Sql Server Net And C Video Tutorial Open Redirect Vulnerability
Guest Diary Open Redirect A Small But Very Common Vulnerability In this video, we explain how open redirect vulnerabilities work and how to create a proof of concept (poc) for bug bounty or ethical hacking purposes. Learn about the risks of exposing open redirects, how to exploit them and how to mitigate them.
What Is An Open Redirect Vulnerability Why Is It Dangerous And How Can What is an open redirection attack? by jon galloway. this tutorial explains how you can prevent open redirection attacks in your asp mvc applications. Open redirection vulnerabilities arise when an application incorporates user controllable data into the target of a redirection in an unsafe way. an attacker can construct a url within the application that causes a redirection to an arbitrary external domain. The above code is vulnerable to an attack if no validation or extra method controls are applied to verify the certainty of the url. this vulnerability could be used as part of a phishing scam by redirecting users to a malicious site. After completing this lab, the learner will understand how to defend c# applications against open redirect vulnerabilities by receiving hands on experience testing for these vulnerabilities and implementing a suitable mitigation.
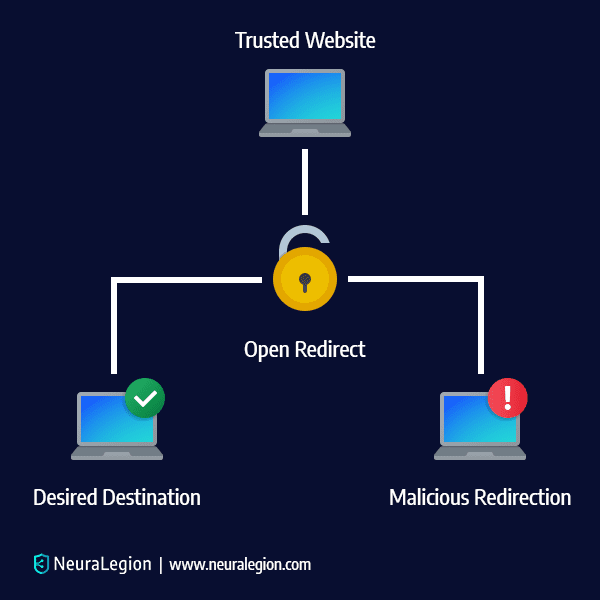
Open Redirect Vulnerability Impact Prevention The above code is vulnerable to an attack if no validation or extra method controls are applied to verify the certainty of the url. this vulnerability could be used as part of a phishing scam by redirecting users to a malicious site. After completing this lab, the learner will understand how to defend c# applications against open redirect vulnerabilities by receiving hands on experience testing for these vulnerabilities and implementing a suitable mitigation. Here's guidance into open redirect vulnerabilities and how to apply mitigation measures against them using open redirect measures. Open redirects, otherwise known as unvalidated redirects and forwards, are a class of vulnerability made possible when a web application, comprised of insufficient input validation controls, is manipulated into redirecting unwitting users of the application to a malicious, attacker controlled url. We are simply redirecting to that url without any validation which is what is making our application vulnerable to open redirect attacks. to prevent open redirect attacks, check if the provided url is a local url or you are only redirecting to known trusted websites. In this article, i’m going to cover what an open redirect vulnerability is, how to discover and exploit it, and some common defense evasion tactics. if you have any corrections or better.
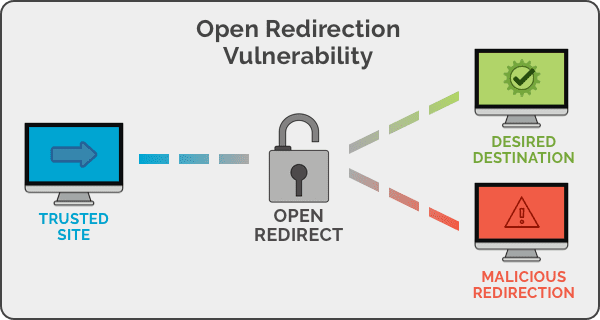
Open Redirection Vulnerability Web Based Application Security Part 1 Here's guidance into open redirect vulnerabilities and how to apply mitigation measures against them using open redirect measures. Open redirects, otherwise known as unvalidated redirects and forwards, are a class of vulnerability made possible when a web application, comprised of insufficient input validation controls, is manipulated into redirecting unwitting users of the application to a malicious, attacker controlled url. We are simply redirecting to that url without any validation which is what is making our application vulnerable to open redirect attacks. to prevent open redirect attacks, check if the provided url is a local url or you are only redirecting to known trusted websites. In this article, i’m going to cover what an open redirect vulnerability is, how to discover and exploit it, and some common defense evasion tactics. if you have any corrections or better.
Comments are closed.