Ssh Key Based Authentication Passwordless Login

How To Setup Passwordless Ssh Login In Linux Learn how to set up passwordless ssh login using ssh keys. this guide covers generating key pairs, copying public keys, and disabling password authentication. This tutorial will walk you step by step through how to manually set up ssh passwordless login to a linux server. these commands should work on the majority of linux distributions, and instructions are included for modern client machines of the macos, windows, and linux varieties.

Ssh Passwordless Login Certificate Problems Portnox In this article, we will show you how to set up an ssh passwordless login using ssh keys to connect remote linux servers without entering passwords. How to setup an ssh key based authentication as well how to connect to your server or workstation without entering a password. Passwordless ssh login streamlines remote server management while boosting security. by following this guide, you’ve generated an ssh key pair, copied the public key to your server, and tested the setup. By using public key authentication, you can eliminate the need to type in your password every time you log in to a remote server. follow the steps outlined in this article to set up passwordless ssh login and enjoy the convenience and security it provides.
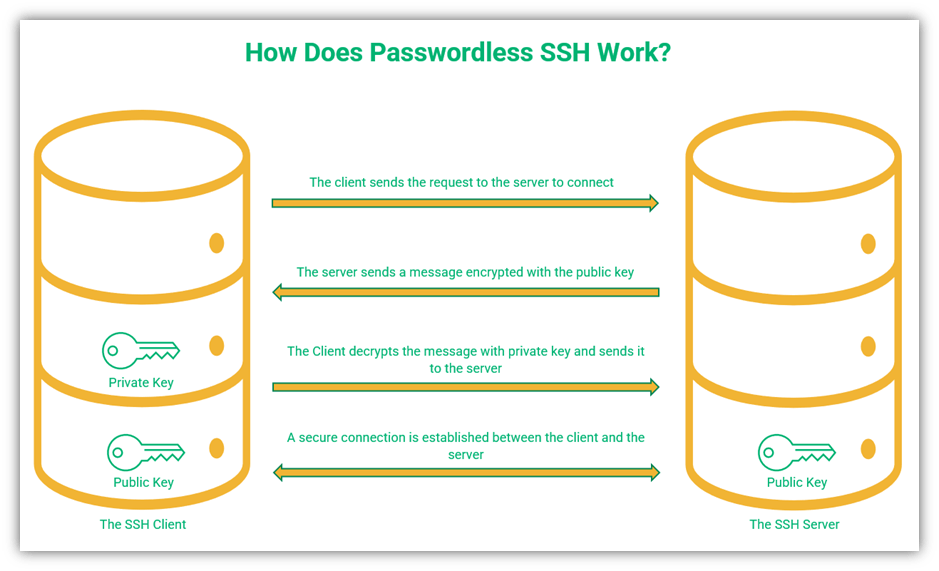
What Is Passwordless Ssh A Look At Ssh Passwordless Authentication Passwordless ssh login streamlines remote server management while boosting security. by following this guide, you’ve generated an ssh key pair, copied the public key to your server, and tested the setup. By using public key authentication, you can eliminate the need to type in your password every time you log in to a remote server. follow the steps outlined in this article to set up passwordless ssh login and enjoy the convenience and security it provides. If you're looking for a safer, faster, and more reliable way to access your servers, ssh key based authentication is the solution. in this guide, we’ll show you how to set up passwordless ssh login for linux and windows (via putty) and share tips to boost your ssh security posture. There are two ways to authenticate an ssh connection password authentication and public key authentication. this tutorial will teach you how to set up and enable passwordless ssh login. By implementing automated ssh login without passwords, you can free up a tremendous amount of time and supercharge remote management. in this detailed tutorial, you will gain hands on experience configuring key based authentication for passwordless ssh access. Automatic scripted automation for accessing remote servers could be potentially necessary, such as when you have kubernetes on the remote server that needs deployment and management. passwordless.
How To Set Up Passwordless Ssh Login Instructional Guide If you're looking for a safer, faster, and more reliable way to access your servers, ssh key based authentication is the solution. in this guide, we’ll show you how to set up passwordless ssh login for linux and windows (via putty) and share tips to boost your ssh security posture. There are two ways to authenticate an ssh connection password authentication and public key authentication. this tutorial will teach you how to set up and enable passwordless ssh login. By implementing automated ssh login without passwords, you can free up a tremendous amount of time and supercharge remote management. in this detailed tutorial, you will gain hands on experience configuring key based authentication for passwordless ssh access. Automatic scripted automation for accessing remote servers could be potentially necessary, such as when you have kubernetes on the remote server that needs deployment and management. passwordless.
Comments are closed.