Supply Chain Security With Go
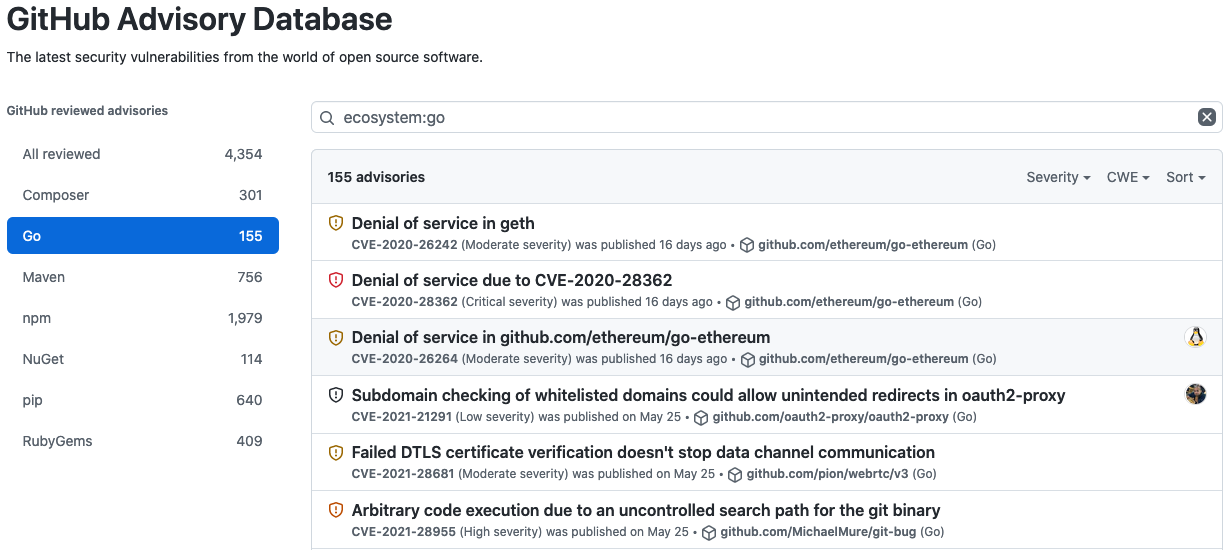
Github Brings Supply Chain Security Features To The Go Community The It is an explicit security design goal of the go toolchain that neither fetching nor building code will let that code execute, even if it is untrusted and malicious. Our previous installment of the supply chain security for go series shared the ecosystem tools available to go developers to manage their dependencies and vulnerabilities. this second installment describes the ways that go helps you trust the integrity of a go package.

Supply Chain Security Nattytech Our work provides preliminary insights for securing the open source software supply chain within the go ecosystem, allowing developers and security analysts to prioritize code audit eforts and uncover hidden malicious behaviors. Today, we're going to discuss software supply chain security: what it is, why it matters, and how the tools we provide with the go programming language can help you secure your software supply chain at every stage of the software development lifecycle. The final and maybe most important software supply chain risk mitigation in the go ecosystem is the least technical one: go has a culture of rejecting large dependency trees, and of preferring a bit of copying to adding a new dependency. By embracing go and implementing these complementary security measures, organizations can significantly reduce their risk of falling victim to supply chain attacks and build more secure and resilient software systems.

Supply Chain Security Framework S2c2f The final and maybe most important software supply chain risk mitigation in the go ecosystem is the least technical one: go has a culture of rejecting large dependency trees, and of preferring a bit of copying to adding a new dependency. By embracing go and implementing these complementary security measures, organizations can significantly reduce their risk of falling victim to supply chain attacks and build more secure and resilient software systems. By 2025, the growing reliance on go modules, ci tools, and containerization will make go ecosystems more attractive to cybercriminals looking to exploit the growing attack surface. let’s explore the biggest threats and how you can secure your go based ci cd pipelines against them. 1. the rise of go modules. Our work provides preliminary insights for securing the open source software supply chain within the go ecosystem, allowing developers and security analysts to prioritize code audit efforts and uncover hidden malicious behaviors. This talk tries to answer that question for various common scenarios, explaining the roles of the various technologies and services (like the go module proxy or go checksum database). the recent xz vulnerability brought the topic of supply chain security to everyone’s attention. Discover why recent security updates for the go programming language are critical in preventing devastating supply chain attacks, and how developers can stay ahead of cyber threats.

Supply Chain Security How Software Complements Human Efforts By 2025, the growing reliance on go modules, ci tools, and containerization will make go ecosystems more attractive to cybercriminals looking to exploit the growing attack surface. let’s explore the biggest threats and how you can secure your go based ci cd pipelines against them. 1. the rise of go modules. Our work provides preliminary insights for securing the open source software supply chain within the go ecosystem, allowing developers and security analysts to prioritize code audit efforts and uncover hidden malicious behaviors. This talk tries to answer that question for various common scenarios, explaining the roles of the various technologies and services (like the go module proxy or go checksum database). the recent xz vulnerability brought the topic of supply chain security to everyone’s attention. Discover why recent security updates for the go programming language are critical in preventing devastating supply chain attacks, and how developers can stay ahead of cyber threats.
Comments are closed.