Technologies Used In Zero Trust Network Access Zero Trust Network Security
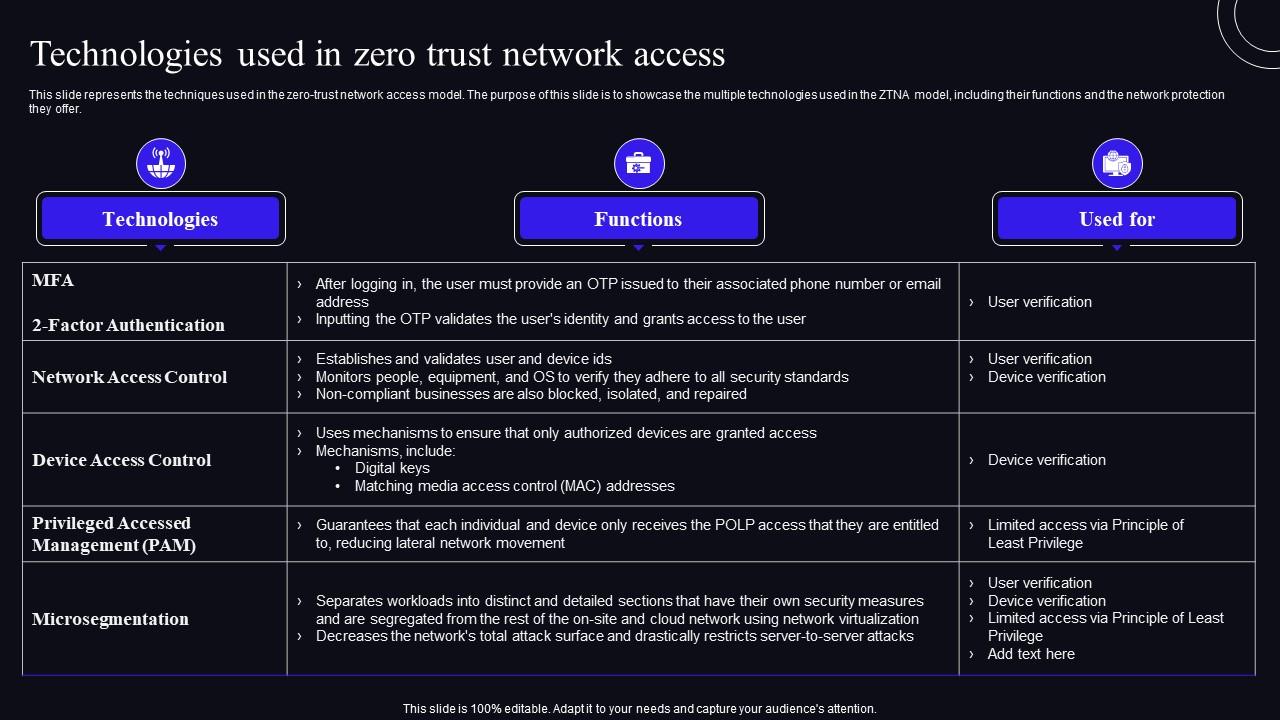
Technologies Used In Zero Trust Network Access Zero Trust Security Discover the essentials of zero trust network access (ztna), its role in cybersecurity, and key advantages in securing remote work environments. You can set up a zero trust network by first assessing the value and vulnerability of corporate assets. next, define and automate multi factor authentication (mfa) policies to allow users and devices access to the assets they need.
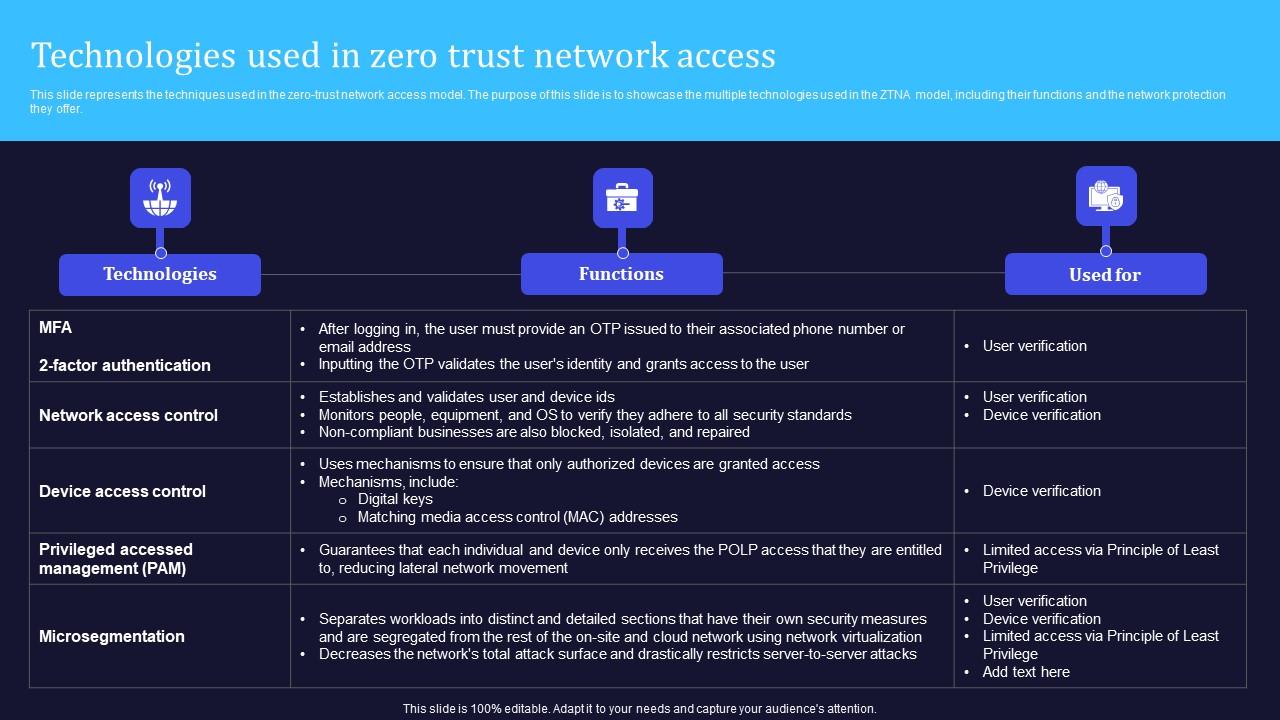
Zero Trust Model Technologies Used In Zero Trust Network Access Ztna is the technology that enables organizations to implement a zero trust security model. learn how ztna works, contrast ztna with vpns, and more. Organizations can implement zero trust network access (ztna) by verifying user identities and device security continuously, using tools like multi factor authentication (mfa) and endpoint security checks. Learn about zero trust network access (ztna) and its role in modern cybersecurity. explore how it secures remote access with strict verification. Learn about the differences between zero trust and secure access service edge (sase) as we answer common questions that organizations have when incorporating these into their overarching cybersecurity framework.

Working Of Zero Trust Network Access Model Zero Trust Security Model Learn about zero trust network access (ztna) and its role in modern cybersecurity. explore how it secures remote access with strict verification. Learn about the differences between zero trust and secure access service edge (sase) as we answer common questions that organizations have when incorporating these into their overarching cybersecurity framework. Achieving zero trust security requires a combination of two key elements: zero trust network access (ztna), which delivers zero trust from the outside, and microsegmentation, which achieves zero trust from the inside – for example, between machines within your network. Discover what zero trust network access (ztna) is, its benefits, types, and how to implement secure access with best practices. A technology that is replacing vpns is zero trust network access (ztna). in this blog post, we’ll dive deep into ztna and explore the models, principles, and architectures that make it a more secure and scalable way to provide remote connectivity. While both virtual private networks (vpns) and zero trust network access (ztna) provide secure remote access, they differ fundamentally in architecture, trust model, and security posture.

Zero Trust Network Access Ending Implicit Trust In Cybersecurity Achieving zero trust security requires a combination of two key elements: zero trust network access (ztna), which delivers zero trust from the outside, and microsegmentation, which achieves zero trust from the inside – for example, between machines within your network. Discover what zero trust network access (ztna) is, its benefits, types, and how to implement secure access with best practices. A technology that is replacing vpns is zero trust network access (ztna). in this blog post, we’ll dive deep into ztna and explore the models, principles, and architectures that make it a more secure and scalable way to provide remote connectivity. While both virtual private networks (vpns) and zero trust network access (ztna) provide secure remote access, they differ fundamentally in architecture, trust model, and security posture.
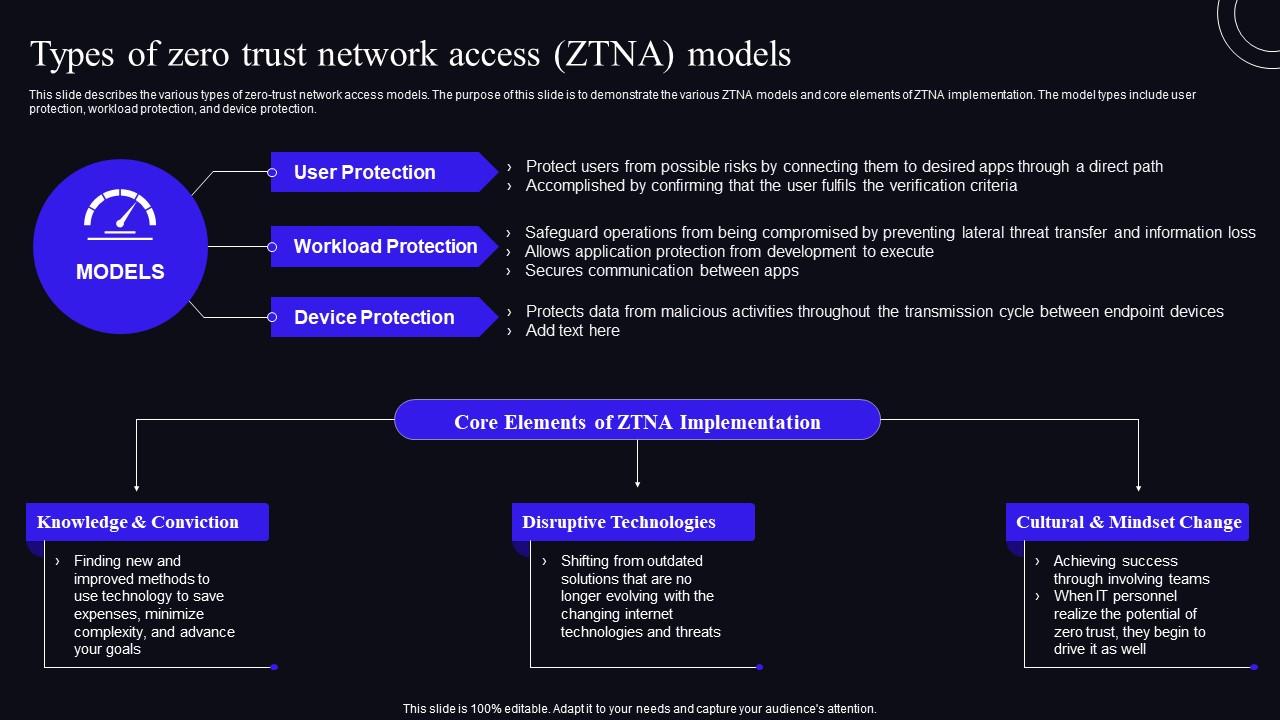
Types Of Zero Trust Network Access Ztna Models Zero Trust Security A technology that is replacing vpns is zero trust network access (ztna). in this blog post, we’ll dive deep into ztna and explore the models, principles, and architectures that make it a more secure and scalable way to provide remote connectivity. While both virtual private networks (vpns) and zero trust network access (ztna) provide secure remote access, they differ fundamentally in architecture, trust model, and security posture.

Zero Trust Network Access Overview Of Zero Trust Solution Categories
Comments are closed.