Steps To Implement Zero Trust Network Access Model Zero Trust Security

Steps To Implement Zero Trust Network Access Model Zero Trust Network Secur As attackers become more sophisticated, companies need more powerful security. learn how to implement zero trust to keep operations secure. Our guide on how to implement zero trust security breaks down core principles, key components, and best practices for building a modern security framework.

Zero Trust Network Access Steps To Implement Zero Trust Network Access Mode Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. Zero trust implementation typically includes at least five steps, which include adding microsegmentation to the network, adding multi factor authentication, and validating endpoint devices. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. Explore a step by step guide on implementing zero trust, covering deployment principles, challenges, and best practices for effective implementation.

Zero Trust Model Steps To Implement Zero Trust Network Access Model Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. Explore a step by step guide on implementing zero trust, covering deployment principles, challenges, and best practices for effective implementation. Organizations must adopt a zero trust security model, one that assumes no user or device is inherently trustworthy, even inside the network. in this guide, we break down the key principles of zero trust, steps to implement it, and how swimlane helps automate and scale zero trust strategies. Learn how to build a zero trust network with our step by step guide. discover the best practices for secure access & data protection. Once you have completed the five step methodology for implementing a zero trust network for your first protect surface, you can expand to iteratively move other data, applications, assets or services from your legacy network to a zero trust network in a way that is cost effective and non disruptive. Seven practical steps to implement zero trust network security in your small business powered by the original gartner report. hands on tips to adopt and win the zero trust culture.
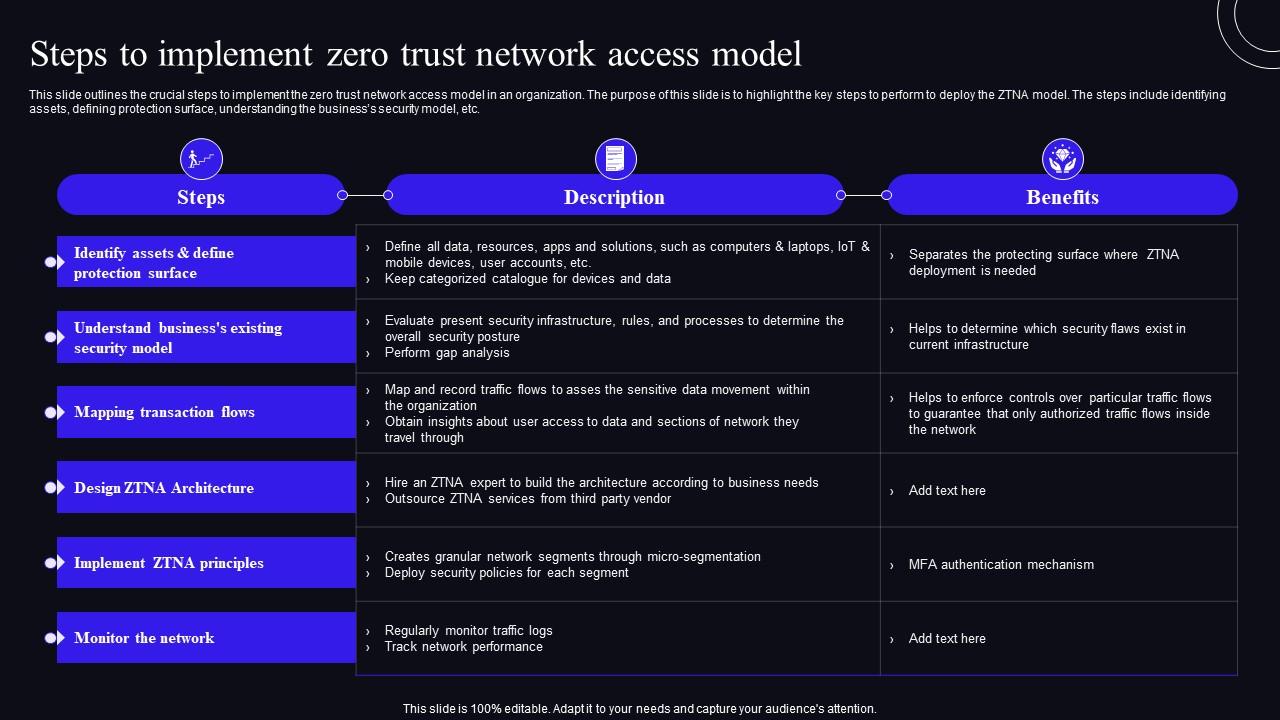
Steps To Implement Zero Trust Network Access Model Zero Trust Security Organizations must adopt a zero trust security model, one that assumes no user or device is inherently trustworthy, even inside the network. in this guide, we break down the key principles of zero trust, steps to implement it, and how swimlane helps automate and scale zero trust strategies. Learn how to build a zero trust network with our step by step guide. discover the best practices for secure access & data protection. Once you have completed the five step methodology for implementing a zero trust network for your first protect surface, you can expand to iteratively move other data, applications, assets or services from your legacy network to a zero trust network in a way that is cost effective and non disruptive. Seven practical steps to implement zero trust network security in your small business powered by the original gartner report. hands on tips to adopt and win the zero trust culture.

Roadmap To Implement Zero Trust Network Access Model Zero Trust Network Once you have completed the five step methodology for implementing a zero trust network for your first protect surface, you can expand to iteratively move other data, applications, assets or services from your legacy network to a zero trust network in a way that is cost effective and non disruptive. Seven practical steps to implement zero trust network security in your small business powered by the original gartner report. hands on tips to adopt and win the zero trust culture.
Comments are closed.