Strategies For Minimizing Cyber Security Risks
Steps To Create Cyber Security Strategies Cyber Attack Risks Mitigation Explore a comprehensive guide to cybersecurity risk management, top strategies, and best practices. learn how to identify, assess, and mitigate risks to improve security posture of your organization. Learn about top cyber risk mitigation strategies, key challenges, and best practices.

Cybersecurity Strategies To Manage Cyber Risks Ppt Infographic Template Gra Protect your business from cyber threats with proactive risk management. learn to identify, evaluate and mitigate security vulnerabilities. With that in mind, we’re offering 10 ways your organization can approach, consider and implement effective cybersecurity risk mitigation strategies to keep your critical systems safe. Here are 10 strategies that you should implement to reduce cybersecurity risk for your organization. Explore the essentials of risk reduction in cyber security and learn how to proactively protect your organization. uncover strategies for minimizing vulnerabilities, strengthening defenses, and implementing best practices to lower potential cyber threats and ensure robust digital security.

Minimizing Cyber Security Risks Powerpoint Presentation And Slides Here are 10 strategies that you should implement to reduce cybersecurity risk for your organization. Explore the essentials of risk reduction in cyber security and learn how to proactively protect your organization. uncover strategies for minimizing vulnerabilities, strengthening defenses, and implementing best practices to lower potential cyber threats and ensure robust digital security. Cyber threats are constantly evolving, and businesses need effective strategies to stay secure. this article explores key methods to reduce cyber risks, from implementing zero trust—where every access request is verified—to using automated tools that strengthen your defenses. With that in mind, we’re offering 10 ways your organization can approach, consider and implement effective cybersecurity risk mitigation strategies to keep your critical systems safe. This comprehensive guide explores the concept of risk mitigation in cyber security, why it matters, the 4 types of risk mitigation, proven risk mitigation strategies, and a real world risk mitigation example. To help organizations fortify existing plans, the national security agency (nsa) has a list of recommendations and best practices for mitigating cyberattacks. these 12 cybersecurity strategies can serve as a foundation for your mitigation plan and strengthen your security protocols.
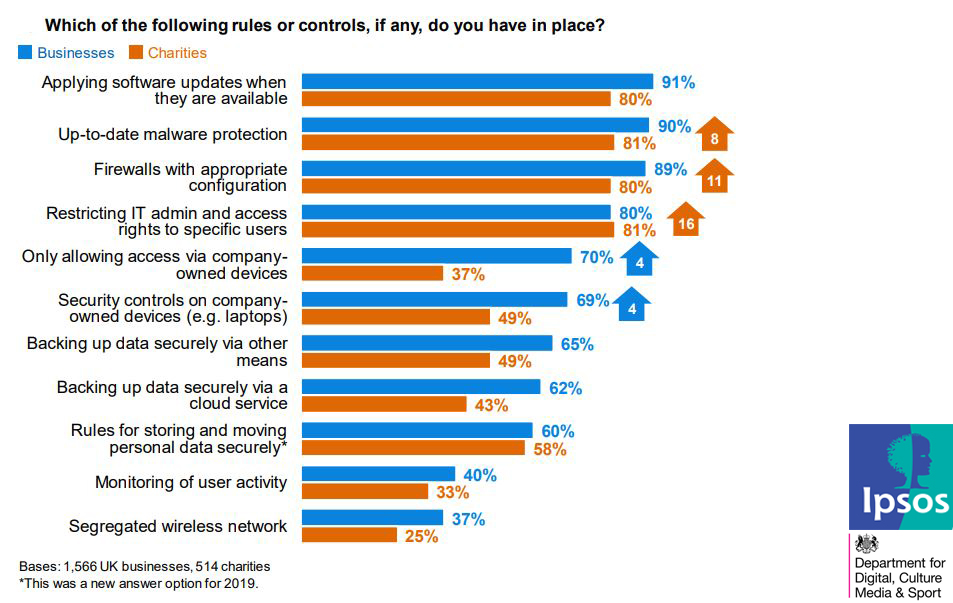
The Most Taken Actions For Preventing Cyber Security Risks 2019 Cyber threats are constantly evolving, and businesses need effective strategies to stay secure. this article explores key methods to reduce cyber risks, from implementing zero trust—where every access request is verified—to using automated tools that strengthen your defenses. With that in mind, we’re offering 10 ways your organization can approach, consider and implement effective cybersecurity risk mitigation strategies to keep your critical systems safe. This comprehensive guide explores the concept of risk mitigation in cyber security, why it matters, the 4 types of risk mitigation, proven risk mitigation strategies, and a real world risk mitigation example. To help organizations fortify existing plans, the national security agency (nsa) has a list of recommendations and best practices for mitigating cyberattacks. these 12 cybersecurity strategies can serve as a foundation for your mitigation plan and strengthen your security protocols.
Comments are closed.