Stream Ciphers Encryption Decryption

Stream Ciphers 3 Pdf Cipher Encryption A block cipher and a stream cipher vary primarily in that a block cipher takes one block of plain text at a time and transforms it into ciphertext. while the stream cipher takes one byte of normal text at a time and converts it into cipher text. In a stream cipher, each plaintext digit is encrypted one at a time with the corresponding digit of the keystream, to give a digit of the ciphertext stream. since encryption of each digit is dependent on the current state of the cipher, it is also known as state cipher.
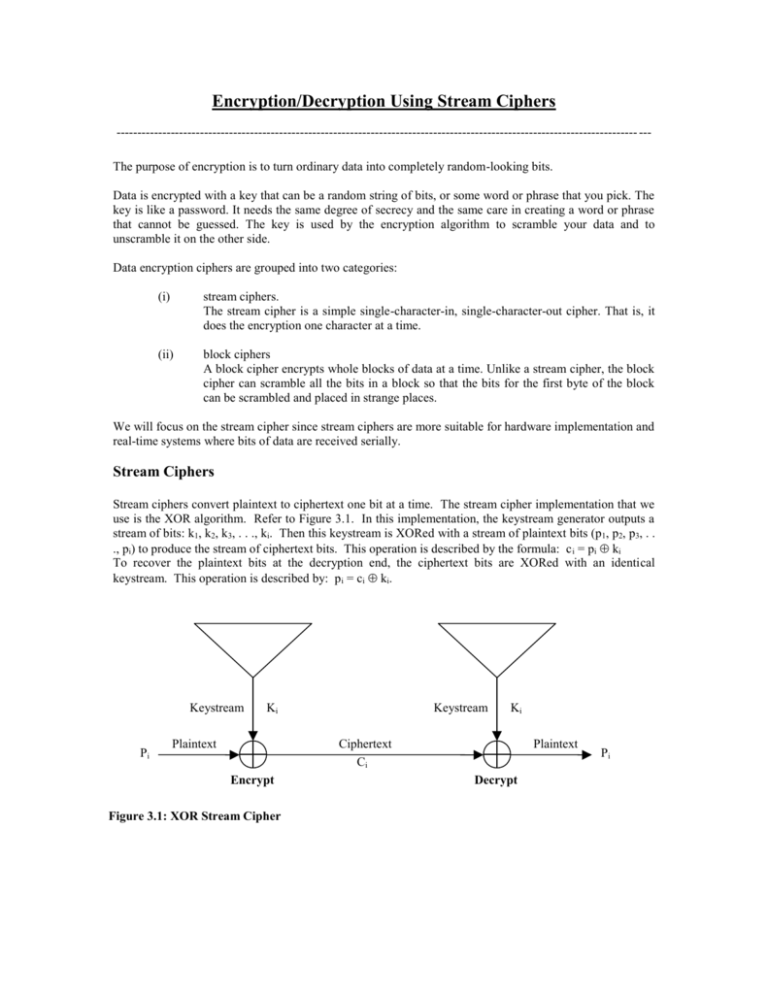
Encryption Decryption Using Stream Ciphers Speedy encryption and decryption: stream ciphers encrypt and decrypt data at single bit or byte speeds, making them ideal for real time communication and demanding applications. If we look at the types of cryptographic algorithms that exist in a little bit more detail, we see that the symmetric ciphers can be divided into stream ciphers and block ciphers, as shown in fig. 2.1. Stream ciphers are usually designed so that each encrypted bit depends on all previously encrypted ones, so decryption becomes possible only if all the bits arrive in order; most true stream ciphers lack the random access property. In this article you’ll learn exactly how stream ciphers work—breaking them down into three simple pieces—before we dive into real world examples like rc4 and chacha20 in the next installments. before zooming into its three parts, here’s the big picture of encrypting and decrypting a single message:.
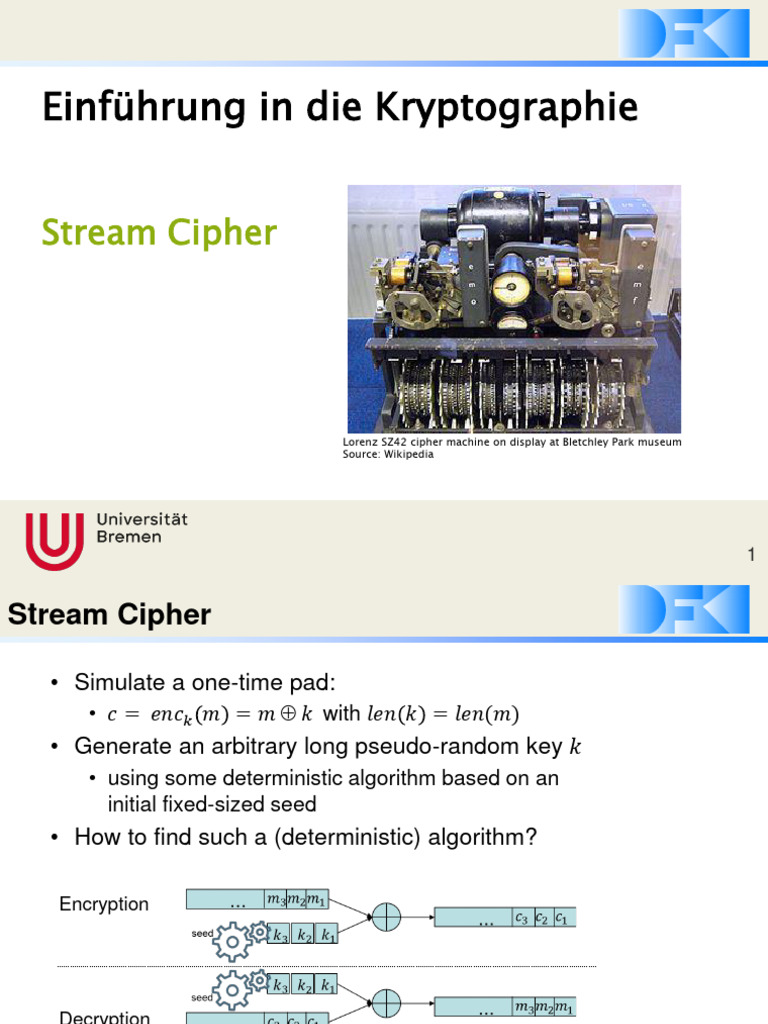
Stream Cipher Pdf Cryptography Computer Science Stream ciphers are usually designed so that each encrypted bit depends on all previously encrypted ones, so decryption becomes possible only if all the bits arrive in order; most true stream ciphers lack the random access property. In this article you’ll learn exactly how stream ciphers work—breaking them down into three simple pieces—before we dive into real world examples like rc4 and chacha20 in the next installments. before zooming into its three parts, here’s the big picture of encrypting and decrypting a single message:. An important distinction in symmetric cryptographic algorithms is between stream and block ciphers. stream ciphers convert one symbol of plaintext directly into a symbol of ciphertext. block ciphers encrypt a group of plaintext symbols as one block. simple substitution is an example of a stream cipher. columnar transposition is a block cipher. A stream cipher is an encryption algorithm that uses a symmetric key to encrypt and decrypt a given amount of data. this key also known as a keystream since it is a set of random characters that replaces the characters in the plaintext is shared by the participants in a transaction for encryption and decryption. Stream ciphers are symmetric ciphers that encrypt and decrypt bits individually. they are used to secure communications in wireless and cellular networks. stream ciphers are well‐suited to hardware implementation and they are generally faster than block ciphers. Unlike block ciphers, stream ciphers work on single bits or single words and need to maintain an internal state to change the cipher at each step. typically stream ciphers can reach higher speeds than block ciphers but they can be more vulnerable to attack.

Stream Cipher Pdf Encryption Cryptography An important distinction in symmetric cryptographic algorithms is between stream and block ciphers. stream ciphers convert one symbol of plaintext directly into a symbol of ciphertext. block ciphers encrypt a group of plaintext symbols as one block. simple substitution is an example of a stream cipher. columnar transposition is a block cipher. A stream cipher is an encryption algorithm that uses a symmetric key to encrypt and decrypt a given amount of data. this key also known as a keystream since it is a set of random characters that replaces the characters in the plaintext is shared by the participants in a transaction for encryption and decryption. Stream ciphers are symmetric ciphers that encrypt and decrypt bits individually. they are used to secure communications in wireless and cellular networks. stream ciphers are well‐suited to hardware implementation and they are generally faster than block ciphers. Unlike block ciphers, stream ciphers work on single bits or single words and need to maintain an internal state to change the cipher at each step. typically stream ciphers can reach higher speeds than block ciphers but they can be more vulnerable to attack.

1 Stream Cipher Based Encryption And Decryption Download Scientific Stream ciphers are symmetric ciphers that encrypt and decrypt bits individually. they are used to secure communications in wireless and cellular networks. stream ciphers are well‐suited to hardware implementation and they are generally faster than block ciphers. Unlike block ciphers, stream ciphers work on single bits or single words and need to maintain an internal state to change the cipher at each step. typically stream ciphers can reach higher speeds than block ciphers but they can be more vulnerable to attack.

1 Stream Cipher Based Encryption And Decryption Download Scientific
Comments are closed.