forwarded ports are all secured. this guide covers everything from basic connections to advanced tunneling and security. Whether you’re logging into a cloud server, configuring a router, or transferring files between systems, mastering the ssh command is an essential skill. this guide will demystify ssh, from its core concepts to advanced use cases, ensuring you can leverage its power securely and efficiently. The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption. The secure shell (ssh) protocol sets up encrypted connections for remote logins and file transfers between computers. ssh also enables tunneling. learn how ssh works.
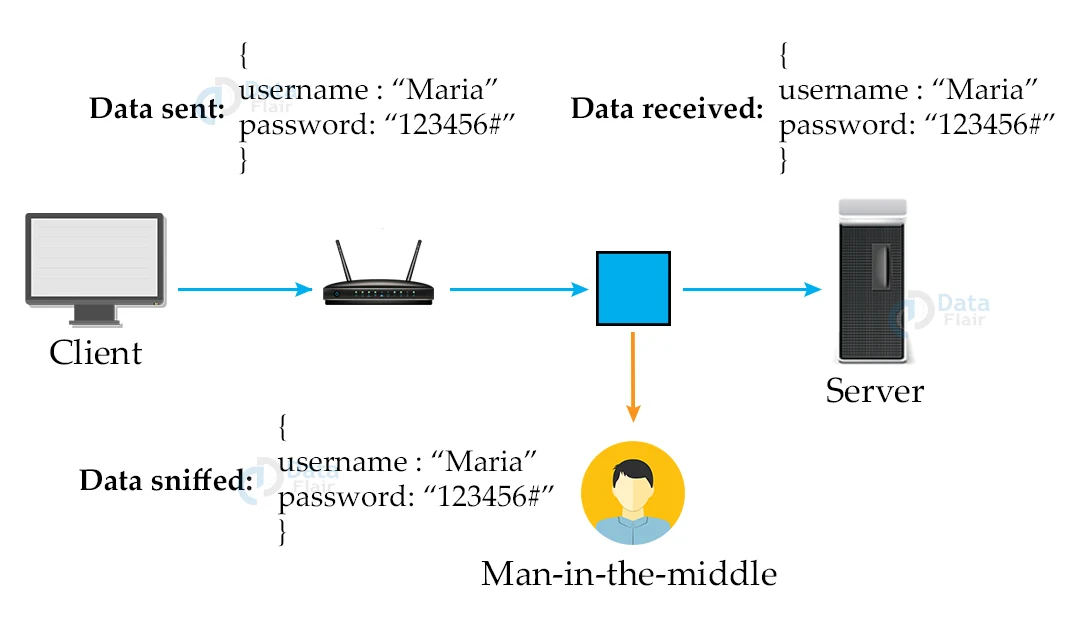
Ssh Protocol Secure Shell Dataflair Ssh (secure shell) is the standard way to remotely manage linux servers. it encrypts all traffic between your machine and the server — commands, file transfers, and even forwarded ports are all secured. this guide covers everything from basic connections to advanced tunneling and security. Whether you’re logging into a cloud server, configuring a router, or transferring files between systems, mastering the ssh command is an essential skill. this guide will demystify ssh, from its core concepts to advanced use cases, ensuring you can leverage its power securely and efficiently. The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption. The secure shell (ssh) protocol sets up encrypted connections for remote logins and file transfers between computers. ssh also enables tunneling. learn how ssh works.
Comments are closed.