Table 1 From Stealing Complex Network Attack Detection Method
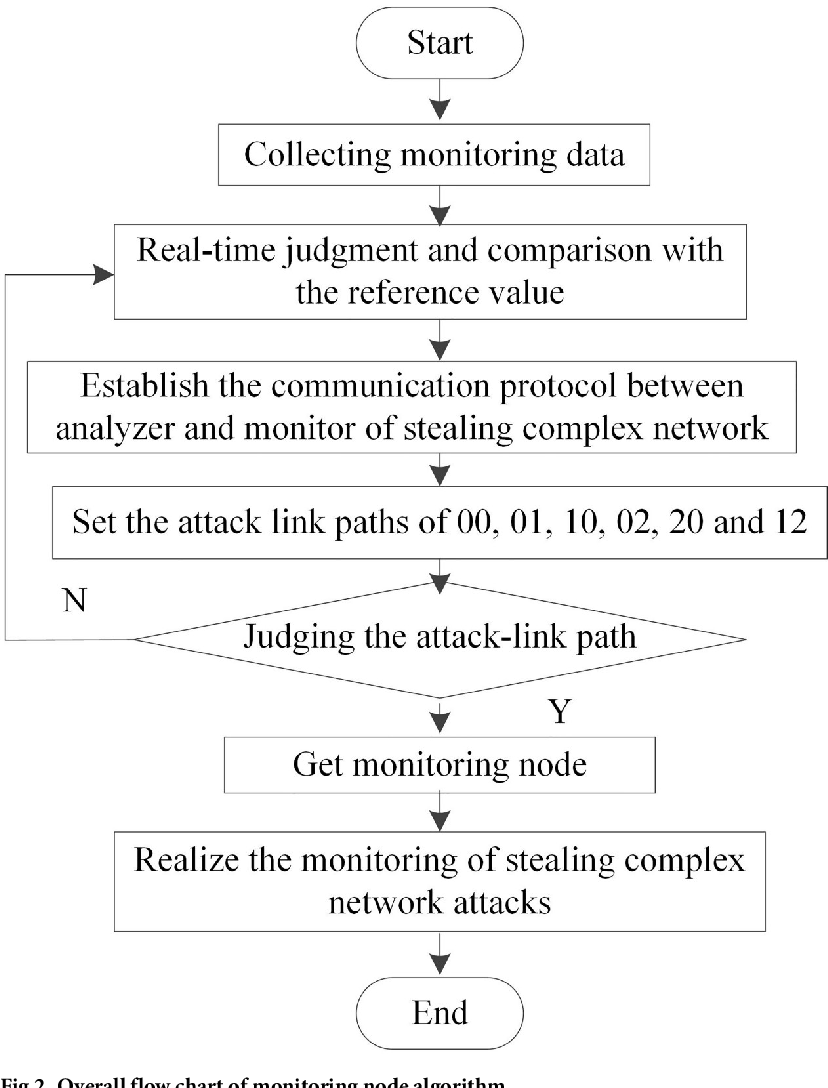
Figure 1 From Stealing Complex Network Attack Detection Method The simulation results show that this method is stable in the range of 1000 to 4000 nodes, and can effectively monitor the complex network attacks of stealing secrets. To further verify the feasibility of the proposed method, experiments are conducted to analyze the accuracy of the proposed method, the detection of stealing complex network attacks based on adaptive immune computation and the detection of sample nodes by the openflow ddos attack detection method.
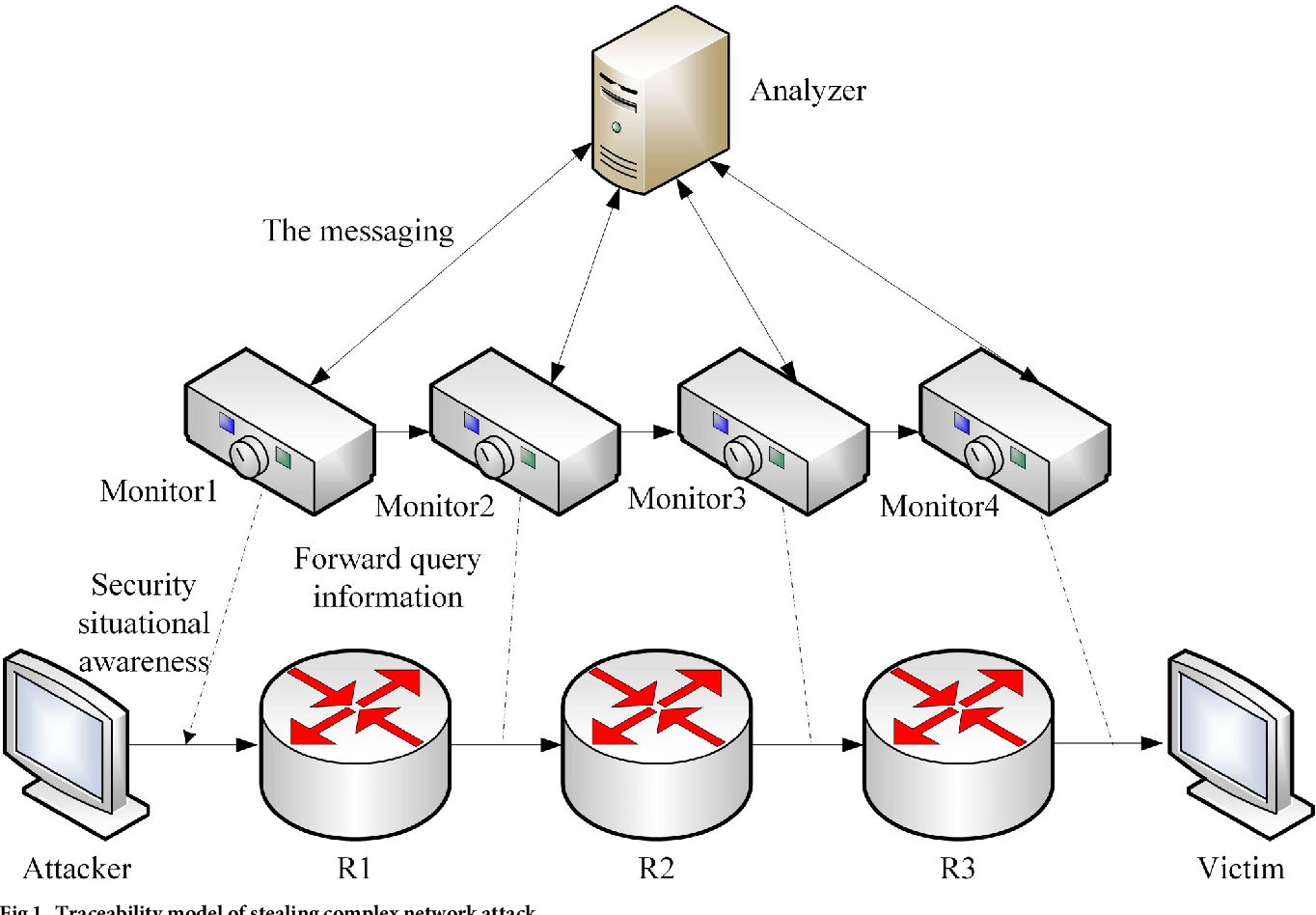
Figure 1 From Stealing Complex Network Attack Detection Method This article proposes and compares three network security situational awareness models and introduces in detail the two model structures of random forest and star. This paper proposes a monitoring method of stealthy complex network attacks considering security situation awareness, and shows that this method is stable in the range of 1000 to 4000 nodes, and can effectively monitor the complex network attacks of stealing secrets. The simulation results show that this method is stable in the range of 1000 to 4000 nodes, and can effectively monitor the complex network attacks of stealing secrets. Article "detection method of stealing complex network attack considering security situation awareness" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst").

Pdf Stealing Complex Network Attack Detection Method Considering The simulation results show that this method is stable in the range of 1000 to 4000 nodes, and can effectively monitor the complex network attacks of stealing secrets. Article "detection method of stealing complex network attack considering security situation awareness" detailed information of the j global is an information service managed by the japan science and technology agency (hereinafter referred to as "jst"). By dynamically adjusting the network topology and capturing multi level attack features, the proposed strategy enables precise identification and classification of complex attack behaviors. Tracking and detection have brought great challenges to network security. therefore, this paper proposes a monitoring method of stealthy complex network attacks considering security situation awareness.
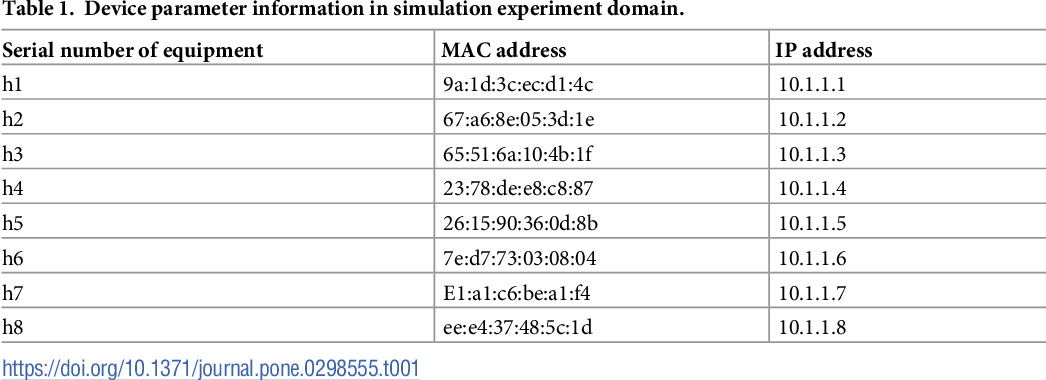
Table 1 From Stealing Complex Network Attack Detection Method By dynamically adjusting the network topology and capturing multi level attack features, the proposed strategy enables precise identification and classification of complex attack behaviors. Tracking and detection have brought great challenges to network security. therefore, this paper proposes a monitoring method of stealthy complex network attacks considering security situation awareness.
Comments are closed.