Tenable Product Usage Analysis Agent
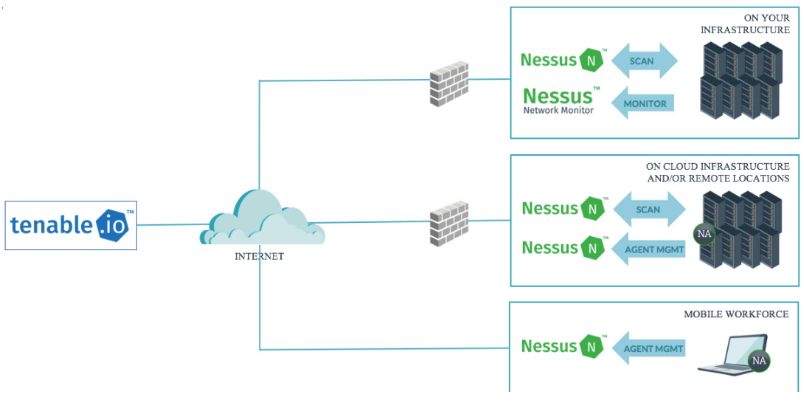
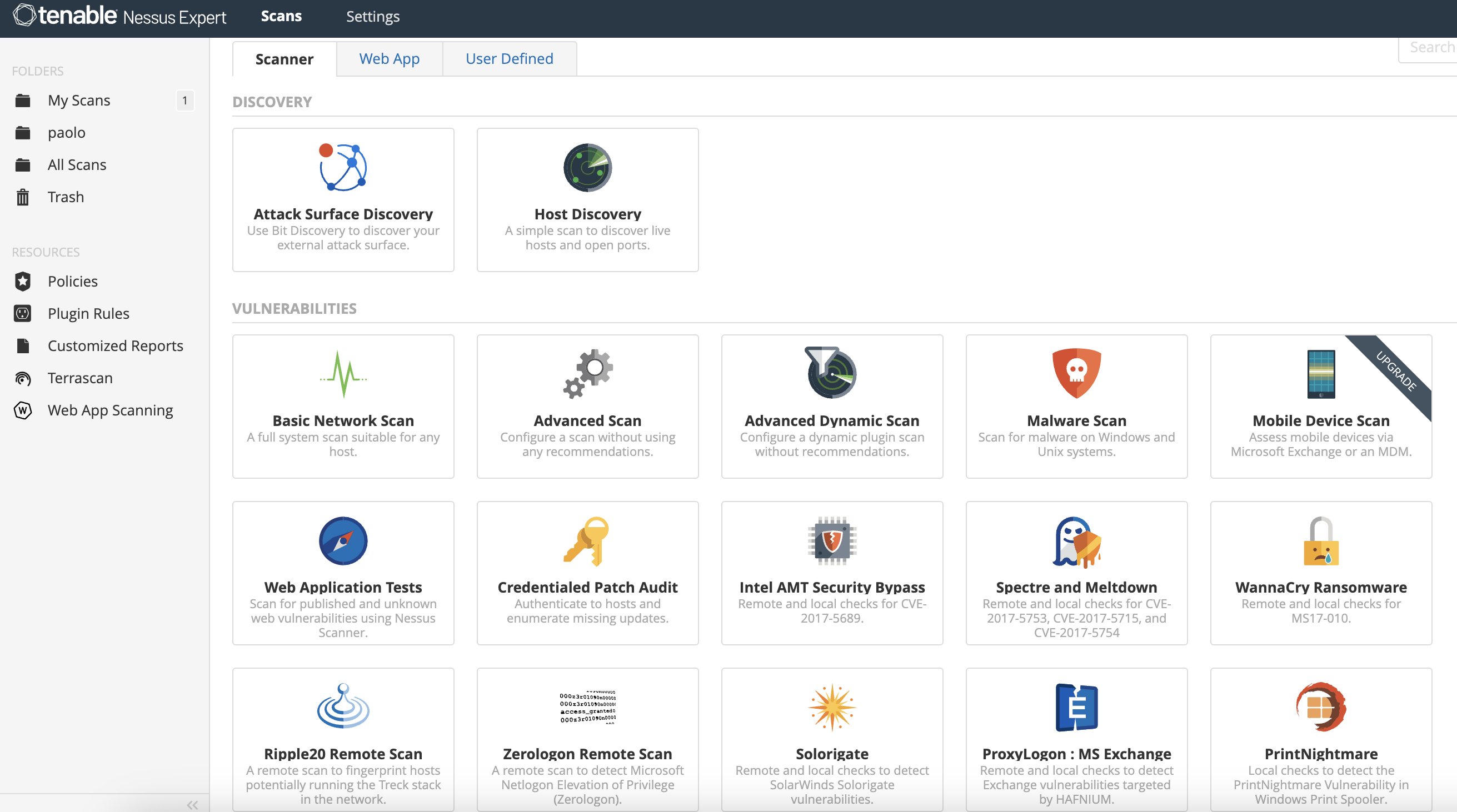
Product Architecture This video uses synthetic data to demonstrate an agentic workflow for trusted product usage analytics and insights. Tenable agents collect vulnerability, compliance, and system data, and report that information back to a manager for analysis. with tenable agents, you extend scan flexibility and coverage. you can scan hosts and endpoints that intermittently connect to the internet without using credentials.

Understanding Tenable Nessus Agent Enhancing Cybersecurity Simplified The tenable product education channel is where you find how to resources to ensure you get the most from your cybersecurity investment. For training videos, please see the tenable product education channel. For tenable security center users with over 10,000 agents and up to 200,000 agents, you can manage your agent scans from a single tenable nessus manager cluster, rather than needing to link multiple instances of tenable nessus manager to tenable security center. This enables the deployment of tenable nessus scanners throughout networks to both public and private clouds as well as multiple physical locations. in this post, i am gonna show some basic steps to bring this popular tenable vulnerability scanning tools into your environment as quick as i can.
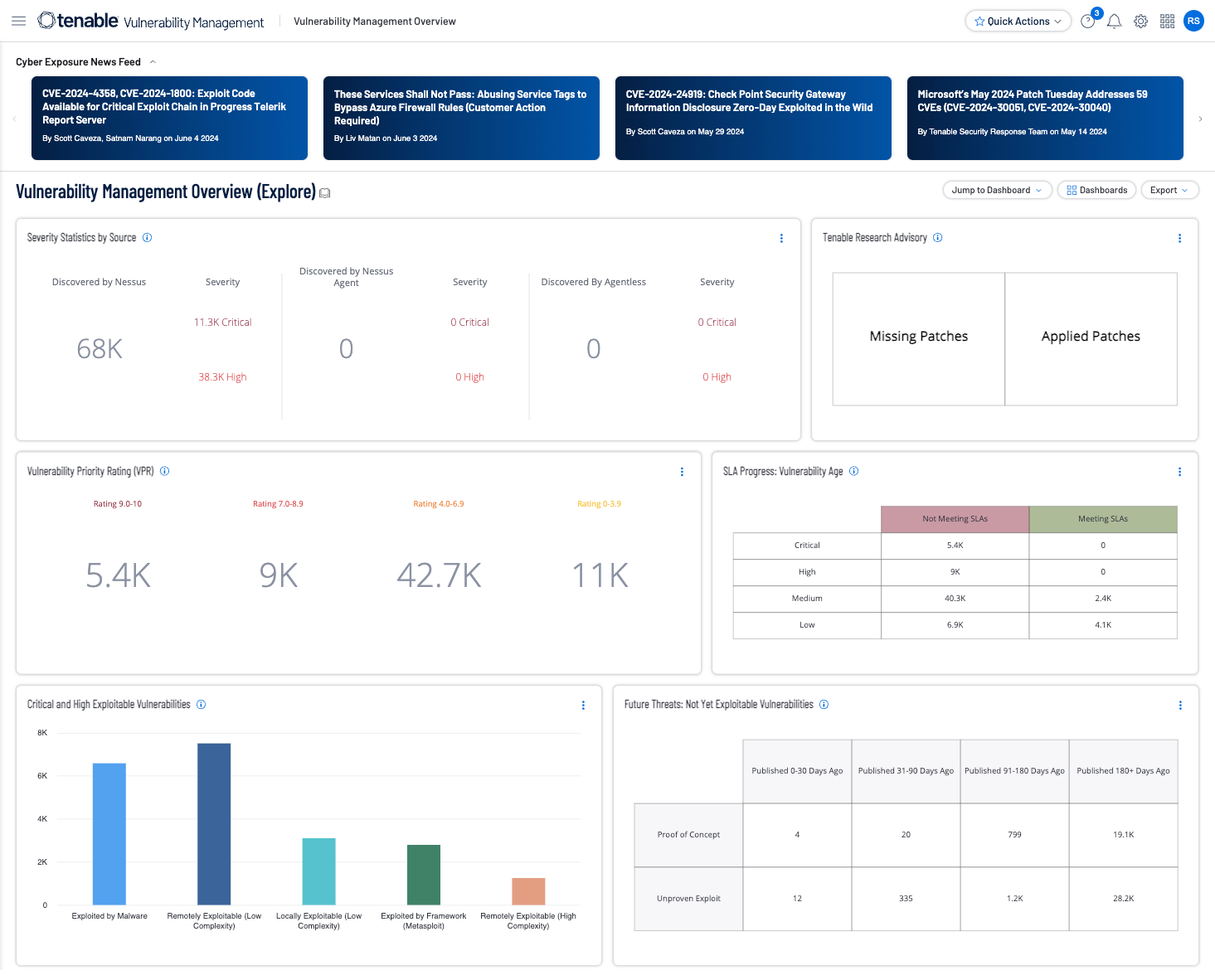
A Guide To Tenable S Exposure Management Solutions Tenable For tenable security center users with over 10,000 agents and up to 200,000 agents, you can manage your agent scans from a single tenable nessus manager cluster, rather than needing to link multiple instances of tenable nessus manager to tenable security center. This enables the deployment of tenable nessus scanners throughout networks to both public and private clouds as well as multiple physical locations. in this post, i am gonna show some basic steps to bring this popular tenable vulnerability scanning tools into your environment as quick as i can. Tenable agents collect vulnerability, compliance, and system data, and report that information back to a manager for analysis. with tenable agents, you extend scan flexibility and coverage. you can scan hosts and endpoints that intermittently connect to the internet without using credentials. Tenable nessus agent download nessus agents for use with tenable vulnerability management and nessus manager view downloads. A tenable agent uses almost no cpu while idle, but is designed to use up to 100% of the cpu when available during jobs. to measure network utilization when uploading results, tenable monitored agent uploads into tenable vulnerability management over a seven day period. Tenable one is an exposure management platform to help organizations gain visibility across the modern attack surface, focus efforts to prevent likely attacks and accurately communicate cyber risk to support optimal business performance.
A Guide To Tenable S Exposure Management Solutions Tenable Tenable agents collect vulnerability, compliance, and system data, and report that information back to a manager for analysis. with tenable agents, you extend scan flexibility and coverage. you can scan hosts and endpoints that intermittently connect to the internet without using credentials. Tenable nessus agent download nessus agents for use with tenable vulnerability management and nessus manager view downloads. A tenable agent uses almost no cpu while idle, but is designed to use up to 100% of the cpu when available during jobs. to measure network utilization when uploading results, tenable monitored agent uploads into tenable vulnerability management over a seven day period. Tenable one is an exposure management platform to help organizations gain visibility across the modern attack surface, focus efforts to prevent likely attacks and accurately communicate cyber risk to support optimal business performance.
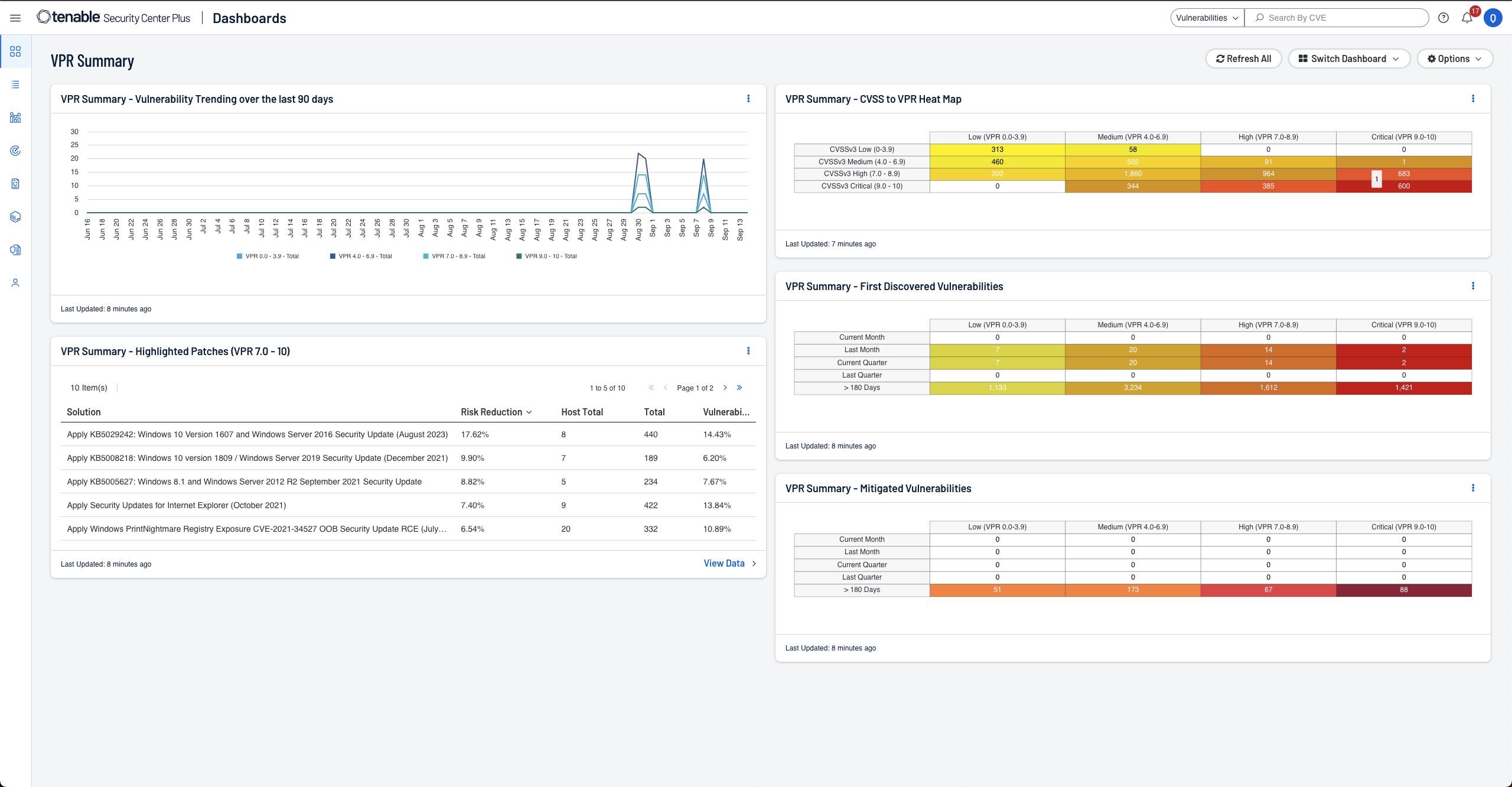
A Guide To Tenable S Exposure Management Solutions Tenable A tenable agent uses almost no cpu while idle, but is designed to use up to 100% of the cpu when available during jobs. to measure network utilization when uploading results, tenable monitored agent uploads into tenable vulnerability management over a seven day period. Tenable one is an exposure management platform to help organizations gain visibility across the modern attack surface, focus efforts to prevent likely attacks and accurately communicate cyber risk to support optimal business performance.
Comments are closed.