Table I From Comparative Analysis Of 5g Security Mechanisms Semantic
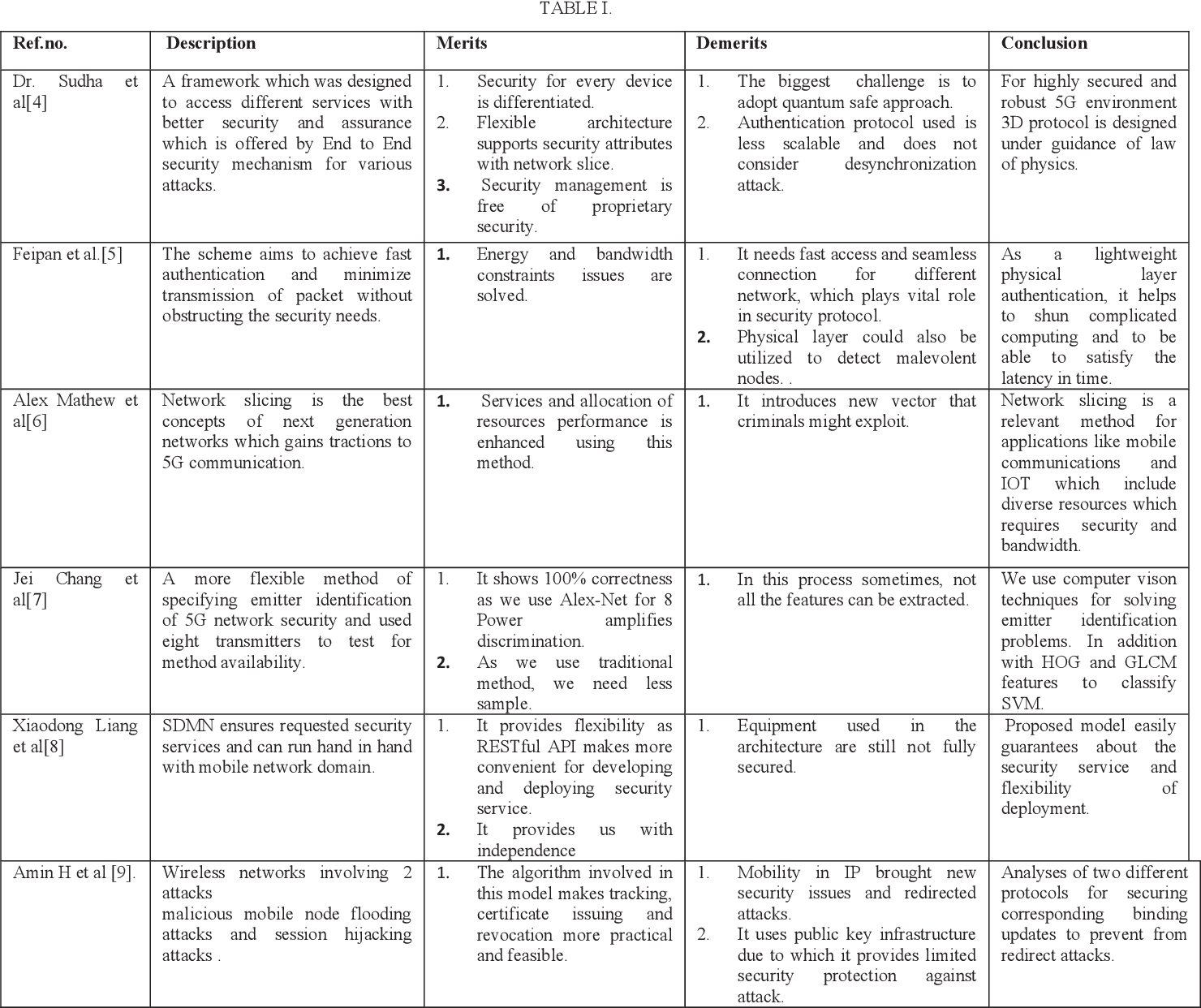
Table I From Comparative Analysis Of 5g Security Mechanisms Semantic This paper provides a concise review of some 5g’s new features, including the service based architecture (sba) and key network functions (nfs), the new security features in user equipment and radio access network (ran), and the new trust model and security mechanisms (e.g. the 5g aka protocol). As networks continue to expand, they become increasingly heterogeneous, accommodating a diverse range of devices, from sensors and iot to clients and servers.

5g Security Pdf Electronics Computer Science The recent development and the existing schemes for the 5g wireless security are presented based on the corresponding security services including authentication, availability, data. We present the informal and formal security analysis techniques used by the authentication and privacy preserving schemes for 4g and 5g cellular networks. With the rapid rollout and growing adoption of 3gpp 5thgeneration (5g) cellular services, including in critical infrastructure sectors, it is important to review security mechanisms, risks, and potential vulnerabilities within this vital technology. This comprehensive survey evaluates various authentication and security mechanisms tailored for 5g networks, highlighting their challenges, opportunities, and the need for innovative solutions to ensure secure and reliable connectivity.

Table Of Contents For 5g And 4g Networks Comparative Analysis Industry Down With the rapid rollout and growing adoption of 3gpp 5thgeneration (5g) cellular services, including in critical infrastructure sectors, it is important to review security mechanisms, risks, and potential vulnerabilities within this vital technology. This comprehensive survey evaluates various authentication and security mechanisms tailored for 5g networks, highlighting their challenges, opportunities, and the need for innovative solutions to ensure secure and reliable connectivity. This survey provides a systematic analysis of 5g security challenges, including zero day vulnerabilities in network slicing, edge computing threats, and ai driven attack surfaces. This work focuses on 5g security issues and highlighting the challenges and proposed solutions, standards, and analysis, in addition to the architecture of 5g network and authentication process of both 4g and 5g. In addition, we provide a taxonomy and comparison of authentication and privacy preserving schemes for 4g and 5g cellular networks in form of tables. based on the current survey, several recommendations for further research are discussed at the end of this paper. Advance product security mechanisms, together with access management, logging, single software track and analytic tools constitute a solid foundation for implementing security policies and operating the network securely.
Comments are closed.