Techniques Of Saas Compromise
Stop Guessing The Ultimate Guide To Saas Conversion Optimization Png Learn how attackers use oauth tokens, session hijacking, and lateral movement to compromise saas applications. expert analysis of real breaches and detection strategies. We're sharing a collection of saas attack techniques to help defenders understand the threats they face. our goal at push is simple — to stop identity attacks. today, the vast majority of identity vulnerabilities exist in the context of saas apps.
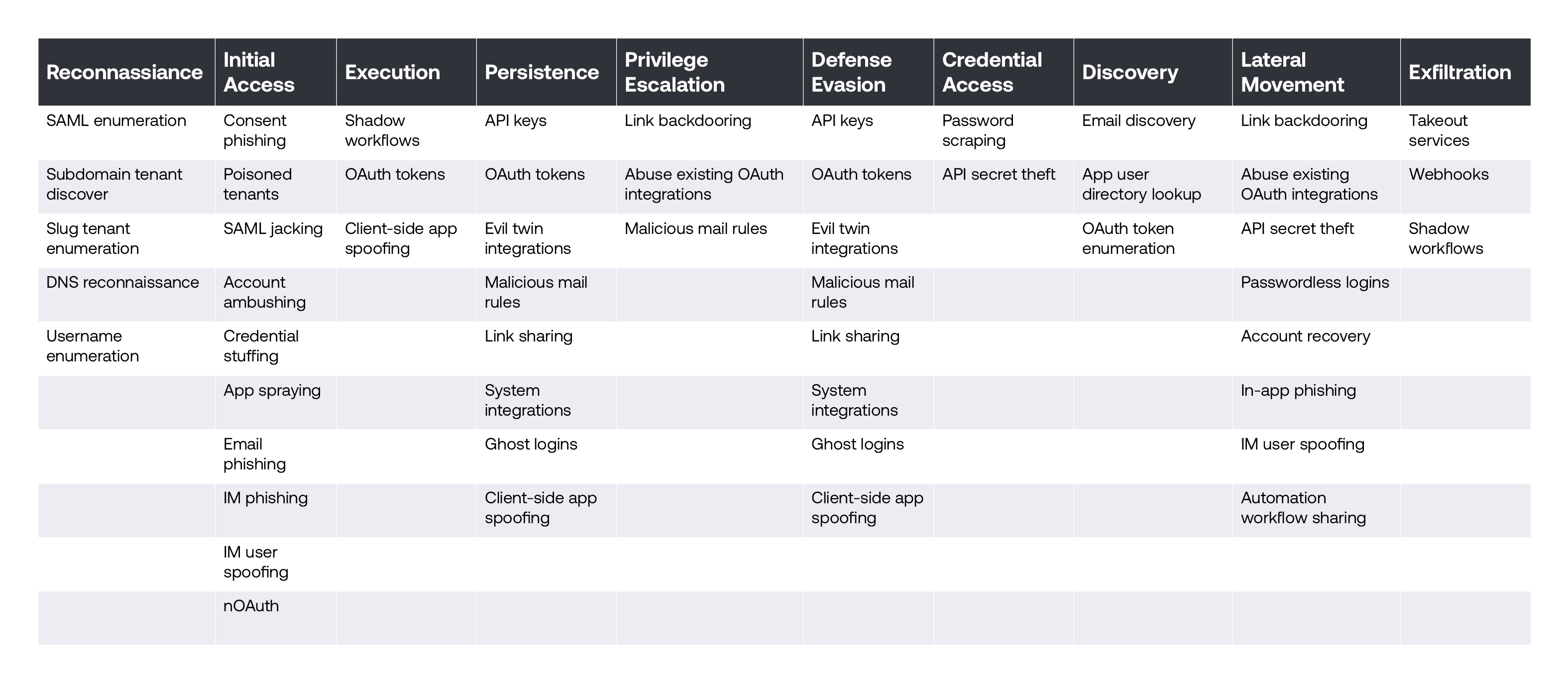
Saas Attack Techniques Offensive security drives defensive security. we're sharing a collection of saas attack techniques to help defenders understand the threats they face. This repository is a collection of saas specific attack techniques. it is intended to be a resource for security researchers, red blue teams, and penetration testers to learn about and share saas attack techniques. This incident exemplifies a modern saas breach pattern: attackers can bypass core platform exploits by compromising a trusted isv and misusing delegated integration privileges across tenants. Uncover the top three attack patterns behind the surge in saas breaches and learn which hidden risks your security team may be overlooking today.
Saas Attack Techniques This incident exemplifies a modern saas breach pattern: attackers can bypass core platform exploits by compromising a trusted isv and misusing delegated integration privileges across tenants. Uncover the top three attack patterns behind the surge in saas breaches and learn which hidden risks your security team may be overlooking today. Protecting saas applications from account compromise explained, highlighting how organizations can detect misuse, secure access, and reduce identity based risk across cloud platforms. Many organizations don’t have a way of discovering saas use in their organization yet, never mind breached accounts, so new persistence techniques might be a bit more than necessary at the. Discover the techniques that help attackers compromise saas applications and the measures they use to ensure their access is long lived. We're sharing a collection of saas attack techniques to help defenders understand the threats they face. our goal at push is simple — to reduce the risk of using cloud identities at work. to do this well, we need to build controls that are easy to use, easy to understand and, ultimately, effective.
Comments are closed.