System Hacking Encoders Hexeditor

How To Crack Programs Using Hex Editor Aslgenerator In the 10th episode of our metasploit tutorial series we will cover how to bypass antiviruses. we will use a website called virustotal run our reverse shell against existing antivirus databases. i. To develop plugins for imhex, use the following template project to get started. you then have access to the entirety of libimhex as well as the imhex api and the content registry to interact with imhex or to add new content. to build a plugin, you will need to use our sdk.
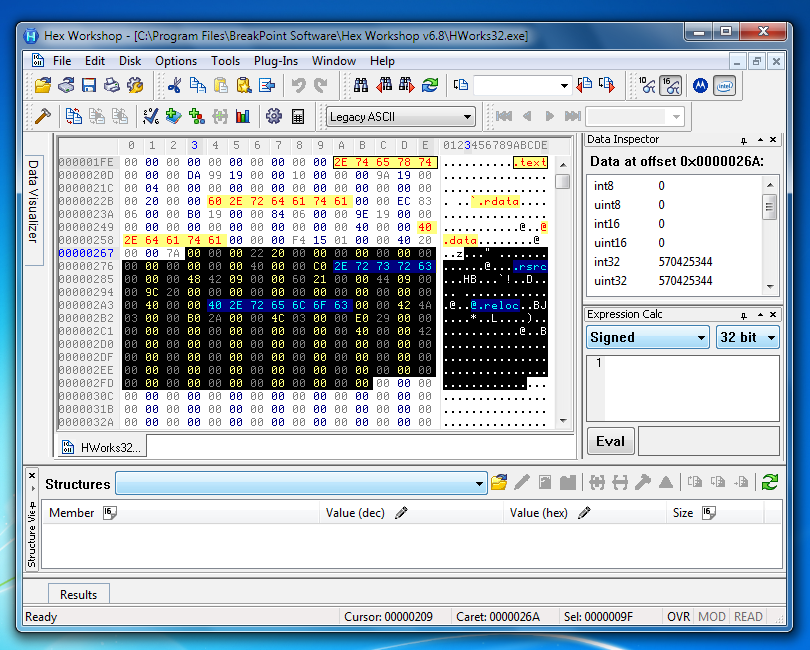
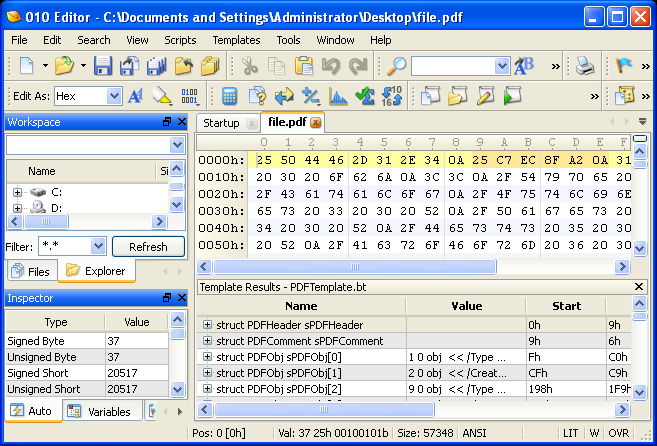
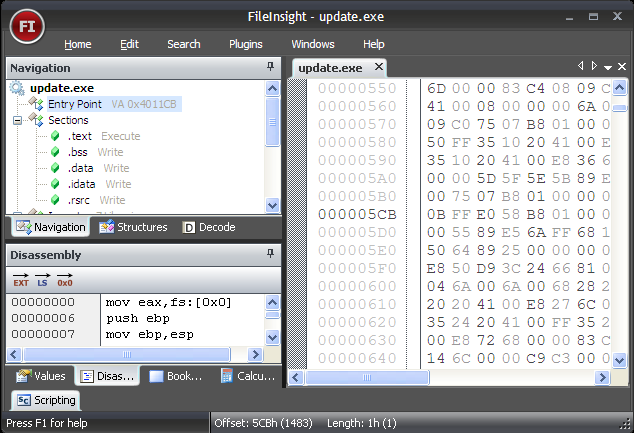
Reverse Engineering Tools Review A hex editor is a specialized tool used to view and manipulate binary data directly at the byte level. unlike regular text editors, which work with human readable characters, hex editors display the raw machine code of files. From writing code to reading config files, the hacker’s world is filled with seemingly infinite lines of ascii. A hex editor is a valuable tool in ethical hacking and password recovery, helping security professionals analyze encrypted data, retrieve lost credentials, and detect vulnerabilities in software. A hex editor for reverse engineers, programmers and people who value their retinas when working at 3 am.

Best Hex Editors For Decompiling Tidecamp A hex editor is a valuable tool in ethical hacking and password recovery, helping security professionals analyze encrypted data, retrieve lost credentials, and detect vulnerabilities in software. A hex editor for reverse engineers, programmers and people who value their retinas when working at 3 am. Learn in demand it skills anytime, anywhere with skillfly. practical, expert led courses designed for career growth and lifelong learning. The video tutorial covers creating and delivering a windows reverse shell payload, using virustotal to check antivirus detection, creating a second payload with encoders, and using hex editing to modify payloads for better antivirus bypass. Towards the end, you’ll grasp the fundamentals of python programming and develop offensive python tools for pen testing and automation. by the end of this course, you’ll have developed all the essentials skills needed for ethical hacking and penetration testing. Unleash your cyber security skills beginning with kali linux installation, footprinting, and nmap scanning in 2019 through coding advanced back doors and bru.
Sans Digital Forensics And Incident Response Blog 6 Hex Editors For Learn in demand it skills anytime, anywhere with skillfly. practical, expert led courses designed for career growth and lifelong learning. The video tutorial covers creating and delivering a windows reverse shell payload, using virustotal to check antivirus detection, creating a second payload with encoders, and using hex editing to modify payloads for better antivirus bypass. Towards the end, you’ll grasp the fundamentals of python programming and develop offensive python tools for pen testing and automation. by the end of this course, you’ll have developed all the essentials skills needed for ethical hacking and penetration testing. Unleash your cyber security skills beginning with kali linux installation, footprinting, and nmap scanning in 2019 through coding advanced back doors and bru.
Sans Digital Forensics And Incident Response Blog 6 Hex Editors For Towards the end, you’ll grasp the fundamentals of python programming and develop offensive python tools for pen testing and automation. by the end of this course, you’ll have developed all the essentials skills needed for ethical hacking and penetration testing. Unleash your cyber security skills beginning with kali linux installation, footprinting, and nmap scanning in 2019 through coding advanced back doors and bru.
Comments are closed.