Swagshop Htb Livewalkthrough
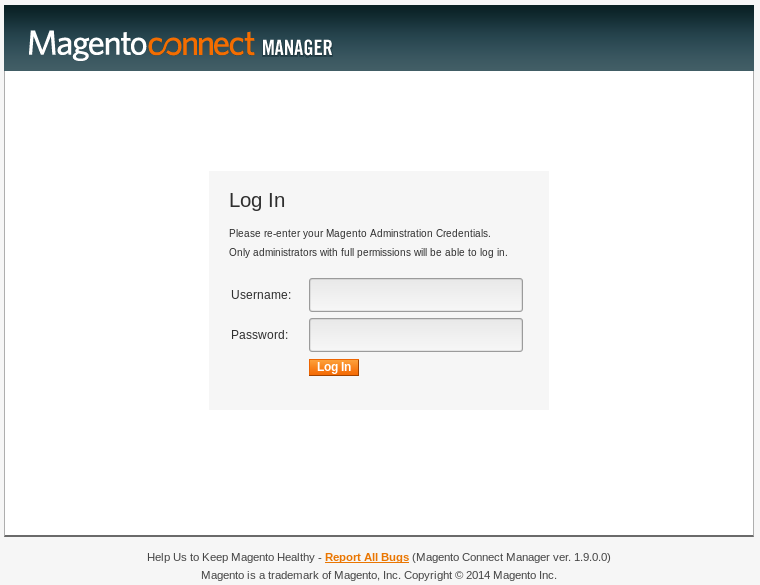
Swagshop Hipotermia This is me thomasthecat a noob cyber security enthusiast solving tryhackme, hackthebox etc various ctf in raw format with no pre preparation. may ran into ra. Swagshop was an easy box that involved a magneto store web server. i start off by exploiting an authentication bypass to add an admin user to the cms. i then used an authenticated exploitation of a php object injection vulnerability to get rce. i was able to then use vi to privesc to gain root level access.
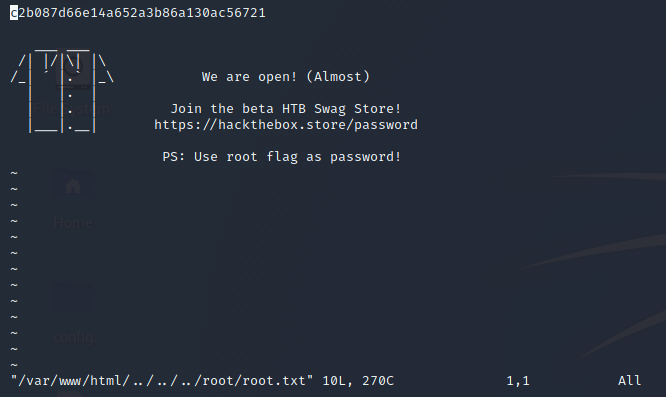
Hackthebox Swagshop Amirr0r This post documents my walkthrough of the swagshop machine from hack the box. the machine exploits vulnerabilities in a magento 1.9 web application to gain initial access. Swagshop was a nice beginner easy box centered around a magento online store interface. i’ll use two exploits to get a shell. the first is an authentication bypass that allows me to add an admin user to the cms. then i can use an authenticated php object injection to get rce. i’ll also show how got rce with a malicious magento package. Walkthrough of hack the box's swagshop machine, covering web exploitation, rce via magento, and privilege escalation to root. So, we add swagshop.htb with its ip address into the etc hosts file as shown below. now, we decide to enumerate the http service on the target machine. as soon as we open it, we see that it is an e commerce based template on magento framework.
Github Jebidiah Anthony Htb Swagshop Htb Swagshop 10 10 10 140 Walkthrough of hack the box's swagshop machine, covering web exploitation, rce via magento, and privilege escalation to root. So, we add swagshop.htb with its ip address into the etc hosts file as shown below. now, we decide to enumerate the http service on the target machine. as soon as we open it, we see that it is an e commerce based template on magento framework. Swagshop is an easy real life machine based on linux. we get the user shell by exploiting the ecommerce web application magento, and we drop root by noticing that our basic user can run a usual text editor as root. These writeups will explain my steps to completion, along with the tools and techniques that i used. the machines that i have chose to complete are from the tj null spread sheet, and are. 🚩 new blog post – htb swagshop walkthrough 🛠️ just published a new write up on the swagshop machine from hack the box!. From the magescan report, if we find about patches, the first one is supee 5344. with this poc, you should be able to add an admin user. access to swagshop.htb index admin. after reading this blog post we can follow this procedure to obtain a user level reverse shell.
Comments are closed.