Ssh Key Based Authentication Ssh Passwordless Authentication Part 4
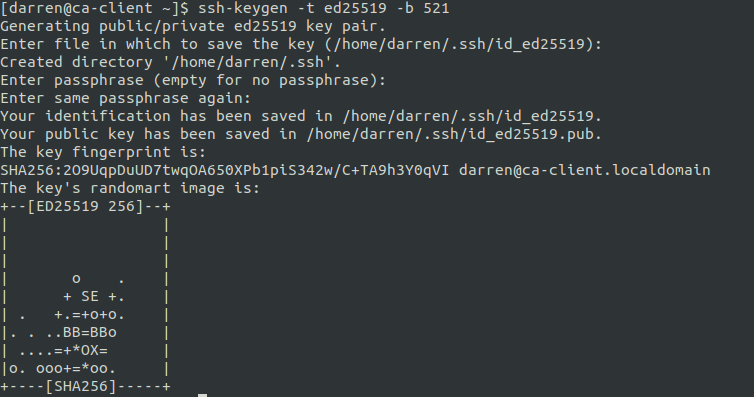
Ssh Key Based Authentication In this video we will learn that how to authenticate user using key based authentication in linux. more. Follow this guide to set up passwordless ssh, enforce best practices like passphrase protected keys and ed25519 algorithms, and rest easy knowing your servers are protected by one of the most secure authentication methods available.
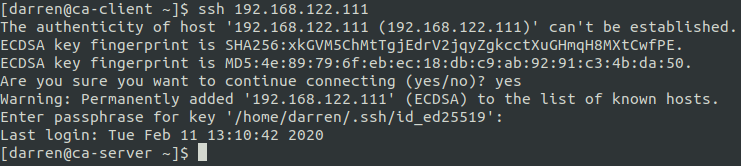
Ssh Key Based Authentication Learn how to set up passwordless ssh login using ssh keys. this guide covers generating key pairs, copying public keys, and disabling password authentication. In this tutorial, we'll compare ssh key based authentication and password authentication. by understanding their processes, pros, cons, and best practices, you'll be equipped to make an informed decision for your server environment. We introduce ssh passkeys, a method for leveraging the web authentication protocol for ssh authentication, replacing passwords with passkeys. we design a framework to integrate passkeys with ssh servers while maintaining backwards compatibility with current clients. Passwordless ssh, also known as key based authentication, provides a more secure and convenient way to log in to remote servers without having to enter a password every time.

Configure Ssh Key Based Authentication Tec Bartec Bar We introduce ssh passkeys, a method for leveraging the web authentication protocol for ssh authentication, replacing passwords with passkeys. we design a framework to integrate passkeys with ssh servers while maintaining backwards compatibility with current clients. Passwordless ssh, also known as key based authentication, provides a more secure and convenient way to log in to remote servers without having to enter a password every time. It's a fairly standard configuration on many linux systems because it reduces the burden on manual ssh authentication and allows for more simplified automation solutions. Implementing ssh key based authentication is a critical step in securing your linux and unix systems. by following this comprehensive guide, you’ve taken a significant step toward protecting your servers from unauthorized access and potential breaches. Ssh authentication with passwords or with passwordless ssh key pairs is common. now learn about zero trust ssh access without passwords and keys. In this quick guide, we’re going to set up passwordless ssh the right way using modern cryptography, secure defaults, and a workflow that’s actually worth your muscle memory.
Comments are closed.