Ssh A Guide To Secure Shell

Ssh Secure Shell Pdf This guide provides an in depth overview of ssh, including its configuration, public private key based authentication, advanced features, x11 forwarding, and best practices for secure usage. A beginner friendly guide to ssh: what it is, how it works, and how to set up key based authentication securely.

1 Ssh Pdf Secure Shell Port Computer Networking What is the secure shell (ssh) protocol? the secure shell (ssh) protocol is a method for securely sending commands to a computer over an unsecured network. ssh uses cryptography to authenticate and encrypt connections between devices. Learn how to use ssh to securely connect to a remote server. this step by step guide covers setup, syntax, key auth, troubleshooting, and best practices. Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers. In this article, we will cover the essentials of ssh, helping us become confident in connecting remotely, pushing code, and managing our development workflow like a pro. ssh is a cryptographic.
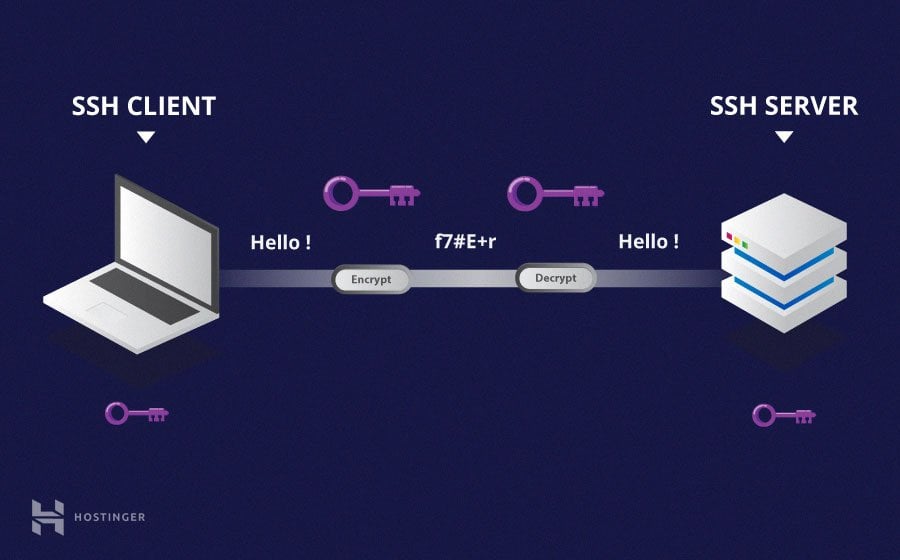
Secure Shell Protocol Ssh Msblab Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers. In this article, we will cover the essentials of ssh, helping us become confident in connecting remotely, pushing code, and managing our development workflow like a pro. ssh is a cryptographic. Ssh (ssh client) is a program for logging into a remote machine and for executing commands on a remote machine. it is intended to provide secure encrypted communications between two untrusted hosts over an insecure network. Learn how to use ssh commands, what are some of the options, and how to configure them in linux unix. Start with this beginner friendly ssh tutorial to manage servers securely and confidently. you’ll learn what ssh is, how it works, and how to log in on macos, linux, or windows. the guide covers generating and protecting ssh keys, creating strong passphrases, and using shell commands for real tasks. Ssh (secure shell) is a secure communication protocol that allows a user to access and control a remote computer over a network. unlike older protocols like telnet or rlogin, ssh encrypts every piece of data, preventing attackers from spying on login credentials and commands.

Ssh Shell Secure Milolab Ssh (ssh client) is a program for logging into a remote machine and for executing commands on a remote machine. it is intended to provide secure encrypted communications between two untrusted hosts over an insecure network. Learn how to use ssh commands, what are some of the options, and how to configure them in linux unix. Start with this beginner friendly ssh tutorial to manage servers securely and confidently. you’ll learn what ssh is, how it works, and how to log in on macos, linux, or windows. the guide covers generating and protecting ssh keys, creating strong passphrases, and using shell commands for real tasks. Ssh (secure shell) is a secure communication protocol that allows a user to access and control a remote computer over a network. unlike older protocols like telnet or rlogin, ssh encrypts every piece of data, preventing attackers from spying on login credentials and commands.
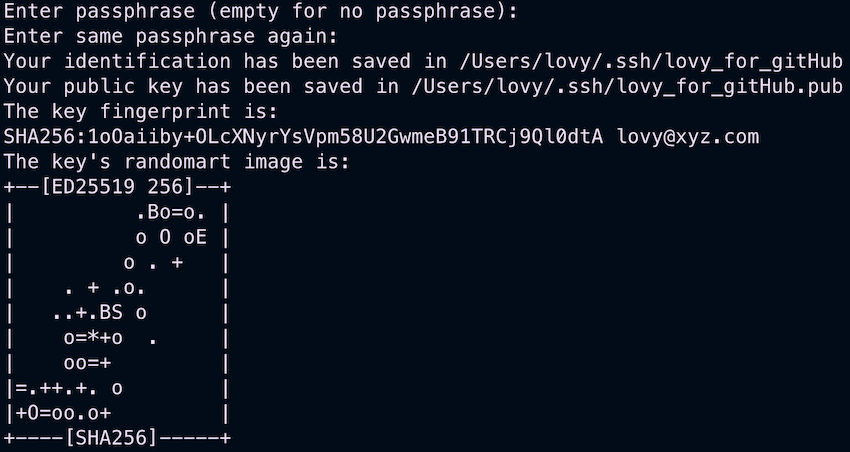
Secure Shell Ssh A Comprehensive Guide To Secure Login Start with this beginner friendly ssh tutorial to manage servers securely and confidently. you’ll learn what ssh is, how it works, and how to log in on macos, linux, or windows. the guide covers generating and protecting ssh keys, creating strong passphrases, and using shell commands for real tasks. Ssh (secure shell) is a secure communication protocol that allows a user to access and control a remote computer over a network. unlike older protocols like telnet or rlogin, ssh encrypts every piece of data, preventing attackers from spying on login credentials and commands.
Comments are closed.