Ssh Keys Management E2e Cloud

Ssh Key Management For Aws Jumpcloud After you log in to the e2e networks ‘my account’, you can click on the left side of the myaccount dashboard, click on the “ssh keys” sub menu available under the services menu. Your ultimate guide to multi cloud ssh key management. covers key sprawl risks, nist recommendations, hardening tips, and a step by step management strategy.
Ssh Key Pair Ssh keys are cryptographic key pairs used in secure shell (ssh) protocol for secure user authentication and communication with servers. they consist of a public key, shared with servers, and a private key, kept securely on the client machine. Choosing an ssh key management is not an easy task because storing and retrieving the private ssh key data is critical. here we list some important key factors to be consider before choosing an ssh key management system to manage your public and private ssh keys. This article examines securing ssh keys through a practical lens grounded in real world cloud security incidents, digital forensics, ediscovery, and criminal defense investigations. Learn how to set up and use ssh keys for passwordless authentication. this guide covers key generation, server setup, and best practices for secure remote access.
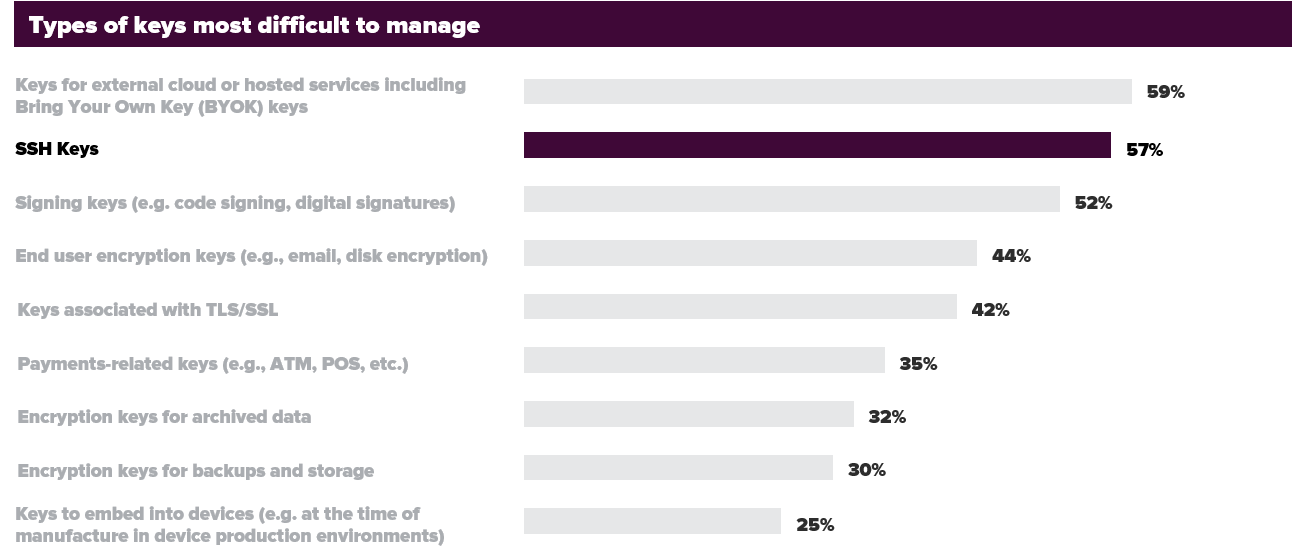
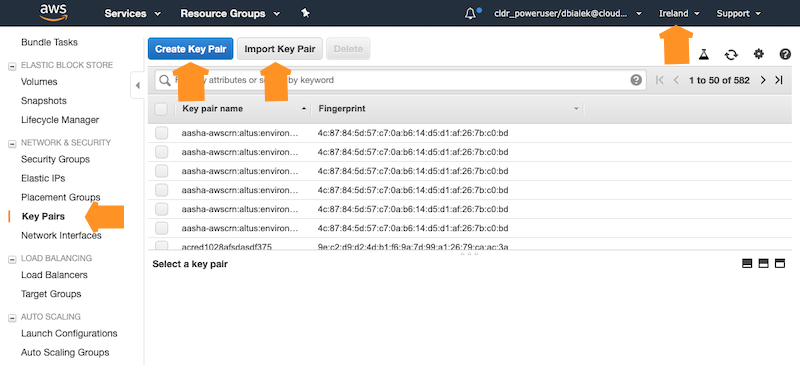
A Guide For Multi Cloud Ssh Key Management Keyfactor This article examines securing ssh keys through a practical lens grounded in real world cloud security incidents, digital forensics, ediscovery, and criminal defense investigations. Learn how to set up and use ssh keys for passwordless authentication. this guide covers key generation, server setup, and best practices for secure remote access. How do you manage and protect ssh keys in multi cloud operations? find out in this overview of ssh in the cloud and cloud ssh key management. Scan and discover all ssh keys spread across hybrid and multi cloud infrastructures – like servers, client devices, cloud instances, and vms – on an on demand basis. Ssh key management platforms offer a centralized, automated, and secure way to tame the keys, ensuring secure remote access, improving operational efficiency, and strengthening your overall security posture. Learn about cloud iam for centralized control and simplifying ssh key management in cloud environments. enhance server access security by utilizing ssh key agents for additional protection and convenience.
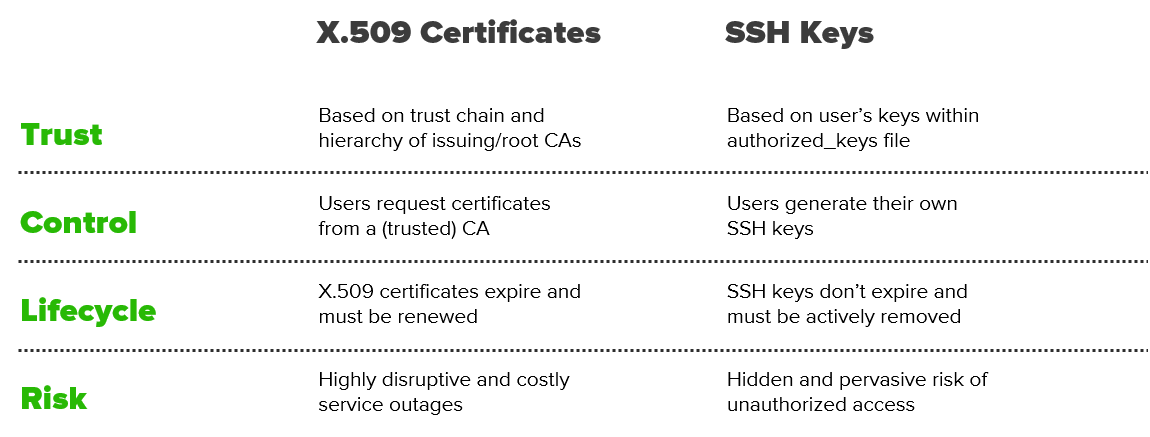
A Guide For Multi Cloud Ssh Key Management Keyfactor How do you manage and protect ssh keys in multi cloud operations? find out in this overview of ssh in the cloud and cloud ssh key management. Scan and discover all ssh keys spread across hybrid and multi cloud infrastructures – like servers, client devices, cloud instances, and vms – on an on demand basis. Ssh key management platforms offer a centralized, automated, and secure way to tame the keys, ensuring secure remote access, improving operational efficiency, and strengthening your overall security posture. Learn about cloud iam for centralized control and simplifying ssh key management in cloud environments. enhance server access security by utilizing ssh key agents for additional protection and convenience.
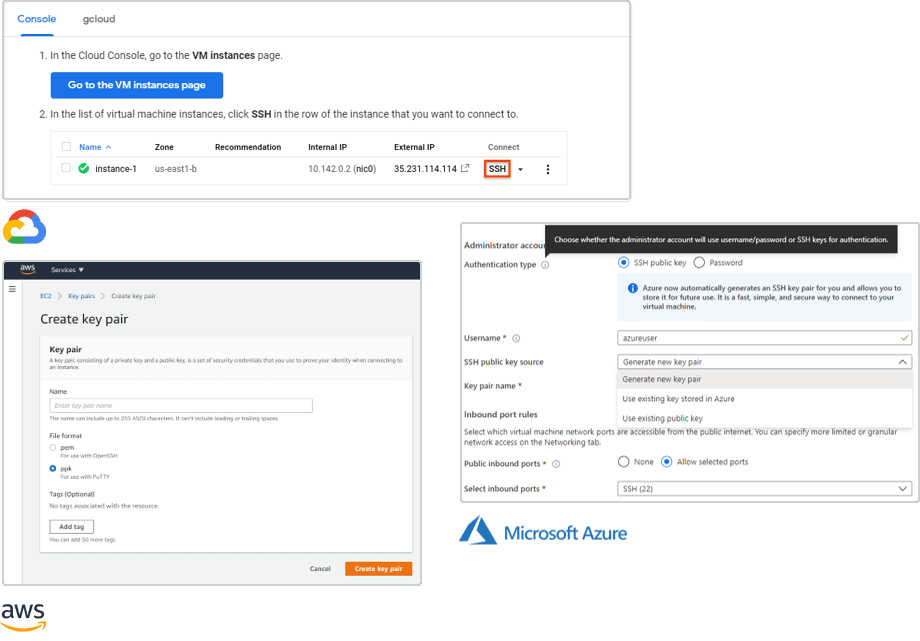
A Guide For Multi Cloud Ssh Key Management Keyfactor Ssh key management platforms offer a centralized, automated, and secure way to tame the keys, ensuring secure remote access, improving operational efficiency, and strengthening your overall security posture. Learn about cloud iam for centralized control and simplifying ssh key management in cloud environments. enhance server access security by utilizing ssh key agents for additional protection and convenience.
Comments are closed.