Step 2 Choose Zero Trust Implementation On Ramp Identity Defined
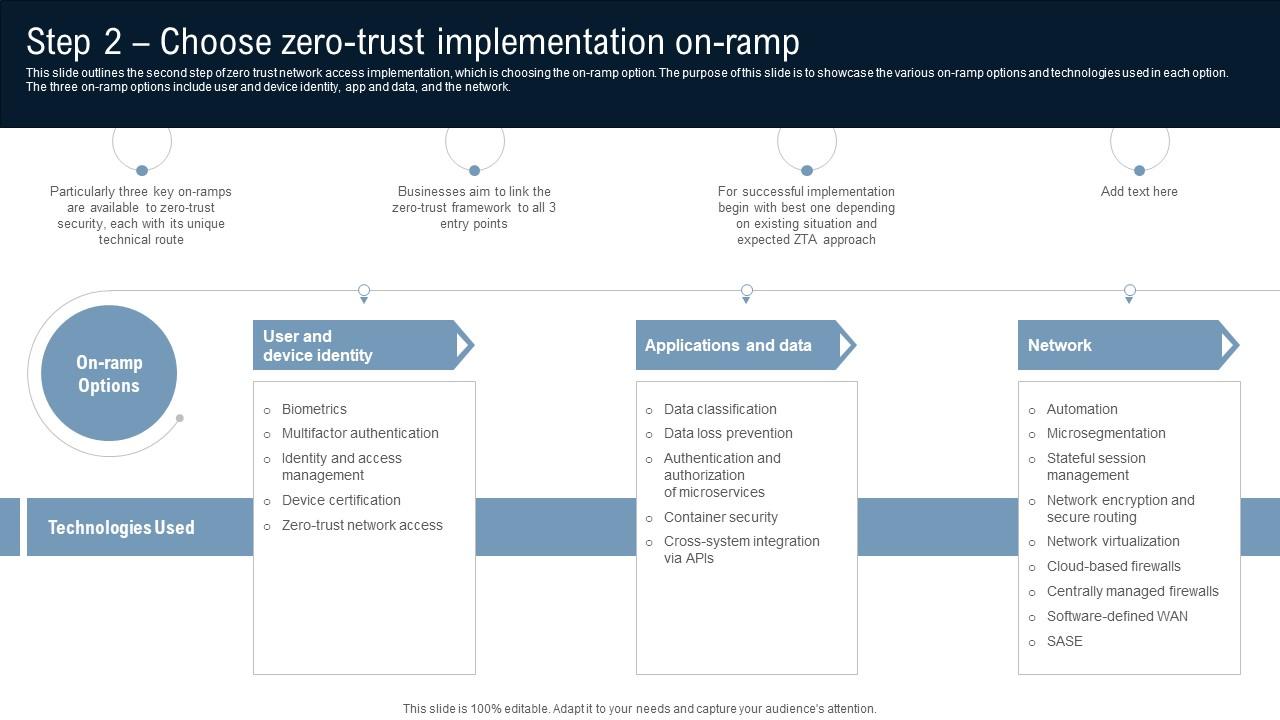
Step 2 Choose Zero Trust Implementation On Ramp Identity Defined Use the steps in this guidance to deploy explicit validation for all access requests that adheres to zero trust principles. This slide outlines the second step of zero trust network access implementation, which is choosing the on ramp option. the purpose of this slide is to showcase the various on ramp options and technologies used in each option.
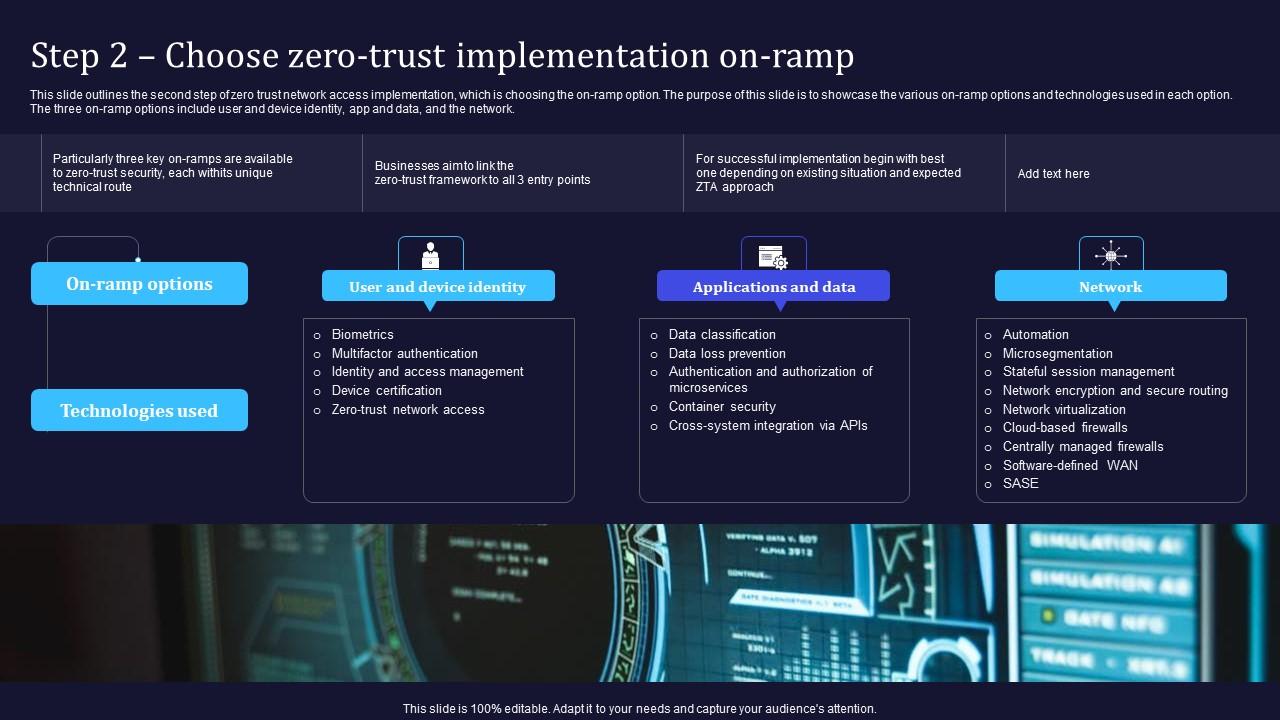
Zero Trust Model Step 2 Choose Zero Trust Implementation On Ramp In our zero trust guides, we define the approach to implement an end to end zero trust methodology across identities, endpoints (devices), data, apps, infrastructure, and network. these activities increase your visibility, which gives you better data for making trust decisions. Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. This slide outlines the second step of zero trust network access implementation, which is choosing the on ramp option. the purpose of this slide is to showcase the various on ramp options and technologies used in each option. Use the steps in this guidance to deploy explicit validation for all access requests that adheres to zero trust principles.

Step 2 Choose Zero Trust Implementation On Ramp Information Pdf This slide outlines the second step of zero trust network access implementation, which is choosing the on ramp option. the purpose of this slide is to showcase the various on ramp options and technologies used in each option. Use the steps in this guidance to deploy explicit validation for all access requests that adheres to zero trust principles. This could involve integrating with an existing identity and access management (iam) identity, credential, and access management (icam) solution, from activity 1.2.1 (phase two) – implement. Ramp guidance takes a project management and checklist approach: * by providing a suggested mapping of key stakeholders, implementers, and their accountabilities, you can more quickly organize an internal project and define the tasks and owners to drive them to conclusion. Below i will describe one of the strategies of implementing zero trust called rapid modernization plan (ramp) which will give any executive or cybersecurity engineer a starting point. Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments.

Zero Trust Network Access Step 2 Choose Zero Trust Implementation On Ramp This could involve integrating with an existing identity and access management (iam) identity, credential, and access management (icam) solution, from activity 1.2.1 (phase two) – implement. Ramp guidance takes a project management and checklist approach: * by providing a suggested mapping of key stakeholders, implementers, and their accountabilities, you can more quickly organize an internal project and define the tasks and owners to drive them to conclusion. Below i will describe one of the strategies of implementing zero trust called rapid modernization plan (ramp) which will give any executive or cybersecurity engineer a starting point. Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments.
Comments are closed.