Ssl Pinning Bypass Using Frida Android Security Android App Pentesting 2026 Phd Security
Android Certificate Pinning Bypass Bulwarkers Web Application Api This page provides a practical workflow to regain dynamic analysis against android apps that detect root‑block instrumentation or enforce tls pinning. it focuses on fast triage, common detections, and copy‑pasteable hooks tactics to bypass them without repacking when possible. Learn how to intercept and analyze https traffic from android apps using frida, even when they use ssl pinning. as an android security researcher or penetration tester, you’ve.

Android Root Detection Bypass Using Frida Part 2 Pentest Learn how to bypass ssl pinning on android apps using frida with step by step commands, real world techniques, and expert insights for penetration testers and security researchers. By following these steps, you can bypass ssl pinning in a target application, allowing you to inspect and manipulate https traffic during security testing. this method leverages frida’s powerful dynamic instrumentation capabilities and the shared script from frida codeshare to simplify the process. | 🔐 ssl pinning bypass on android using frida | step by step guide 2026 learn to bypass ssl pinning on android apps with frida!. This readme provides a clear, organized guide on using the repository to bypass ssl pinning in android applications, making it accessible to developers and security professionals alike.
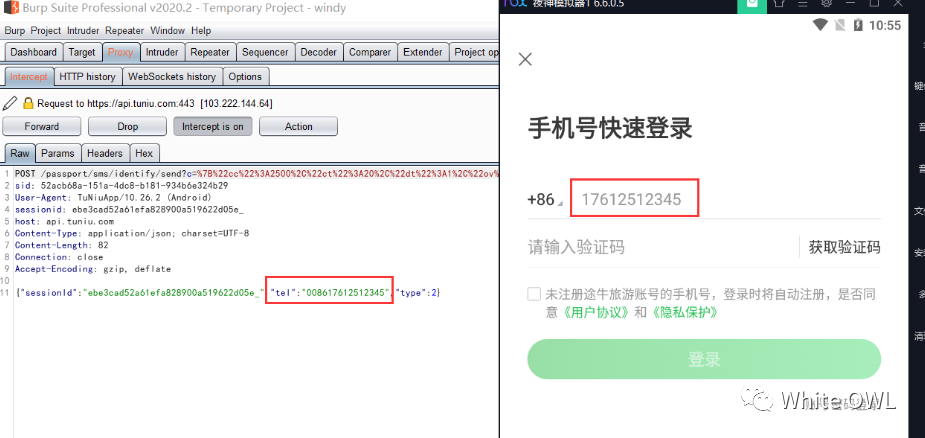
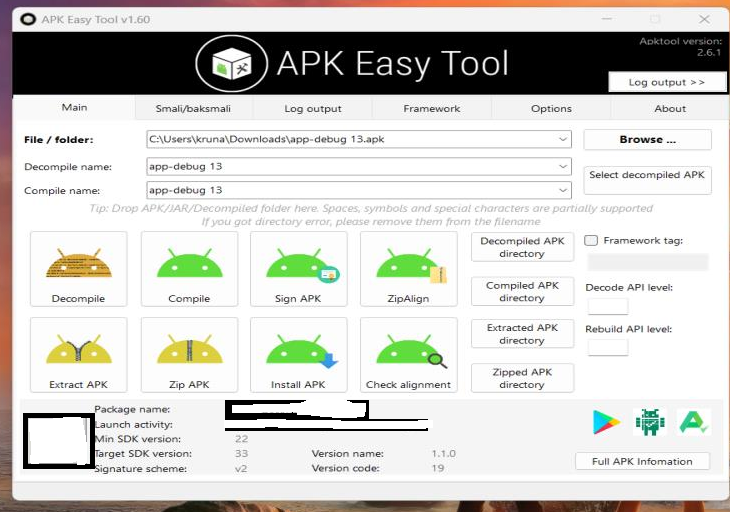
利用frida绕过android App Apk 的ssl Pinning 腾讯云开发者社区 腾讯云 | 🔐 ssl pinning bypass on android using frida | step by step guide 2026 learn to bypass ssl pinning on android apps with frida!. This readme provides a clear, organized guide on using the repository to bypass ssl pinning in android applications, making it accessible to developers and security professionals alike. If the app is implementing ssl pinning with a custom framework or library, the ssl pinning must be manually patched and deactivated, which can be time consuming. this section describes various ways to bypass ssl pinning and gives guidance about what you should do when the existing tools don't help. Add logic to bypass ssl pinning in the form of ‘js’ script. this script will instruct frida to perform manipulations and override the application’s response for ssl pinning. When performing mobile application penetration testing, one of the most common obstacles is ssl pinning. even after installing burp’s certificate, traffic still doesn’t appear – because the application explicitly validates the server certificate. There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post.
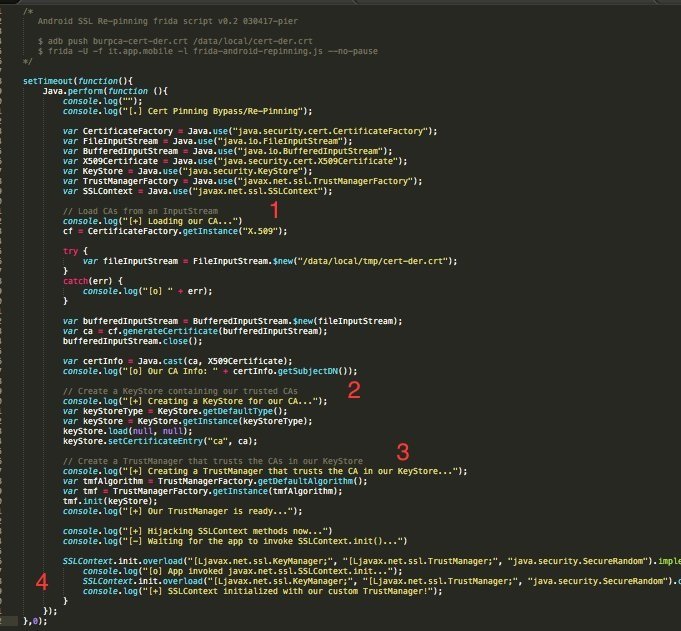
Universal Android Ssl Pinning Bypass With Frida If the app is implementing ssl pinning with a custom framework or library, the ssl pinning must be manually patched and deactivated, which can be time consuming. this section describes various ways to bypass ssl pinning and gives guidance about what you should do when the existing tools don't help. Add logic to bypass ssl pinning in the form of ‘js’ script. this script will instruct frida to perform manipulations and override the application’s response for ssl pinning. When performing mobile application penetration testing, one of the most common obstacles is ssl pinning. even after installing burp’s certificate, traffic still doesn’t appear – because the application explicitly validates the server certificate. There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post.

Ssl Pinning Bypass For Android Emulators Using Frida By Gokce Medium When performing mobile application penetration testing, one of the most common obstacles is ssl pinning. even after installing burp’s certificate, traffic still doesn’t appear – because the application explicitly validates the server certificate. There are a lot of different things that you can do with frida, but one of the most common uses for frida is to bypass ssl pinning. this can be done for both android and ios applications, but i’m just going to go over how to do it with an android device in this blog post.
Ssl Pinning Bypass For Android Emulators Using Frida By Gokce Medium
Comments are closed.