Spring Security Architecture Pdf Spring Framework Authentication

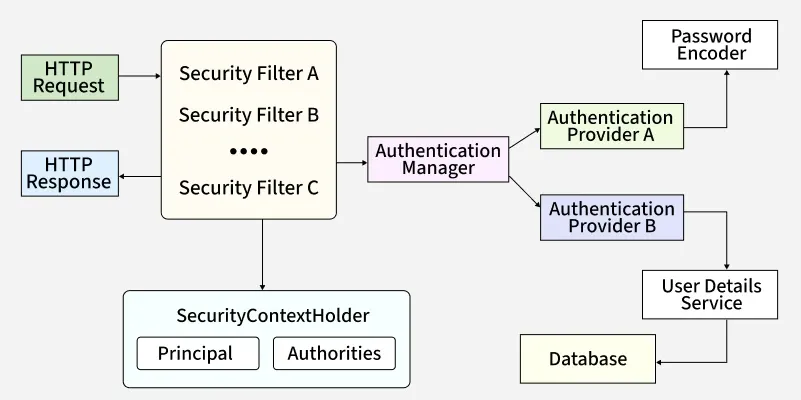
Spring Security Architecture Pdf Spring Framework Authentication At an authentication level, spring security supports a wide range of authentication models. most of these authentication models are either provided by third parties, or are developed by relevant standards bodies such as the internet engineering task force. The document provides a high level overview of the spring security architecture, which separates authentication and authorization into two independent problems.

Understanding Spring Security Architecture Jwt 54 Off This paper will shift its focus to explore advanced approaches to securing enterprise environments using the spring framework; specifically discussing topics such as json web token (jwt),. I’ll look at the main components of the framework, explain the work of the servlet filters for securing web applications, look at how spring aop (aspect oriented programming) helps you add security in an unobtrusive way, and in general, show how the framework is designed internally. It is the de facto standard for securing spring based applications, offering flexible integration with modern security mechanisms such as jwt, oauth2, ldap and database backed authentication. At this point — just know that the framework is a flexible, filter based framework where many different authentication schemes can be enabled. let’s take a look first at the core services used by the security filter chain.

Spring Security Pdf Spring Framework Autenticación It is the de facto standard for securing spring based applications, offering flexible integration with modern security mechanisms such as jwt, oauth2, ldap and database backed authentication. At this point — just know that the framework is a flexible, filter based framework where many different authentication schemes can be enabled. let’s take a look first at the core services used by the security filter chain. Build and deploy secure spring framework and spring boot based enterprise java applications with the spring security framework. this book explores a comprehensive set of functionalities to implement industry standard authentication and authorization mechanisms for java applications. Written by a lead cloud and security architect as well as cissp, this book helps you easily secure your java apps with spring security, a trusted and highly customizable authentication. Written by a lead cloud and security architect as well as cissp, this book helps you easily secure your java apps with spring security, a trusted and highly customizable authentication and access control framework. In this paper, the spring security framework is analyzed with the goal of identifying supported authentication and authorization patterns. additionally, a best practice guide on implementing the identified patterns using the framework is presented.
Spring Security Architecture Geeksforgeeks Build and deploy secure spring framework and spring boot based enterprise java applications with the spring security framework. this book explores a comprehensive set of functionalities to implement industry standard authentication and authorization mechanisms for java applications. Written by a lead cloud and security architect as well as cissp, this book helps you easily secure your java apps with spring security, a trusted and highly customizable authentication. Written by a lead cloud and security architect as well as cissp, this book helps you easily secure your java apps with spring security, a trusted and highly customizable authentication and access control framework. In this paper, the spring security framework is analyzed with the goal of identifying supported authentication and authorization patterns. additionally, a best practice guide on implementing the identified patterns using the framework is presented.
Comments are closed.