Switch Attacks Mac Flooding And Mac Spoofing

How Do Mac Spoofing Attacks Work In this tutorial, we looked over how a switched lan network works, and we saw how a mac flooding and a mac spoofing attack works. we discussed what the attacker could achieve and how network administrators can mitigate these attacks. When a mac flooding attack occurs: the table becomes overwhelmed by the sheer number of spoofed mac addresses. once full, the switch can no longer map new mac addresses to ports. incoming packets are broadcast to all ports, allowing any device in the network to intercept the traffic.
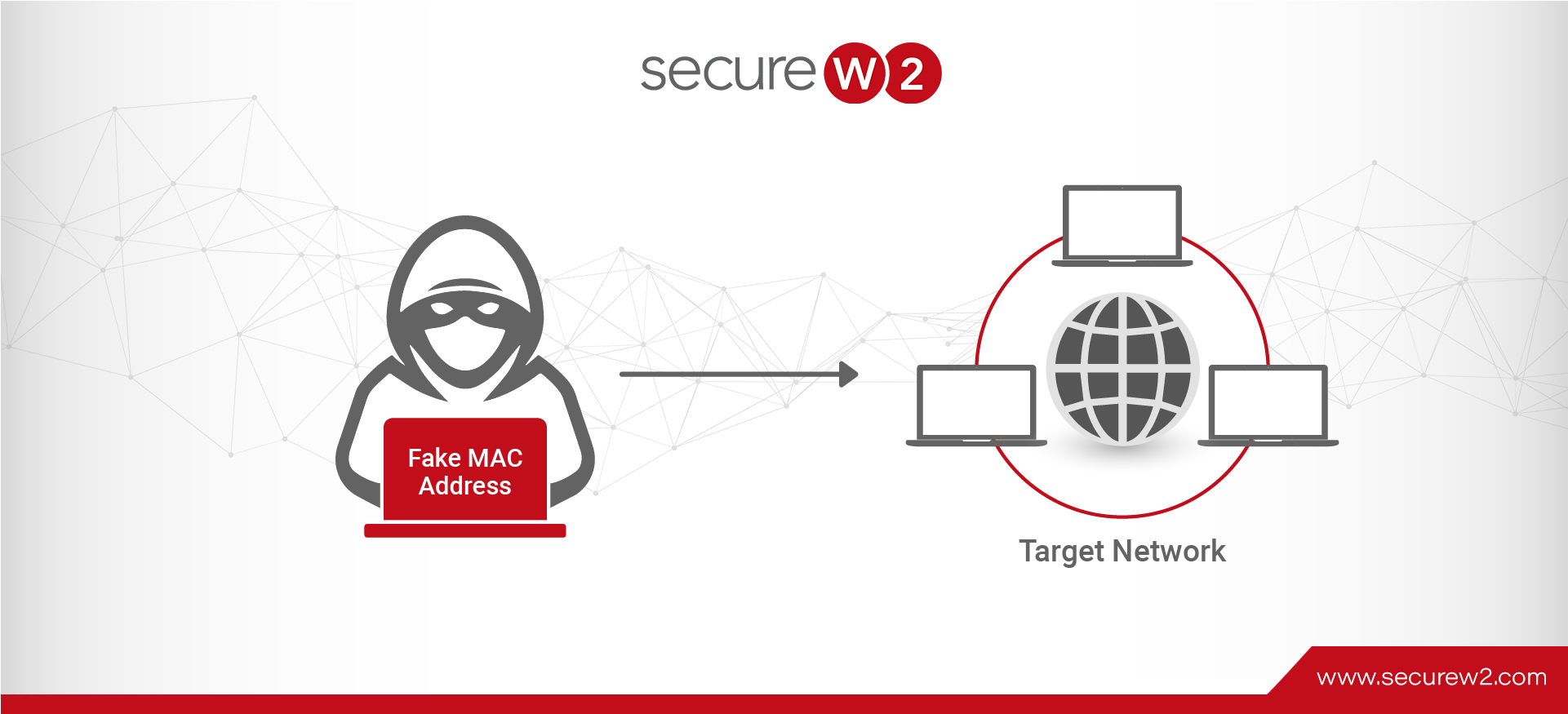
Mac Spoofing Attacks Explained A Technical Overview In computer networking, a media access control attack or mac flooding is a technique employed to compromise the security of network switches. the attack works by forcing legitimate mac table contents out of the switch and forcing a unicast flooding behavior, potentially sending sensitive information to portions of the network where it is not. Learn what mac flooding is, how attackers exploit it to overwhelm network switches, and the steps you can take to detect and prevent this network security threat. This chapter covers two common attacks against a switch. our gns3 test environment is not designed to withstand this attack, but you will learn the fundamentals of cam flooding and arp spoofing. In this article, we’ll look at the common layer 2 attack types, evaluate their relevance today, and explore how switch features like dynamic mac learning and port security help mitigate them.
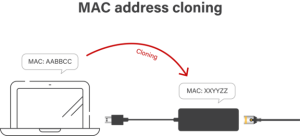
Mac Spoofing Attacks Explained A Technical Overview This chapter covers two common attacks against a switch. our gns3 test environment is not designed to withstand this attack, but you will learn the fundamentals of cam flooding and arp spoofing. In this article, we’ll look at the common layer 2 attack types, evaluate their relevance today, and explore how switch features like dynamic mac learning and port security help mitigate them. The detection: if an attacker spoofs a victim’s mac on a different switch port, the switch will see the mac “flapping” between port a and port b rapidly. this causes a massive cpu spike on the switch and generates specific syslog error messages. This repository explores layer 2 network attacks, including mac flooding, arp spoofing, and man in the middle (mitm) attacks. it covers methodologies, tools used, and mitigation techniques based on practical exercises from the tryhackme layer2 room. A mac flooding attack is a type of denial of service attack in which an attacker sends a large number of spoofed mac addresses to fill the cam table of a switch. A mac flooding attack, also known as a mac table overflow attack, is a type of network security attack that targets network switches. it involves overwhelming a switch’s mac address table by flooding it with a massive amount of spoofed ethernet frames, each containing a unique source mac address.
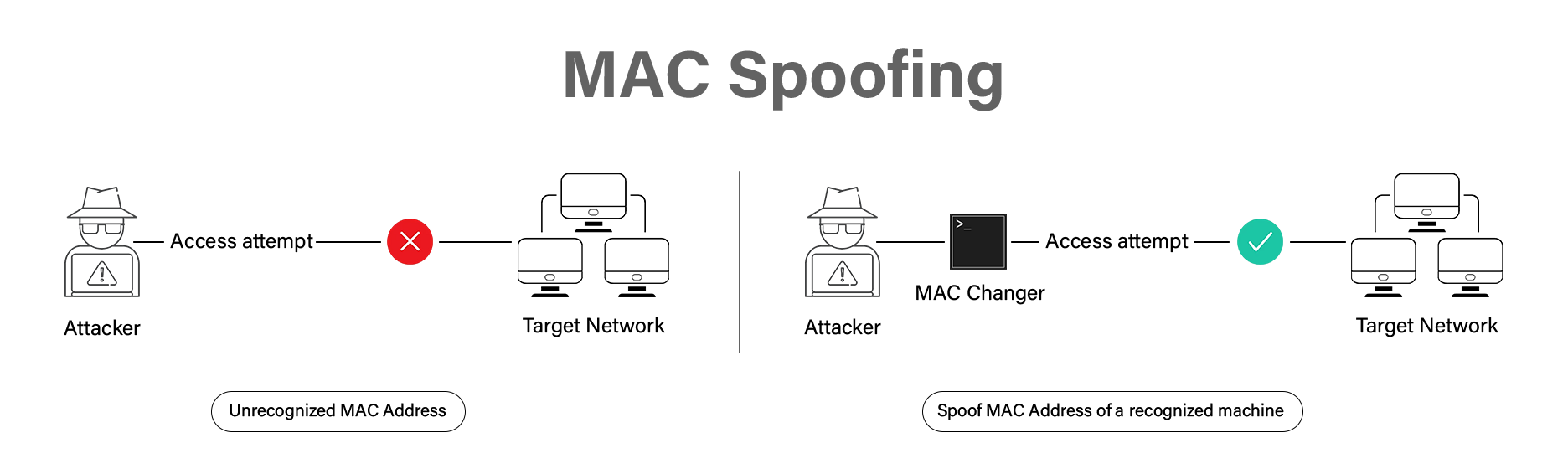
Mac Spoofing Attacks Explained A Technical Overview The detection: if an attacker spoofs a victim’s mac on a different switch port, the switch will see the mac “flapping” between port a and port b rapidly. this causes a massive cpu spike on the switch and generates specific syslog error messages. This repository explores layer 2 network attacks, including mac flooding, arp spoofing, and man in the middle (mitm) attacks. it covers methodologies, tools used, and mitigation techniques based on practical exercises from the tryhackme layer2 room. A mac flooding attack is a type of denial of service attack in which an attacker sends a large number of spoofed mac addresses to fill the cam table of a switch. A mac flooding attack, also known as a mac table overflow attack, is a type of network security attack that targets network switches. it involves overwhelming a switch’s mac address table by flooding it with a massive amount of spoofed ethernet frames, each containing a unique source mac address.
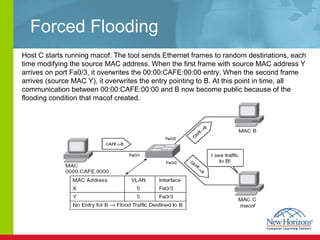
Mac Address Flooding Attack Tool Lasopaline A mac flooding attack is a type of denial of service attack in which an attacker sends a large number of spoofed mac addresses to fill the cam table of a switch. A mac flooding attack, also known as a mac table overflow attack, is a type of network security attack that targets network switches. it involves overwhelming a switch’s mac address table by flooding it with a massive amount of spoofed ethernet frames, each containing a unique source mac address.
Mac Address Flooding Attack Tool Nanaxroom
Comments are closed.