Strengthening The Software Supply Chain With Sbom 103 3 The Vibe

Strengthening The Software Supply Chain With Sbom 103 3 The Vibe In addition to preventing organizational information, digital infrastructure, and customer data from being compromised, sbom can also improve the overall quality of the software used by companies. These guidelines contain detailed information on minimum sbom requirements, software security vulnerability inspection criteria, the use of government supported test beds, and how to specify and utilize software components.
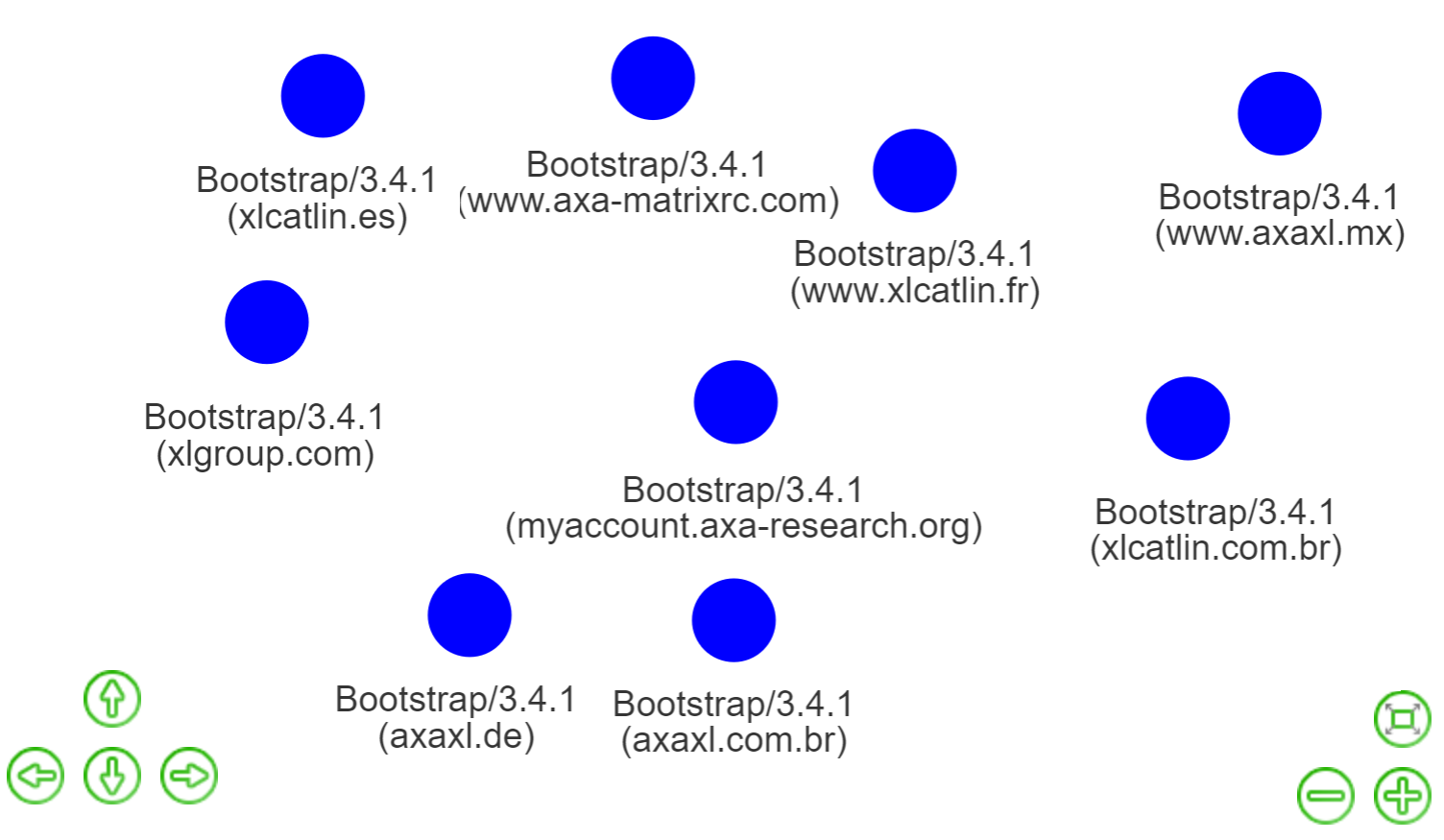
Rankiteo Sbom Supply Chain Analytics For Enhanced Software Security These guidelines contain detailed information on minimum sbom requirements, software security vulnerability inspection criteria, the use of government supported test beds, and how to specify and utilize software components. To prevent and defend against cyberattacks, various efforts are being made to ramp up software supply chain security, particularly in the u.s. and europe. This guide provides information on the benefits of sbom, common misconceptions and concerns, creation of an sbom, distributing and sharing an sbom, and role specific guidance. In addition to preventing organizational information, digital infrastructure, and customer data from being compromised, sbom can also improve the overall quality of the software used by companies.

Executive Corner Strengthening The Software Supply Chain With Sbom This guide provides information on the benefits of sbom, common misconceptions and concerns, creation of an sbom, distributing and sharing an sbom, and role specific guidance. In addition to preventing organizational information, digital infrastructure, and customer data from being compromised, sbom can also improve the overall quality of the software used by companies. Accordingly, vendor responsibilities include ensuring the integrity and security of software via contractual agreements, software releases and updates, notifications, and mitigations of vulnerabilities. this guidance contains recommended best practices and standards to aid customers in these tasks. The addition of vex data helps practitioners quickly assess whether vulnerabilities in their software supply chain components are known to affect their systems, thereby improving the suitability and usability of sbom based security workflows. This article unpacks what an sbom is, why it matters across every phase of the software supply chain, and how to turn it into your secret weapon for resilience, visibility, and peace of mind.

Executive Corner Strengthening The Software Supply Chain With Sbom Accordingly, vendor responsibilities include ensuring the integrity and security of software via contractual agreements, software releases and updates, notifications, and mitigations of vulnerabilities. this guidance contains recommended best practices and standards to aid customers in these tasks. The addition of vex data helps practitioners quickly assess whether vulnerabilities in their software supply chain components are known to affect their systems, thereby improving the suitability and usability of sbom based security workflows. This article unpacks what an sbom is, why it matters across every phase of the software supply chain, and how to turn it into your secret weapon for resilience, visibility, and peace of mind.
Comments are closed.