Ssh Guide For It Professionals Pdf

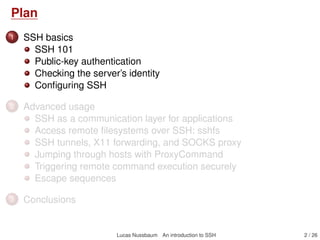
Ssh Pdf Pdf Secure Shell Shell Computing The document is a comprehensive guide to secure shell (ssh), detailing its use for secure system management, file transfer, and connection tunneling. it covers configuration, public private key authentication, advanced features, x11 forwarding, and best practices for secure usage. This downloadable ebook, shrouded in suspense, is available in a pdf format ( *). dive into a world of uncertainty and anticipation. download now to unravel the secrets hidden within the pages.
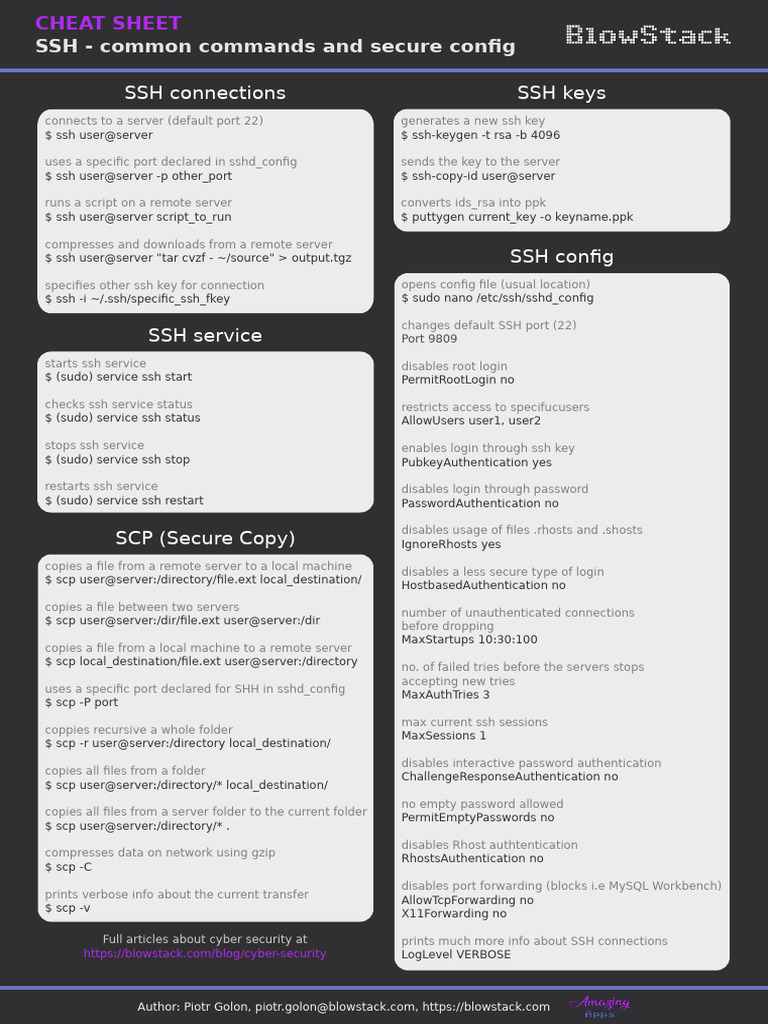
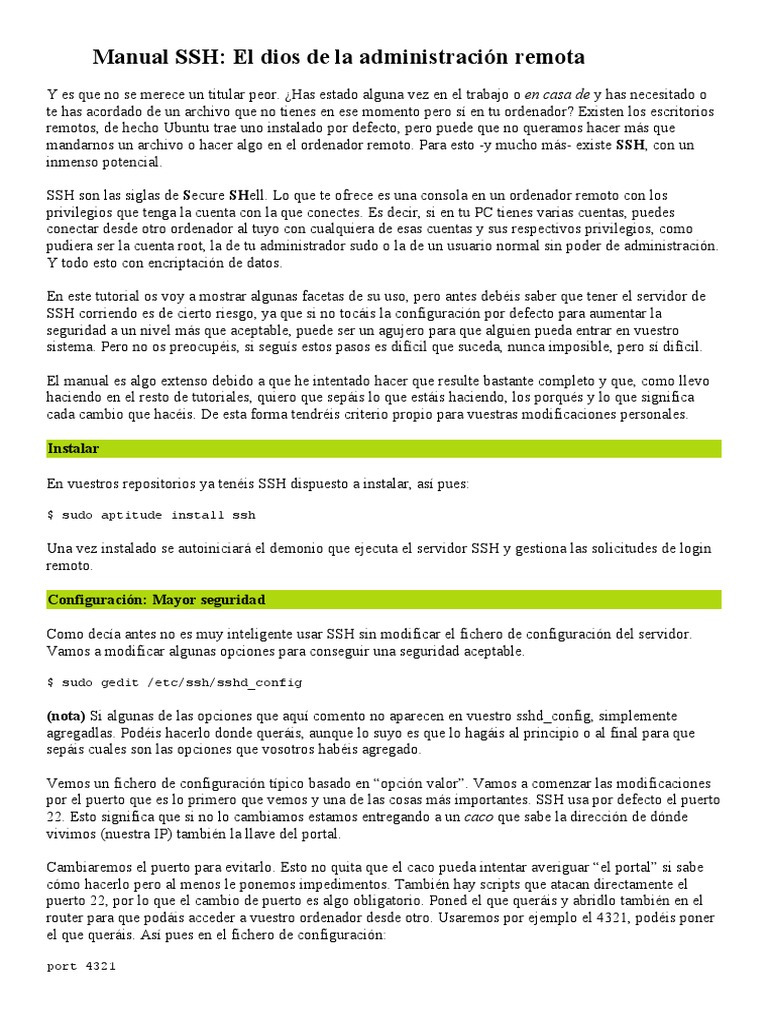
Ssh Cheat Sheet Pdf Secure Shell Information Technology Management This chapter provides guidelines for configuring ssh (secure shell) securely for system administrators running ssh on unix systems. the focus is on establishing a secure system, even at the expense of flexibility. The ssh protocol, version 1. this protocol went through several revisions, of which 1.3 and 1.5 are the best known, and we will write ssh 1.3 and ssh 1.5 should the distinction be necessary. Red hat a trusted adviser to the fortune 500. 1 ssh user's guide the erlang secure shell (ssh) application, ssh, implements the ssh transport layer protocol and provides ssh file transfer protocol (sftp) clients and servers.

Ssh Command Cheat Sheet Quick Reference Pdf Secure Shell Red hat a trusted adviser to the fortune 500. 1 ssh user's guide the erlang secure shell (ssh) application, ssh, implements the ssh transport layer protocol and provides ssh file transfer protocol (sftp) clients and servers. 01. advanced penetration testing.pdf 02. the basics of web hacking.pdf 03. the basics of hacking and penetration testing.pdf 04. the art of deception by kevin mitnick.pdf 05. sql injection attacks and defense.pdf 06. metasploit the penetration tester's guide.pdf. Ssh is a program that allows you to remotely access other systems. it has two parts: the server, which must be active on the system you wish to connect to, and the client, which you run on your system to connect. Ssh, the secure shell : the definitive guide by barrett, daniel j publication date 2005 topics unix shells, data encryption (computer science), computer networks security measures publisher sebastopol, ca : o'reilly collection internetarchivebooks; printdisabled contributor internet archive language english item size 1.2g xviii, 645 p. : 24. Secure shell (ssh) provides an open protocol for securing network communications that is less complex and expensive than hardware based vpn solutions. secure shell client server solutions provide command shell, file transfer, and data tunneling services for tcp ip applications.
Ssh Quick Reference Cheat Sheet 01. advanced penetration testing.pdf 02. the basics of web hacking.pdf 03. the basics of hacking and penetration testing.pdf 04. the art of deception by kevin mitnick.pdf 05. sql injection attacks and defense.pdf 06. metasploit the penetration tester's guide.pdf. Ssh is a program that allows you to remotely access other systems. it has two parts: the server, which must be active on the system you wish to connect to, and the client, which you run on your system to connect. Ssh, the secure shell : the definitive guide by barrett, daniel j publication date 2005 topics unix shells, data encryption (computer science), computer networks security measures publisher sebastopol, ca : o'reilly collection internetarchivebooks; printdisabled contributor internet archive language english item size 1.2g xviii, 645 p. : 24. Secure shell (ssh) provides an open protocol for securing network communications that is less complex and expensive than hardware based vpn solutions. secure shell client server solutions provide command shell, file transfer, and data tunneling services for tcp ip applications.
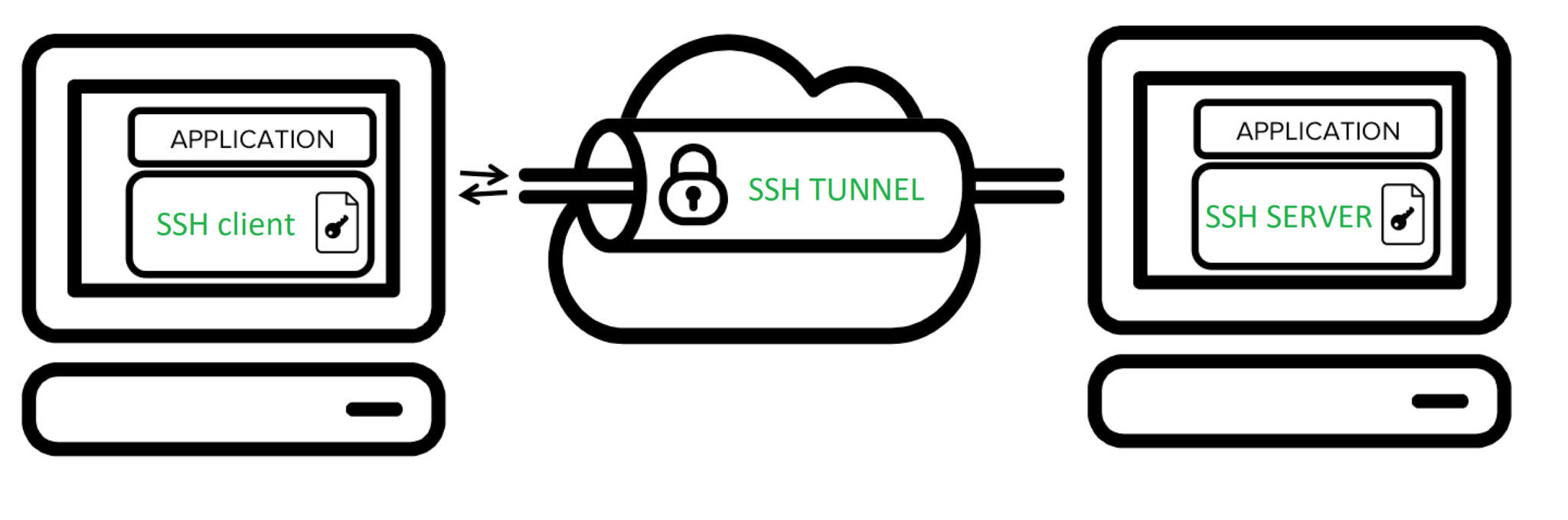
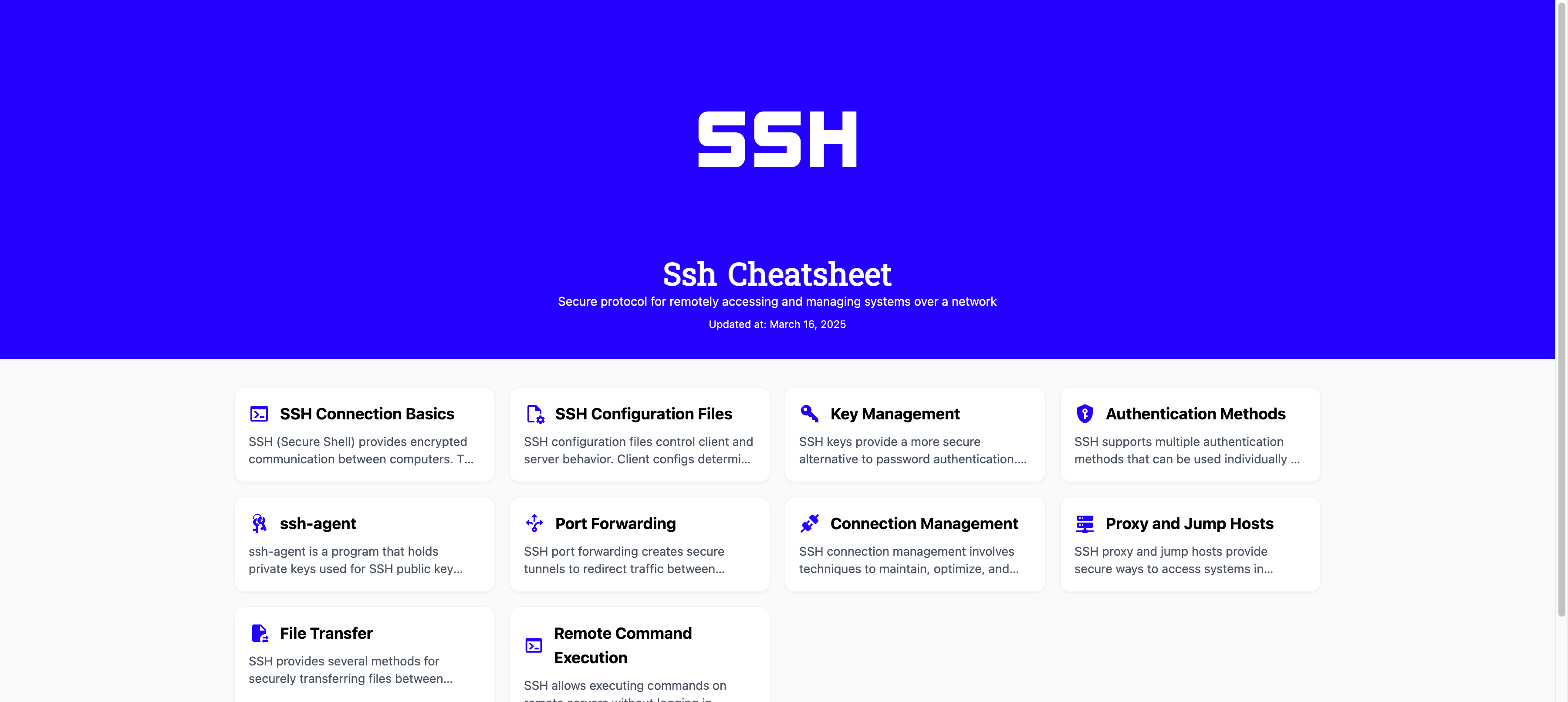
A Comprehensive Guide To Ssh For Beginners Toàn Thiện Blog Ssh, the secure shell : the definitive guide by barrett, daniel j publication date 2005 topics unix shells, data encryption (computer science), computer networks security measures publisher sebastopol, ca : o'reilly collection internetarchivebooks; printdisabled contributor internet archive language english item size 1.2g xviii, 645 p. : 24. Secure shell (ssh) provides an open protocol for securing network communications that is less complex and expensive than hardware based vpn solutions. secure shell client server solutions provide command shell, file transfer, and data tunneling services for tcp ip applications.

Ssh2 Usersguide Pdf Secure Shell Public Key Certificate

Ssh Cheat Sheet En Pdf Computer File File Transfer Protocol
Ssh Protocol Explained The Ultimate Guide In Pdf
Guides Cheat Sheet Cheat Sheet Ssh V4 Pdf At Main Jonhespeto Guides

An Illustrated Guide To Ssh Tunnels Pdf Secure Shell Networking

Ssh And Ftp Installation Guide Pdf Technology Engineering

Ssh Pdf

Tunneling With Ssh Pdf Secure Shell Computer Network

Ssh Cheat Sheet Stordis Gmbh

Ssh The Ultimate Strategy Guide For Cybersecurity

How To Provide Ssh A Step By Step Guide
An Introduction To Ssh Pdf

Ssh Configuration Download Free Pdf Ip Address Network Architecture

Configure Network Devices With Ssh Pdf Computer Network Secure Shell

Ssh Protocol Explained The Ultimate Guide In Pdf

A Beginner S Guide To Ssh Pdf

The Ultimate Guide To Manage Your Files Via Ssh

An Introduction To Ssh Pdf

Ccna Ssh Configuration Pdf Ip Address Router Computing

Configuration Details For Multiple Ssh Hosts Including Server Names
Xk0 005 Lesson 002 Ssh Users Groups 002 Advanced Ssh Pdf At Main
The Beginner S Guide To Ssh

Ssh A Complete Guide 2021 Edition Ebook By Gerardus Blokdyk Epub

Ssh For Beginners The Ultimate Getting Started Guide Timothy Dilbert

Guiding Ssh Pdf

Cheatsheet Ssh A4 Pdf
Guía Completa Para Dominar Ssh La Herramienta Esencial Para La
The Beginner S Guide To Ssh Connections Web Security Lab

Ssh Guide For It Professionals Pdf

Ssh Protocol Guide For Secure Remote Access Moldstud
Comments are closed.