Source Code Review Secure Session Management

Secure Source Code Review Sealcube This cheat sheet provides practical guidance for conducting effective manual security code reviews, with emphasis on both baseline and incremental review methodologies. This guideline highlights 8 focus areas, including authentication, authorisation, business logic & design, data management, exception handling, injection attack, logging & auditing, and session management that developers can focus on when reviewing code.

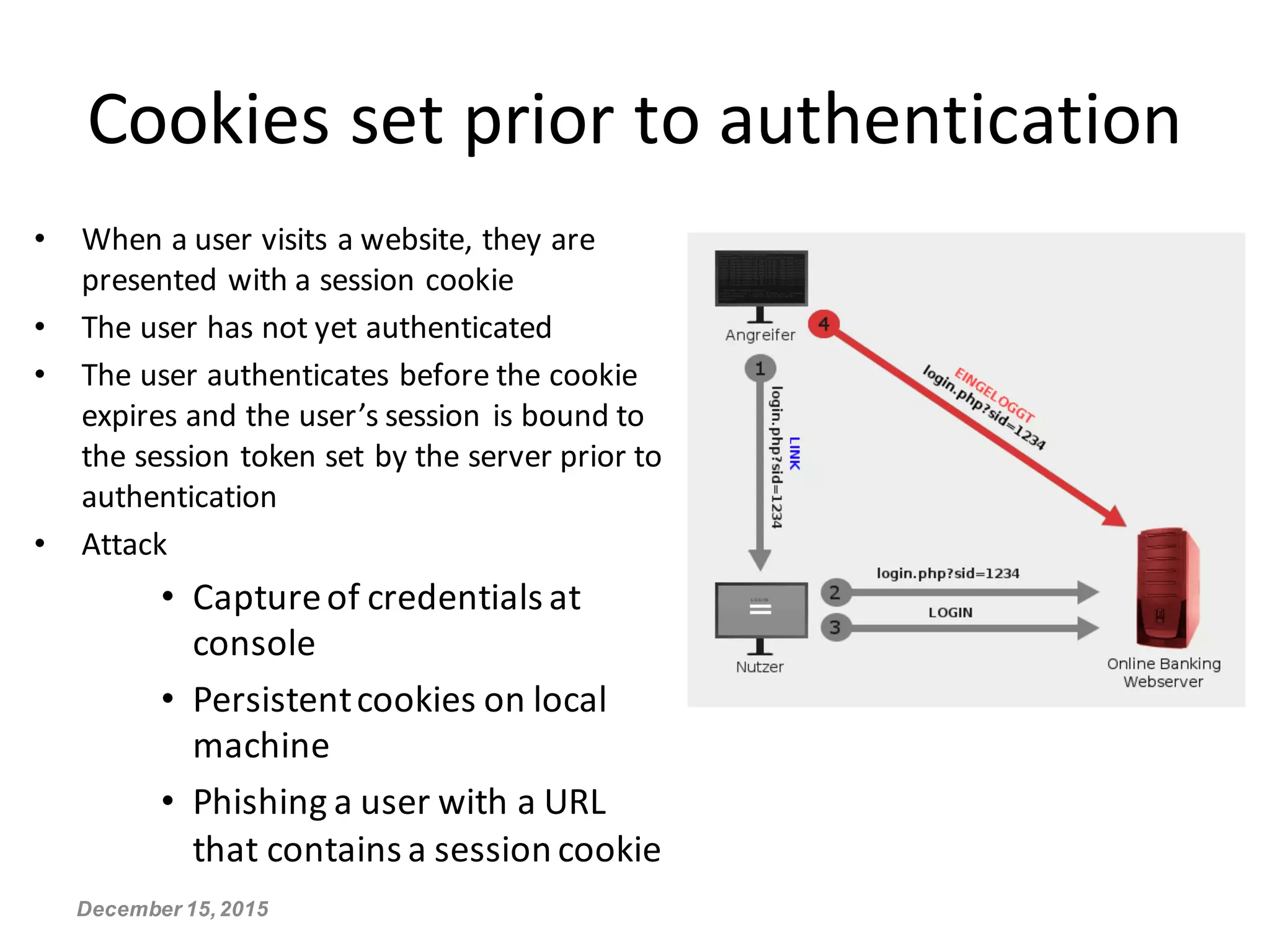
Secure Source Code Review Services In India Bangalore Kerala Wattlecorp Learn what is a secure code review, why it matters, and how to implement it. discover checklists, tools, and best practices for the sdlc to improve code security. Learn how to run secure code reviews that catch vulnerabilities early. explore process steps, tools, owasp tips, and real world coding practices. In this blog post, we will delve into the details of broken authentication and session management vulnerabilities, how to identify them during a secure code review, and what measures can be taken to prevent them. ⚠️ disclaimer: while these code review snippets provide guidance for secure coding, they are not exhaustive. it is crucial to understand the unique security requirements of your project and conduct thorough testing to ensure robust security measures.

Secure Session Management Cheat Sheet In this blog post, we will delve into the details of broken authentication and session management vulnerabilities, how to identify them during a secure code review, and what measures can be taken to prevent them. ⚠️ disclaimer: while these code review snippets provide guidance for secure coding, they are not exhaustive. it is crucial to understand the unique security requirements of your project and conduct thorough testing to ensure robust security measures. In this video, we’ll break down secure sessio. Explore the ultimate code review security checklist. learn why secure code review matters, how to build a java checklist, and use owasp guidelines for safer development. Secure code review is a process used to identify potential security vulnerabilities in software source code. it is an important part of a secure sdlc process and can be used to detect common coding flaws such as buffer overflows, sql injection, and cross site scripting. So how do you review code for security without going mad or becoming the villain of the sprint? let’s break it down.
What Is A Secure Code Review And When Should You Do It Ip With Ease In this video, we’ll break down secure sessio. Explore the ultimate code review security checklist. learn why secure code review matters, how to build a java checklist, and use owasp guidelines for safer development. Secure code review is a process used to identify potential security vulnerabilities in software source code. it is an important part of a secure sdlc process and can be used to detect common coding flaws such as buffer overflows, sql injection, and cross site scripting. So how do you review code for security without going mad or becoming the villain of the sprint? let’s break it down.

Secure Source Code Review Services In Bengaluru India Wattlecorp Secure code review is a process used to identify potential security vulnerabilities in software source code. it is an important part of a secure sdlc process and can be used to detect common coding flaws such as buffer overflows, sql injection, and cross site scripting. So how do you review code for security without going mad or becoming the villain of the sprint? let’s break it down.
Secure Session Management Pdf
Comments are closed.