Teiss Cyber Risk Management Reframing Resilience

Nist Cyber Resilience Framework Overview Pdf Information Security In a cyber security context, business resilience begins with bolstering defences against compromise. but as no organisation is 100% breach proof, it also demands that plans be put in place so an organisation can continue operating even in the event of a security breach. Organisations need to be resilient to cyber threats. they must be able to respond and recover in the event of a critical incident. increasingly, such incidents are ai enabled, and the response is automated. security teams face the challenge of balancing between enabling innovation and security.

Teiss Cyber Risk Management Reframing Resilience Gain practical insights from cyber and risk leaders as they unpack the biggest challenges and opportunities facing security teams today. 🎤 featuring: laurie gibbett, cyber risk. This highlights the need for all organisations, including all schools and colleges to consider cyber risks and their defensive and recovery methods. there is no excuse for having not done so. Altum strategy group that draws on proprietary survey data to reframe cybersecurity as a measurable enterprise resilience discipline. The pivotal literature review examining resilience and risk management in cybersecurity comprises the various dimensions that are essential to comprehending the emotional, psychological and organizational dynamics in the respective field.
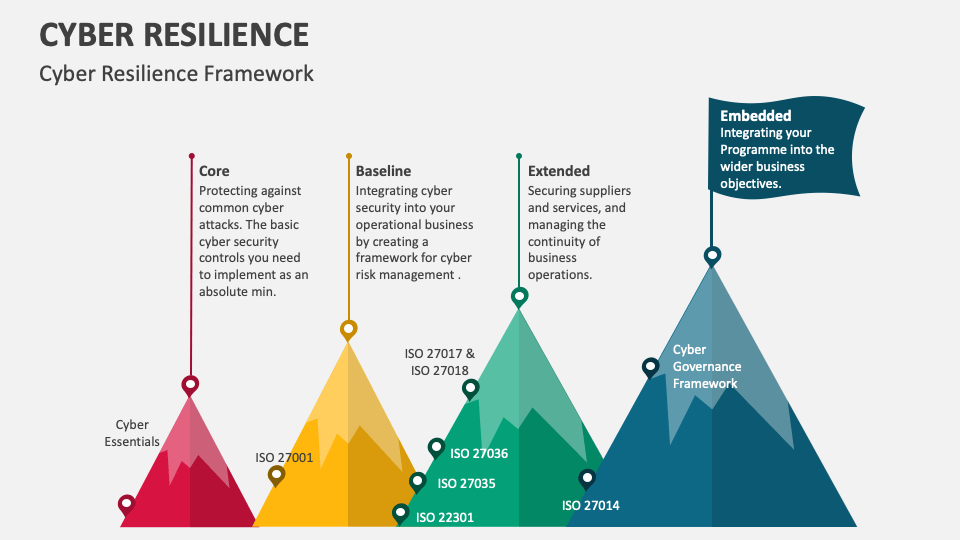
Cyber Resilience Powerpoint And Google Slides Template Ppt Slides Altum strategy group that draws on proprietary survey data to reframe cybersecurity as a measurable enterprise resilience discipline. The pivotal literature review examining resilience and risk management in cybersecurity comprises the various dimensions that are essential to comprehending the emotional, psychological and organizational dynamics in the respective field. This study presents a cyber resilience management framework based on an exploratory multiple case study analysis across four organizations and an analysis of existing cybersecurity. As cyber resilience gains greater prominence in board level and c level discussions worldwide, leaders increasingly recognize cyber risk as a core business, operational and governance issue. Third party suppliers are appealing to cyber criminals, making embedding predictive resilience critical in identifying any potential risks before they can escalate. managing supply chains can be a huge challenge for businesses. To mitigate growing cyber resilience risk, leadership teams must invest in embedding visibility and control into their security solutions’ very fabric. this is enabled through an approach we call ‘resilient by design,’ which starts by moving to a modern zero trust architecture.
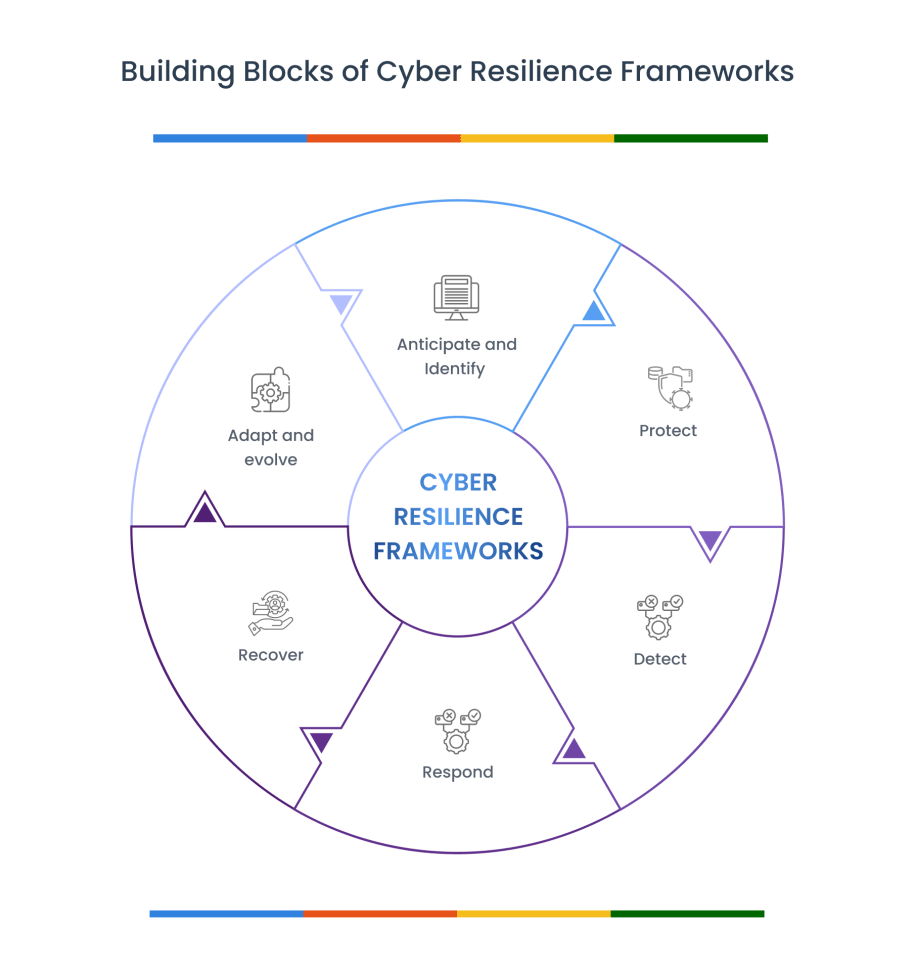
What Is Cyber Resilience A Complete Guide This study presents a cyber resilience management framework based on an exploratory multiple case study analysis across four organizations and an analysis of existing cybersecurity. As cyber resilience gains greater prominence in board level and c level discussions worldwide, leaders increasingly recognize cyber risk as a core business, operational and governance issue. Third party suppliers are appealing to cyber criminals, making embedding predictive resilience critical in identifying any potential risks before they can escalate. managing supply chains can be a huge challenge for businesses. To mitigate growing cyber resilience risk, leadership teams must invest in embedding visibility and control into their security solutions’ very fabric. this is enabled through an approach we call ‘resilient by design,’ which starts by moving to a modern zero trust architecture.
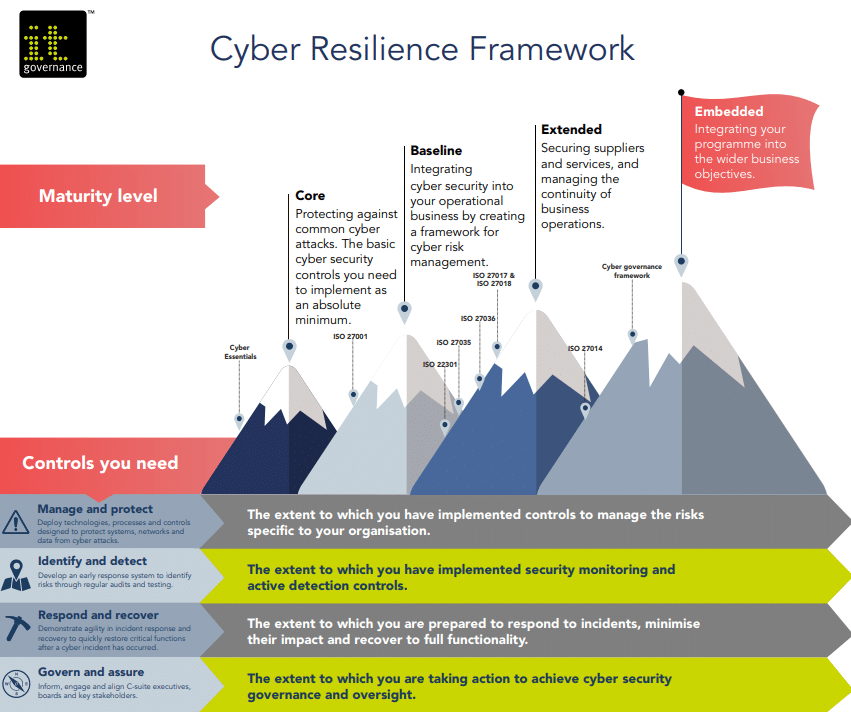
5 Steps To Building A Robust Cyber Resilience Framework Spectral Third party suppliers are appealing to cyber criminals, making embedding predictive resilience critical in identifying any potential risks before they can escalate. managing supply chains can be a huge challenge for businesses. To mitigate growing cyber resilience risk, leadership teams must invest in embedding visibility and control into their security solutions’ very fabric. this is enabled through an approach we call ‘resilient by design,’ which starts by moving to a modern zero trust architecture.

How To Construct An Effective Cyber Resilience Strategy Kahootz
Comments are closed.