Sql Injection Remote Code Execution Double P1 Bug Bounty Directory
Automating Sql Injection And Cross Site Scripting Vulnerability Contribute to faizee asad bug bounty development by creating an account on github. Browse 5,000 curated bug bounty writeups from the security community. learn from real vulnerability discoveries, techniques, and methodologies.
Automating Sql Injection And Cross Site Scripting Vulnerability A comprehensive sql injection detection and exploitation tool with support for multiple database types and advanced evasion techniques. Bug bounty writeups a list of available bug bounty & disclosure programs and write ups. Here is a technical breakdown of the critical vulnerabilities discovered, the exploitation methodology used, and the necessary remediation strategies. 1. authentication bypass via boolean based. A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters.
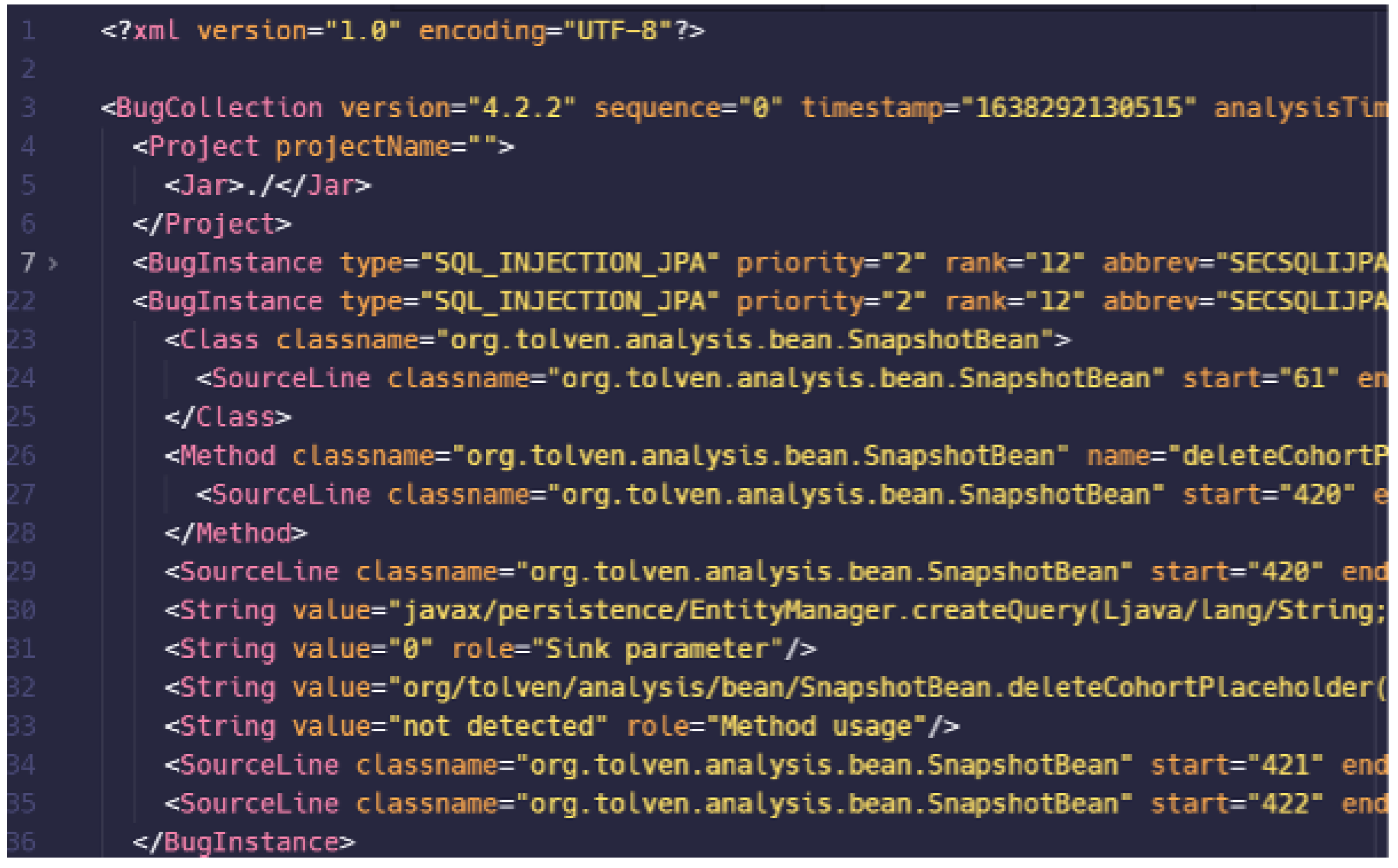
Automating Sql Injection And Cross Site Scripting Vulnerability Here is a technical breakdown of the critical vulnerabilities discovered, the exploitation methodology used, and the necessary remediation strategies. 1. authentication bypass via boolean based. A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters. You'll learn how to tailor payloads to the sql statement in play, incorporate them into your bug bounty workflow, and detect and exploit sqli vulnerabilities – even in hardened systems. This is a directory of ethical hacking writeups including bug bounty, responsible disclosure and pentest writeups. my goal is to help you improve your hacking skills by making it easy to learn about thousands of vulnerabilities that hackers found on different targets. A curated list of available bug bounty & disclosure programs and write ups. kh4sh3i bug bounty writeups. Bug bounty writeups a list of available bug bounty & disclosure programs and write ups.
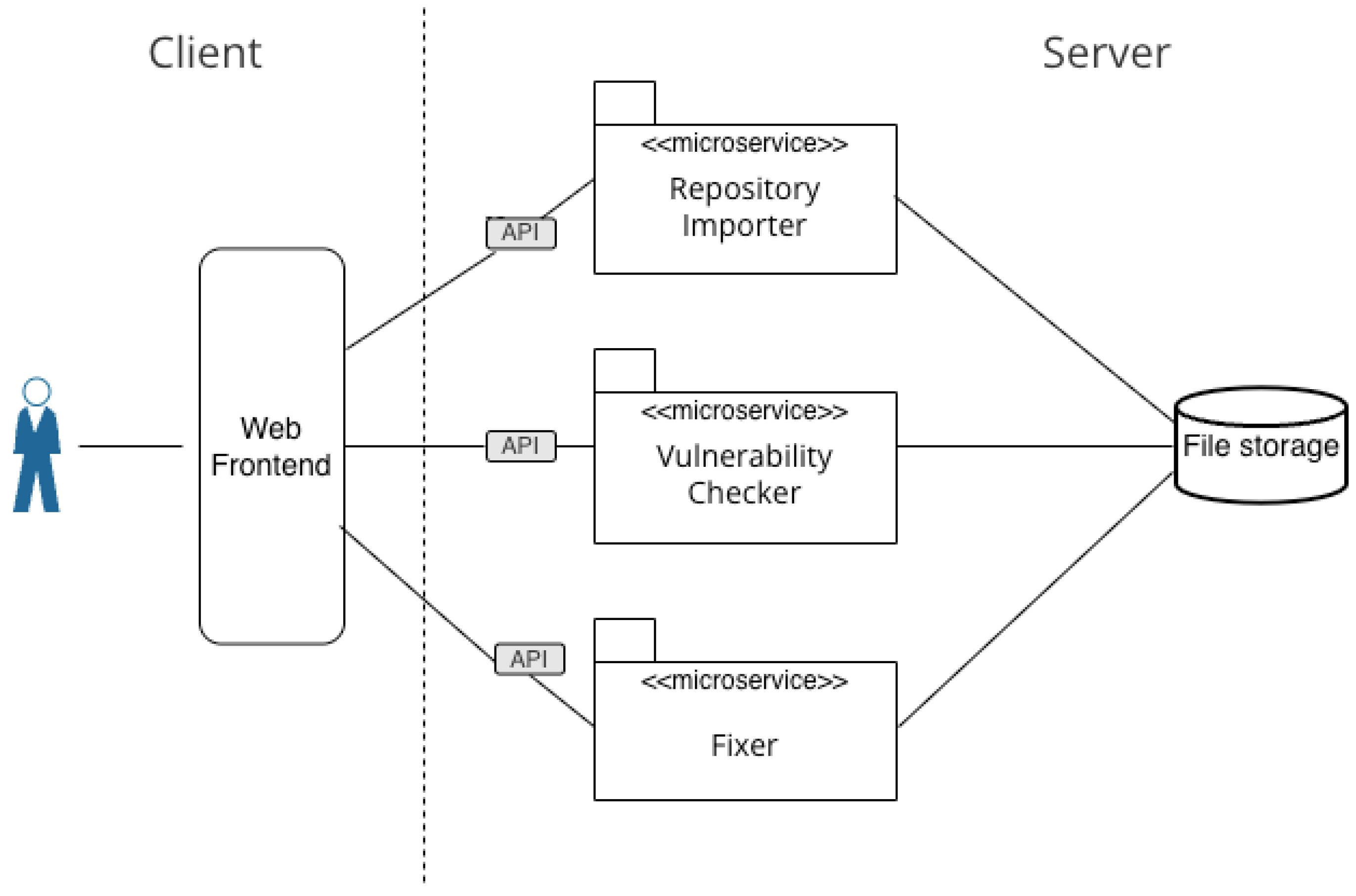
Automating Sql Injection And Cross Site Scripting Vulnerability You'll learn how to tailor payloads to the sql statement in play, incorporate them into your bug bounty workflow, and detect and exploit sqli vulnerabilities – even in hardened systems. This is a directory of ethical hacking writeups including bug bounty, responsible disclosure and pentest writeups. my goal is to help you improve your hacking skills by making it easy to learn about thousands of vulnerabilities that hackers found on different targets. A curated list of available bug bounty & disclosure programs and write ups. kh4sh3i bug bounty writeups. Bug bounty writeups a list of available bug bounty & disclosure programs and write ups.
Comments are closed.