Technical Mechanisms Of Mac Spoofing Ppt Powerpoint St Ai Ss Ppt

Cisco Ai Endpoint Analytics Solution To Mac Attribute Spoofing Cisco Unlock the secrets of mac spoofing with our comprehensive powerpoint presentation deck. dive into technical mechanisms, explore real world applications, and enhance your cybersecurity knowledge. The document discusses various methods for attacking network switches, including mac flooding attacks, mac spoofing attacks, and attacks against the spanning tree protocol (stp).
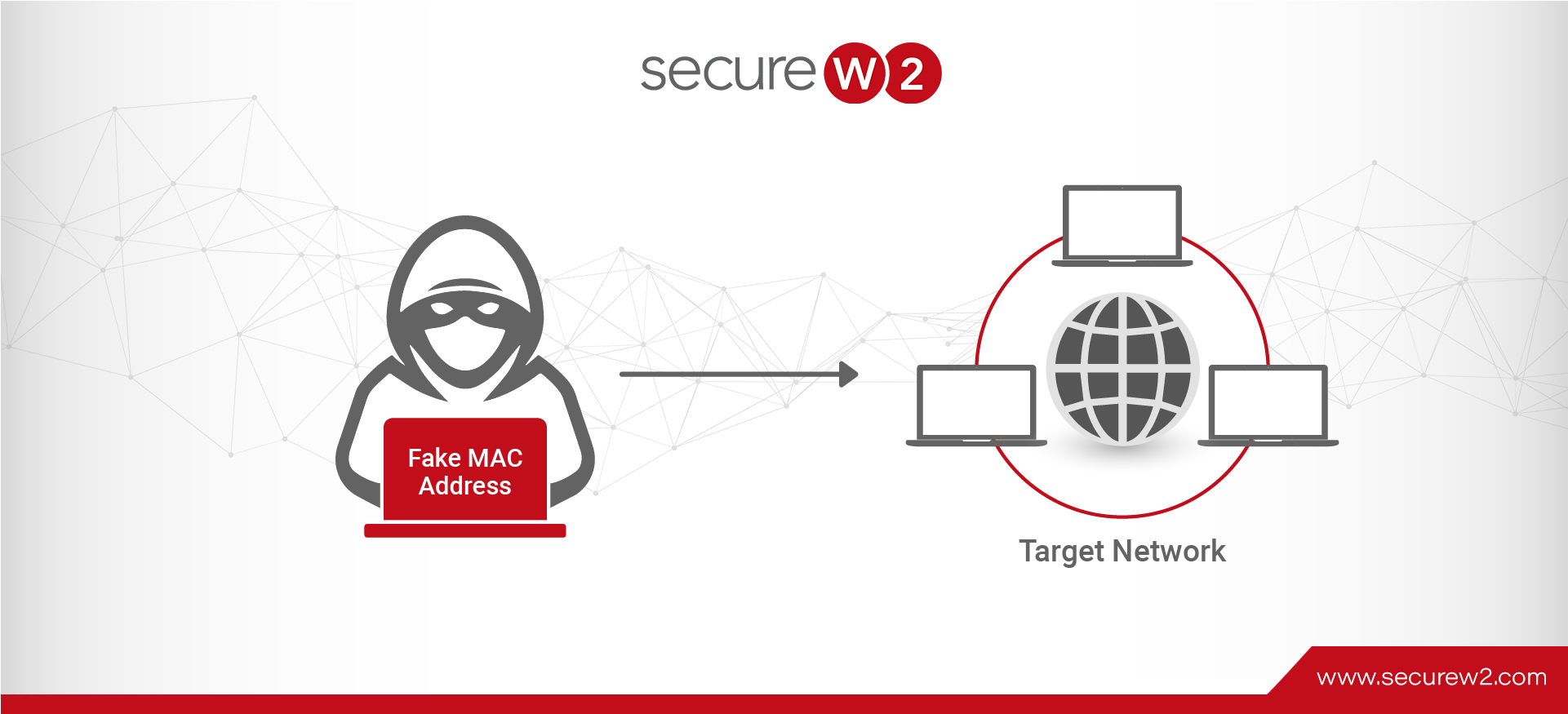
Mac Spoofing Attacks Explained A Technical Overview Packet sniffing and spoofing 1 shared networks every network packet reaches every computer's network interface card, which then filters packets based on the mac address. This study addresses the critical cybersecurity challenges faced by small and mediumsized businesses (smbs) in protecting their local area networks (lans) against evolving mac address. Introducing technical mechanisms of mac spoofing ppt powerpoint st ai ss to increase your presentation threshold. encompassed with eight stages, this template is a great option to educate and entice your audience. Enhance your cybersecurity knowledge with our professional powerpoint presentation on countermeasures against mac spoofing. this comprehensive deck covers essential strategies, real world examples, and effective solutions to protect your network.
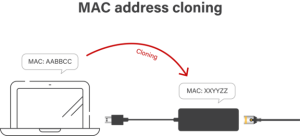
Mac Spoofing Attacks Explained A Technical Overview Introducing technical mechanisms of mac spoofing ppt powerpoint st ai ss to increase your presentation threshold. encompassed with eight stages, this template is a great option to educate and entice your audience. Enhance your cybersecurity knowledge with our professional powerpoint presentation on countermeasures against mac spoofing. this comprehensive deck covers essential strategies, real world examples, and effective solutions to protect your network. Discover the critical insights on mac spoofing and privacy concerns with our comprehensive powerpoint presentation. this deck explores the implications of mac address spoofing, potential security threats, and best practices for safeguarding personal information. Discover our comprehensive powerpoint presentation on mac spoofing incidents, featuring detailed case studies and insightful analysis. Unlock the secrets of mac spoofing with our comprehensive powerpoint presentation. designed for professionals, this deck covers essential concepts, techniques, and best practices. This article discusses the concept of mac address spoofing and its implications in bypassing network restrictions. it covers techniques for obtaining and changing a device's mac address, as well as the potential uses and risks associated with mac address spoofing.
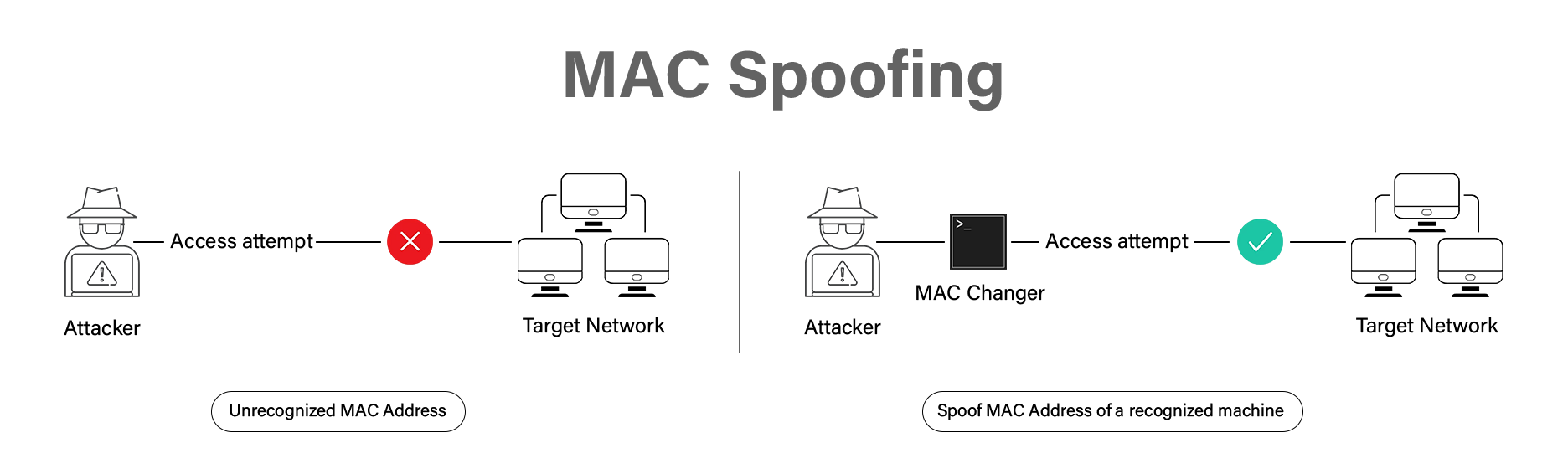
Mac Spoofing Attacks Explained A Technical Overview Discover the critical insights on mac spoofing and privacy concerns with our comprehensive powerpoint presentation. this deck explores the implications of mac address spoofing, potential security threats, and best practices for safeguarding personal information. Discover our comprehensive powerpoint presentation on mac spoofing incidents, featuring detailed case studies and insightful analysis. Unlock the secrets of mac spoofing with our comprehensive powerpoint presentation. designed for professionals, this deck covers essential concepts, techniques, and best practices. This article discusses the concept of mac address spoofing and its implications in bypassing network restrictions. it covers techniques for obtaining and changing a device's mac address, as well as the potential uses and risks associated with mac address spoofing.

Toolfad Blog Unlock the secrets of mac spoofing with our comprehensive powerpoint presentation. designed for professionals, this deck covers essential concepts, techniques, and best practices. This article discusses the concept of mac address spoofing and its implications in bypassing network restrictions. it covers techniques for obtaining and changing a device's mac address, as well as the potential uses and risks associated with mac address spoofing.
Comments are closed.