Student Artifact Analysis Assignment 5 Computerscienceblog
Student Artifact Analysis Assignment 5 Computerscienceblog In the first code, the student initialized 4 homework assignments, three quizzes and one final exam along with the average time spent in minutes a week on the course. the code then converts minutes to hours and minutes using integer division and modulus. This assignment focuses on the analysis of digital artifacts in windows and linux operating systems, as well as internet browser artifacts. it emphasizes the importance of digital forensics in crime investigations and requires the exploration of forensic tools, including documentation and citations in harvard style.

Assignment 3 Pdf Software Development Computer Science Investigate critical windows artifacts for forensic evidence. demonstrate step by step methodologies for analyzing logs, registries, file systems, and browser data. provide reproducible forensic workflows that can be applied in lab environments or real world cases. When analyzing a multipart forensic image file, you only need to add point to the first (*.e01) file, and make sure all the image files are together in one folder. The document summarizes various artifacts found on windows systems that can provide evidence of a user's activities. it describes artifacts from file downloads, email attachments, skype chat logs, browser histories, software installed and used on the system, documents opened, and programs and files recently run. Part 1: explore different approaches & share replies: the first person’s artifact analysis that i looked through was matt’s. the comment i left him is below the second person’s artifact for assignment 5 was thomas’s.

Artifact Analysis 5 More Than Math The document summarizes various artifacts found on windows systems that can provide evidence of a user's activities. it describes artifacts from file downloads, email attachments, skype chat logs, browser histories, software installed and used on the system, documents opened, and programs and files recently run. Part 1: explore different approaches & share replies: the first person’s artifact analysis that i looked through was matt’s. the comment i left him is below the second person’s artifact for assignment 5 was thomas’s. Part 1: explore different approaches & share replies: the first person’s artifact analysis that i looked through was matt’s. the comment i left him is below the second person’s artifact for assignment 5 was thomas’s. They might see their peers that can’t get the homework done as lazy but the hope of the assignment is to put yourself in their shoes and see how different grading practices would affect different students. I also moved the chomp sound effect to outside the check so it won’t run forever. posted in uncategorized previous:student artifact – analysis – assignment 4 next:student artifact – analysis – assignment 5 computerscienceblog. Part 1: analyze student thinking “cookies and conversation” in “cookies and conversation”, the code is organized in chronological order using one sprite, its costume changes, and a sound recording between each costume switch.
Lab Browser Artifact Analysis Cst 640 Study Guides Ethical Learning Part 1: explore different approaches & share replies: the first person’s artifact analysis that i looked through was matt’s. the comment i left him is below the second person’s artifact for assignment 5 was thomas’s. They might see their peers that can’t get the homework done as lazy but the hope of the assignment is to put yourself in their shoes and see how different grading practices would affect different students. I also moved the chomp sound effect to outside the check so it won’t run forever. posted in uncategorized previous:student artifact – analysis – assignment 4 next:student artifact – analysis – assignment 5 computerscienceblog. Part 1: analyze student thinking “cookies and conversation” in “cookies and conversation”, the code is organized in chronological order using one sprite, its costume changes, and a sound recording between each costume switch.

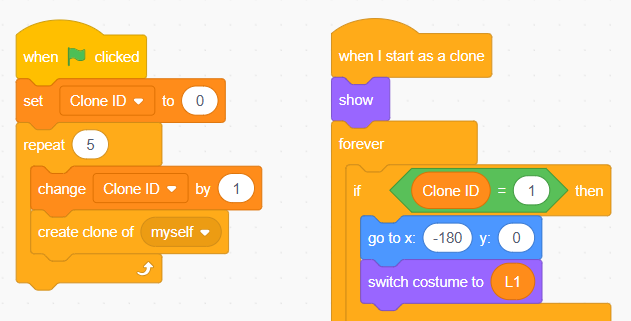
Assignment Pdf I also moved the chomp sound effect to outside the check so it won’t run forever. posted in uncategorized previous:student artifact – analysis – assignment 4 next:student artifact – analysis – assignment 5 computerscienceblog. Part 1: analyze student thinking “cookies and conversation” in “cookies and conversation”, the code is organized in chronological order using one sprite, its costume changes, and a sound recording between each costume switch.

Assignment 211 5 Pdf Applied Mathematics Theoretical Computer
Comments are closed.