Splunk Threat Intelligence Platform Threatconnect

Threatconnect Threat Intelligence Operations Platform Reviews Ratings Using the threatconnect app for splunk, you can apply relevant threat intelligence to your infrastructure, mark false positives, and take immediate and automatic action on your intel. Threatconnect provides the ability to aggregate threat intelligence from multiple sources (open source, commercial, communities, and internally created), analyze and track identified adversary infrastructure and capabilities.

Threat Intelligence Platform Tip What Is A Tip The threatconnect ® application (app) for splunk ® gives splunk users the ability to leverage customizable threat intelligence integrated into splunk from their threatconnect accounts. Threatconnect offers substantial advantages in threat data enrichment, while splunk soar excels in integration with diverse systems, automation, and orchestration. The threatconnect app for splunk lets users configure indicator collections and data model searches, performs data model searches, and provides dashboards for analyzing data model search matches and indicator collections. Threatconnect this app integrates with the threatconnect platform to provide various hunting actions in addition to threat ingestion built by splunk llc log in to download.
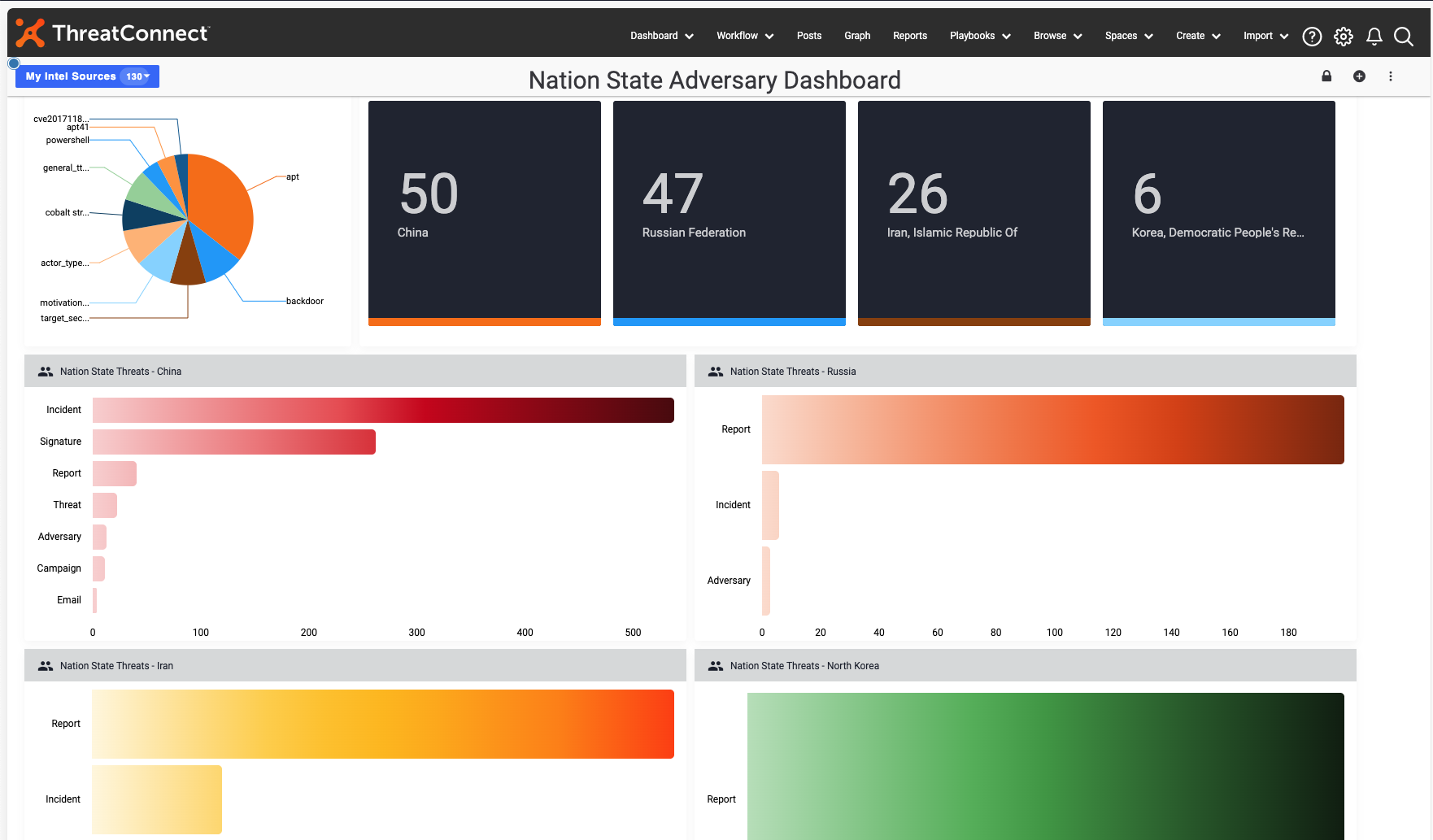
Threatconnect Extends Threat Intel Platform To Enable Ti Ops The threatconnect app for splunk lets users configure indicator collections and data model searches, performs data model searches, and provides dashboards for analyzing data model search matches and indicator collections. Threatconnect this app integrates with the threatconnect platform to provide various hunting actions in addition to threat ingestion built by splunk llc log in to download. With threatconnect, organizations infuse ml and ai powered threat intel and cyber risk quantification into their work, allowing them to orchestrate and automate processes to get the necessary insights and respond faster and more confidently than ever before. Threatconnect allows our organization to collect, analyze, and share intelligence with various teams in a single platform, effectively reducing the amount of time needed for an analyst to produce actionable intelligence to share with our partners and stakeholders. The threatconnect app for splunk lets users configure indicator collections and data model searches, performs data model searches, and provides dashboards for analyzing data model search matches and indicator collections. Leverage tailored, accurate, and timely threat intelligence refined and enriched from multiple sources, in cluding our collective analytics layer (cal) to reduce false positives.

Threatconnect Threat Intelligence Platform Tip Vs Threatmodeler With threatconnect, organizations infuse ml and ai powered threat intel and cyber risk quantification into their work, allowing them to orchestrate and automate processes to get the necessary insights and respond faster and more confidently than ever before. Threatconnect allows our organization to collect, analyze, and share intelligence with various teams in a single platform, effectively reducing the amount of time needed for an analyst to produce actionable intelligence to share with our partners and stakeholders. The threatconnect app for splunk lets users configure indicator collections and data model searches, performs data model searches, and provides dashboards for analyzing data model search matches and indicator collections. Leverage tailored, accurate, and timely threat intelligence refined and enriched from multiple sources, in cluding our collective analytics layer (cal) to reduce false positives.
Comments are closed.