Tackle Iot Application Security Threats And Vulnerabilities Linux

Challenges Amp Security Threats In Iot With Solution Architectures Many iot applications use third party frameworks and libraries when built. if they’re obsolete or have known vulnerabilities and aren’t validated when installed in a network, they could pose security risks. Threat modeling can identify, assess and prioritize the potential iot app vulnerabilities. a model can suggest security activities that will ensure it admins include iot apps in overall security strategies.

Tackle Iot Application Security Threats And Vulnerabilities Linux Explore effective linux security practices for cloud and iot environments. learn strategies to prevent attacks and secure infrastructure. In this paper, we propose a new taint analysis solution her mescan, which directly applies traditional reaching definition analysis (rda) to the vex intermediate representation (ir) of binaries, to detect taint style vulnerabilities in linux based iot firmware. Finally, this article points out the security challenges and opportunities faced by iot operating systems, summarizes the current research status, and puts forward corresponding suggestions. Explore key challenges and strategies for securing linux based iot and edge devices, from minimizing attack surfaces to performing ota updates.
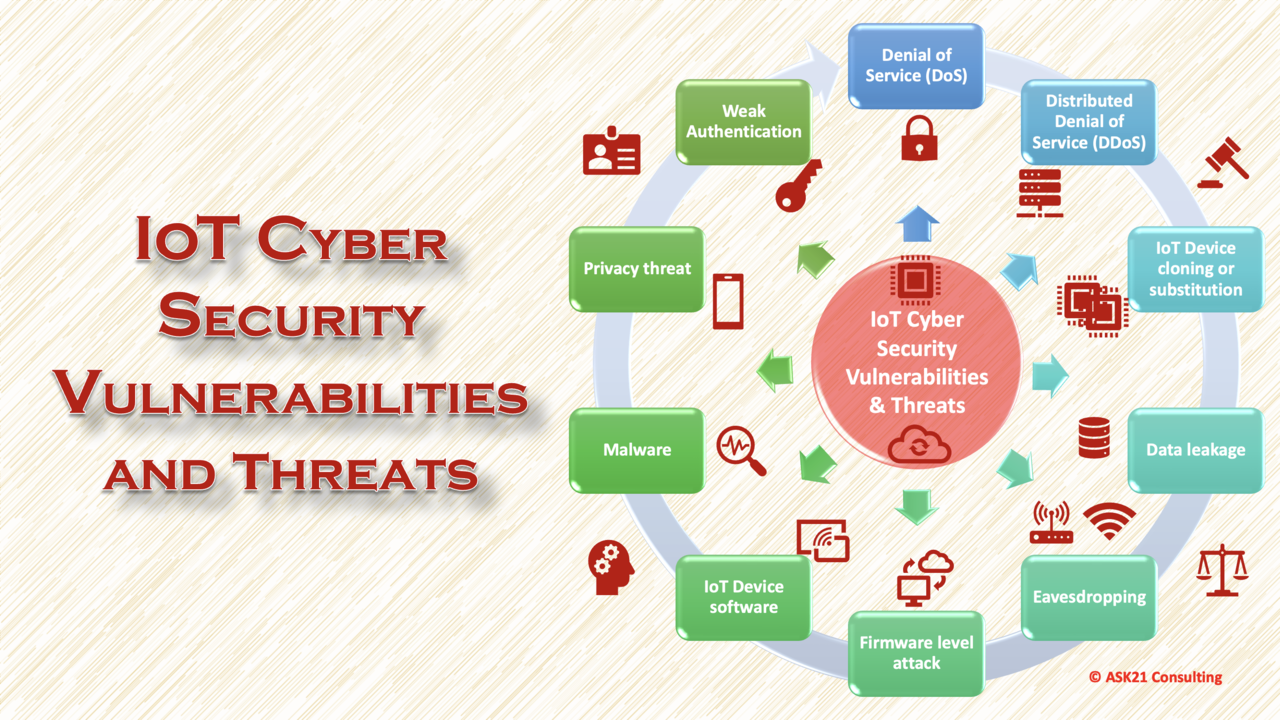
Iot Cyber Security Vulnerabilities And Threats Finally, this article points out the security challenges and opportunities faced by iot operating systems, summarizes the current research status, and puts forward corresponding suggestions. Explore key challenges and strategies for securing linux based iot and edge devices, from minimizing attack surfaces to performing ota updates. While linux provides a solid foundation for iot security, implementing best practices is essential for achieving the highest levels of security. here are some strategies to enhance the security of iot devices running linux:. Internet of things (iot) device vulnerabilities can lead to data theft and sophisticated cyberattacks. discover the top iot vulnerabilities and how to best protect your network and devices. Since cybersecurity risk for the iot spans digital security to physical security, it’s essential to address the entire confidentiality, integrity, and availability (cia) framework. What are linux security vulnerabilities? linux security vulnerabilities are weaknesses or flaws within the linux operating system that can be exploited by attackers to gain unauthorized access, escalate privileges, or perform malicious activities.
Comments are closed.