Sql Injection Attack Via Orm Sink Valency Networks
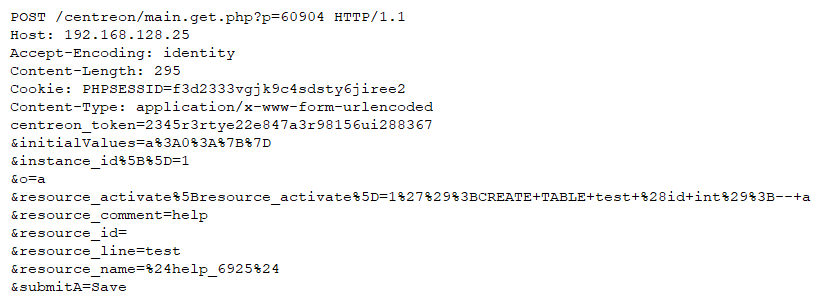
Centreon Sql Injection Vulnerability From the perspective of a tester, this attack is more identical to an sql injection attack. however, the injection vulnerability does exist in code generated by the orm tool. The vulnerability ormar is a popular async mini orm for python, commonly used with fastapi and starlette. versions 0.9.9 through 0.22.0 contain a sql injection vulnerability in the min () and max () aggregate methods.

Sql Injection And Cross Site Scripting The Differences And Attack This vulnerability in ormar presents a risk of data manipulation or exfiltration through sql injection. the practical threat largely depends on whether the application exposes ormar ’s aggregate min() and max() functions to user controlled input without sufficient validation or sanitization. From the point of view of a tester, this attack is virtually identical to a sql injection attack. however, the injection vulnerability exists in code generated by the orm layer. This article shows how sql injection vulnerabilities can still occur in apps using modern orm frameworks. learn how to spot insecure patterns and write safer code. Sql injection attack via orm sink ⭐️ compliance 2 min read 19 10 2025 prashant phatak.
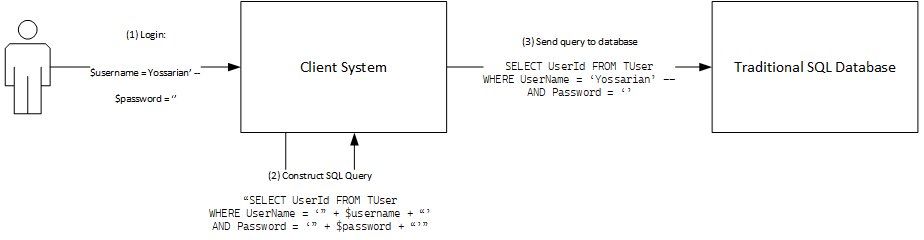
Primer Introduction To Sql Injection Attacks Firesand This article shows how sql injection vulnerabilities can still occur in apps using modern orm frameworks. learn how to spot insecure patterns and write safer code. Sql injection attack via orm sink ⭐️ compliance 2 min read 19 10 2025 prashant phatak. Sql injection is a technique where attackers inject sql code into application inputs to retrieve or manipulate database information. it compromises confidentiality, integrity, and in some cases availability of data. attacks can lead to vertical or horizontal privilege escalation. From the point of view of a tester, this attack is virtually identical to a sql injection attack. however, the injection vulnerability exists in code generated by the orm layer. Versions 0.9.9 through 0.22.0 are affected. the vulnerability stems from the orm's construction of sql expressions in aggregate queries, where user supplied column names are passed directly into `sqlalchemy.text ()` without adequate validation or sanitization. However, a critical vulnerability has been identified in versions 0.9.9 to 0.22.0, which allows for sql injection through the min () and max () aggregate functions, potentially exposing sensitive data. the vulnerability arises from the way ormar handles user supplied input in aggregate queries.
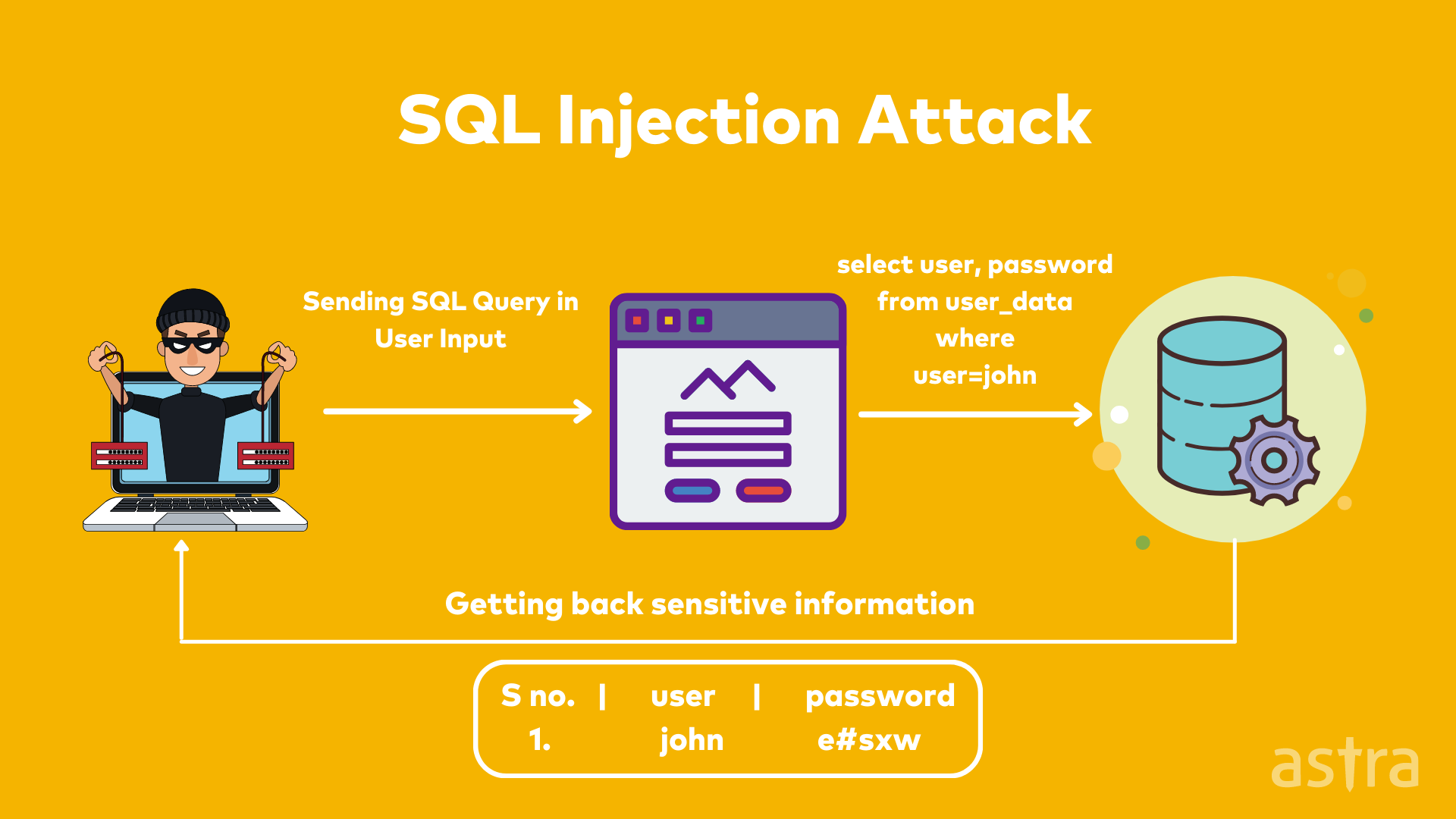
A Comprehensive Guide To Owasp Penetration Testing Sql injection is a technique where attackers inject sql code into application inputs to retrieve or manipulate database information. it compromises confidentiality, integrity, and in some cases availability of data. attacks can lead to vertical or horizontal privilege escalation. From the point of view of a tester, this attack is virtually identical to a sql injection attack. however, the injection vulnerability exists in code generated by the orm layer. Versions 0.9.9 through 0.22.0 are affected. the vulnerability stems from the orm's construction of sql expressions in aggregate queries, where user supplied column names are passed directly into `sqlalchemy.text ()` without adequate validation or sanitization. However, a critical vulnerability has been identified in versions 0.9.9 to 0.22.0, which allows for sql injection through the min () and max () aggregate functions, potentially exposing sensitive data. the vulnerability arises from the way ormar handles user supplied input in aggregate queries.

Enhancing The Performance Of Sql Injection Attack Detection Through Versions 0.9.9 through 0.22.0 are affected. the vulnerability stems from the orm's construction of sql expressions in aggregate queries, where user supplied column names are passed directly into `sqlalchemy.text ()` without adequate validation or sanitization. However, a critical vulnerability has been identified in versions 0.9.9 to 0.22.0, which allows for sql injection through the min () and max () aggregate functions, potentially exposing sensitive data. the vulnerability arises from the way ormar handles user supplied input in aggregate queries.
Comments are closed.