Ssh Authentication Methods Password Key Based Or Certificate Based
Ssh Key Based Authentication Two of the most common authentication methods are password based and key based authentication. understanding the differences between these methods is key to implementing effective security practices. In this tutorial, we'll compare ssh key based authentication and password authentication. by understanding their processes, pros, cons, and best practices, you'll be equipped to make an informed decision for your server environment.

Configure Ssh Key Based Authentication Tec Bartec Bar The ssh protocol (aka secure shell) is used to establish secure and reliable communications between two hosts. it supports different ssh authentication methods and uses strong encryption to protect exchanged data. When it comes to securing access to your linux servers, the choice of ssh authentication method can make a world of difference. with options ranging from simple passwords to complex certificate based systems, it's essential to understand the tradeoffs between convenience and security. In this article, we looked at ssh authentication methods, ways for servers to require them in order, and for clients to prefer some to others. in conclusion, knowing how to order authentication methods introduces another layer of security to the golden standard, which is ssh. These authentication methods can be combined or used separately, depending on the level of functionality and security you want. user authentication methods used by the client by default are, in the following order: gssapi, public key, keyboard interactive, and password authentication (if available).
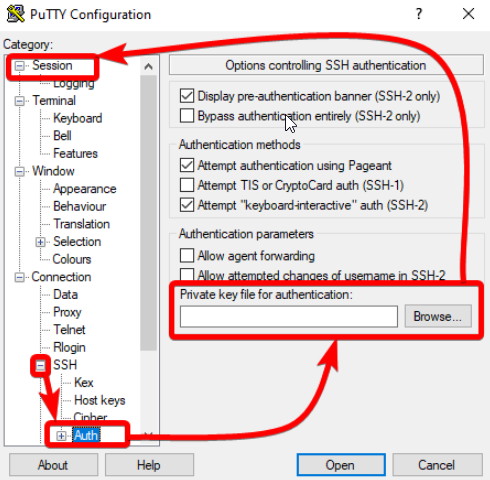
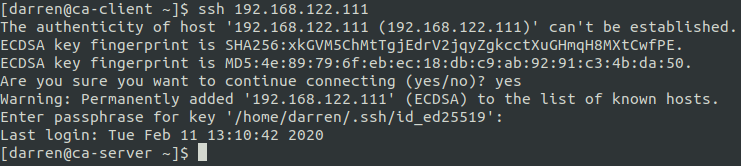
Ssh Key Vs Password Based Authentication Hostwinds In this article, we looked at ssh authentication methods, ways for servers to require them in order, and for clients to prefer some to others. in conclusion, knowing how to order authentication methods introduces another layer of security to the golden standard, which is ssh. These authentication methods can be combined or used separately, depending on the level of functionality and security you want. user authentication methods used by the client by default are, in the following order: gssapi, public key, keyboard interactive, and password authentication (if available). There are two main authentication methods used in ssh: password based and key based authentication. passwords require manual entry and depend on user created credentials, while ssh keys rely on cryptographic algorithms that generate unique key pairs. In password based authentication, after establishing secure connection with remote servers, ssh users usually pass on their usernames and passwords to remote servers for client authentication. these credentials are shared through the secure tunnel established by symmetric encryption. This blog post compares four different passwordless authentication methods for ssh: ssh keys, certificates, host based, and pam modules. Password authentication is simple and straightforward. the user provides a username and password to the ssh server and the server verifies these credentials against its local user database or an external authentication system (like ldap).

Ssh Key Based Authentication Linux Administrator System There are two main authentication methods used in ssh: password based and key based authentication. passwords require manual entry and depend on user created credentials, while ssh keys rely on cryptographic algorithms that generate unique key pairs. In password based authentication, after establishing secure connection with remote servers, ssh users usually pass on their usernames and passwords to remote servers for client authentication. these credentials are shared through the secure tunnel established by symmetric encryption. This blog post compares four different passwordless authentication methods for ssh: ssh keys, certificates, host based, and pam modules. Password authentication is simple and straightforward. the user provides a username and password to the ssh server and the server verifies these credentials against its local user database or an external authentication system (like ldap).

Ssh Key Based Authentication Linux Administrator System This blog post compares four different passwordless authentication methods for ssh: ssh keys, certificates, host based, and pam modules. Password authentication is simple and straightforward. the user provides a username and password to the ssh server and the server verifies these credentials against its local user database or an external authentication system (like ldap).
Comments are closed.