Sql First Code In Android Mobile Sql Phone App Sql Viral Shorts Phone App
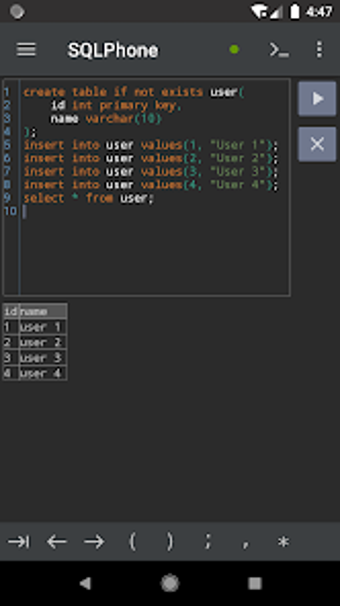
Sqlphone Sql Interpreter For Android Download Contribute to annontopicmodel unsupervised topic modeling development by creating an account on github. Find tickets to your next unforgettable experience. browse concerts, workshops, yoga classes, charity events, food and music festivals, and more things to do.

This App Lets You Practice Sql On Your Android Phone Techwiser Providing it professionals with a unique blend of original content, peer to peer advice from the largest community of it leaders on the web. Symantec security research centers around the world provide unparalleled analysis of and protection from it security threats that include malware, security risks, vulnerabilities, and spam. Create custom, responsive websites with the power of code — visually. design and build your site with a flexible cms and top tier hosting. try webflow for free. Bleepingcomputer is a premier destination for cybersecurity news for over 20 years, delivering breaking stories on the latest hacks, malware threats, and how to protect your devices.

This App Lets You Practice Sql On Your Android Phone Techwiser Create custom, responsive websites with the power of code — visually. design and build your site with a flexible cms and top tier hosting. try webflow for free. Bleepingcomputer is a premier destination for cybersecurity news for over 20 years, delivering breaking stories on the latest hacks, malware threats, and how to protect your devices. Techtarget provides purchase intent insight powered solutions to identify, influence, and engage active buyers in the tech market. Analytics insight magazine's april issue dives into trust in ai giants, crypto as a risk barometer, india’s ai startups, nvidia’s revenue race, and the cybersecurity arms race shaping 2026. Ransomware is a type of malware that encrypts the victim's personal data until a ransom is paid. [1][2][3][4][5] difficult to trace digital currencies such as paysafecard or bitcoin and other cryptocurrencies are commonly used for the ransoms, making tracing and prosecuting the perpetrators difficult. sometimes the original files can be retrieved without paying the ransom due to implementation. Discover hundreds of marketing statistics and metrics on social media, content marketing, lead generation, email marketing, seo, aeo, sales, and more.

Android Basics Sql App Inspection Not Database In Newer Versions Techtarget provides purchase intent insight powered solutions to identify, influence, and engage active buyers in the tech market. Analytics insight magazine's april issue dives into trust in ai giants, crypto as a risk barometer, india’s ai startups, nvidia’s revenue race, and the cybersecurity arms race shaping 2026. Ransomware is a type of malware that encrypts the victim's personal data until a ransom is paid. [1][2][3][4][5] difficult to trace digital currencies such as paysafecard or bitcoin and other cryptocurrencies are commonly used for the ransoms, making tracing and prosecuting the perpetrators difficult. sometimes the original files can be retrieved without paying the ransom due to implementation. Discover hundreds of marketing statistics and metrics on social media, content marketing, lead generation, email marketing, seo, aeo, sales, and more.

Using Sql For Mobile App Analytics Datatas Ransomware is a type of malware that encrypts the victim's personal data until a ransom is paid. [1][2][3][4][5] difficult to trace digital currencies such as paysafecard or bitcoin and other cryptocurrencies are commonly used for the ransoms, making tracing and prosecuting the perpetrators difficult. sometimes the original files can be retrieved without paying the ransom due to implementation. Discover hundreds of marketing statistics and metrics on social media, content marketing, lead generation, email marketing, seo, aeo, sales, and more.
App Integration Sql For Mobile Apps Hire Sql
Comments are closed.