Solved Implement S Aes Cipher Encryption And Decryption Chegg
Solved Implement S Aes Simplified Advanced Encryption Chegg Implement s aes cipher (encryption and decryption) in c c , python or java. your solution’s ready to go! our expert help has broken down your problem into an easy to learn solution you can count on. question: implement s aes cipher (encryption and decryption) in c c , python or java. Implement s aes cipher (encryption and decryption) in c c , python, or java. s aes: the encryption algorithm takes a 16 bit block of plaintext as input and a 16 bit key and produces a 16 bit block of ciphertext as output.

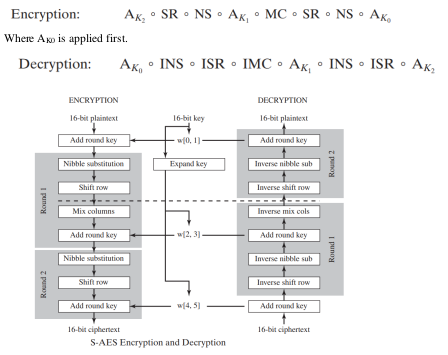
Implement S Aes Simplified Advanced Chegg This project implements a simplified version of the advanced encryption standard (s aes), which performs encryption and decryption on 16 bit data blocks using 16 bit keys. Here are some tips to help you solve the encryption and decryption problem using s aes: understand s aes: familiarize yourself with the structure and steps involved in the s aes algorithm. Now we have the final ciphertext. now lets decrypt. note that we use the same keys generated during the encryption (that is, the decryptor would generate the round sub keys using the input key k, using the encryption s box). the decryption worked!. Unlike des, the decryption algorithm differs substantially from the encryption algorithm. although, overall, very similar steps are used in encryption and decryption, their implementations are not identical and the order in which the steps are invoked is different, as mentioned previously.
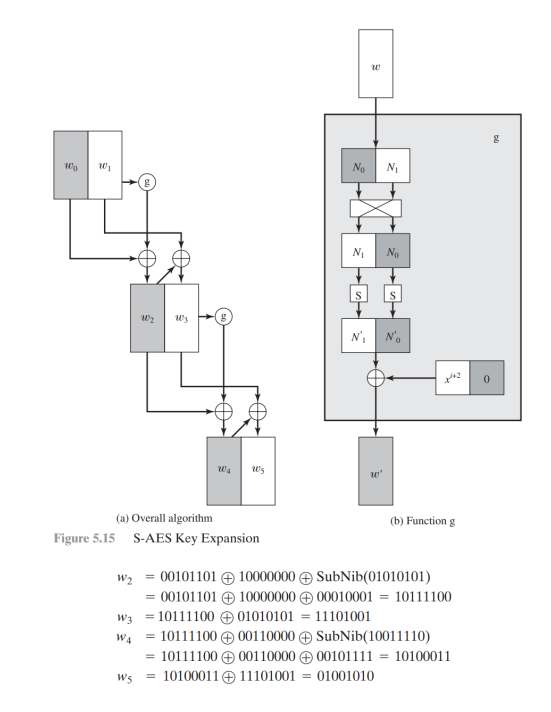
Implement S Aes Simplified Advanced Chegg Now we have the final ciphertext. now lets decrypt. note that we use the same keys generated during the encryption (that is, the decryptor would generate the round sub keys using the input key k, using the encryption s box). the decryption worked!. Unlike des, the decryption algorithm differs substantially from the encryption algorithm. although, overall, very similar steps are used in encryption and decryption, their implementations are not identical and the order in which the steps are invoked is different, as mentioned previously. In fact, the structure of s aes is exactly the same as aes. the differences are in the key size (16 bits), the block size (16 bits) and the number of rounds (2 rounds). In the world of cryptography, security and simplicity are often at odds. but what if there was a way to bridge the gap between understanding cryptography and actually doing robust encryption? a few months ago, i found out that there is a simplified version of aes, called simplified aes (s aes). Let's illustrate the aes encryption and aes decryption concepts through working source code in python. the first example below will illustrate a simple password based aes encryption (pbkdf2 aes ctr) without message authentication (unauthenticated encryption). The algorithms were implemented using c. the following sections show how an encryption or decryption can be calculated using the functions provided in this application report.
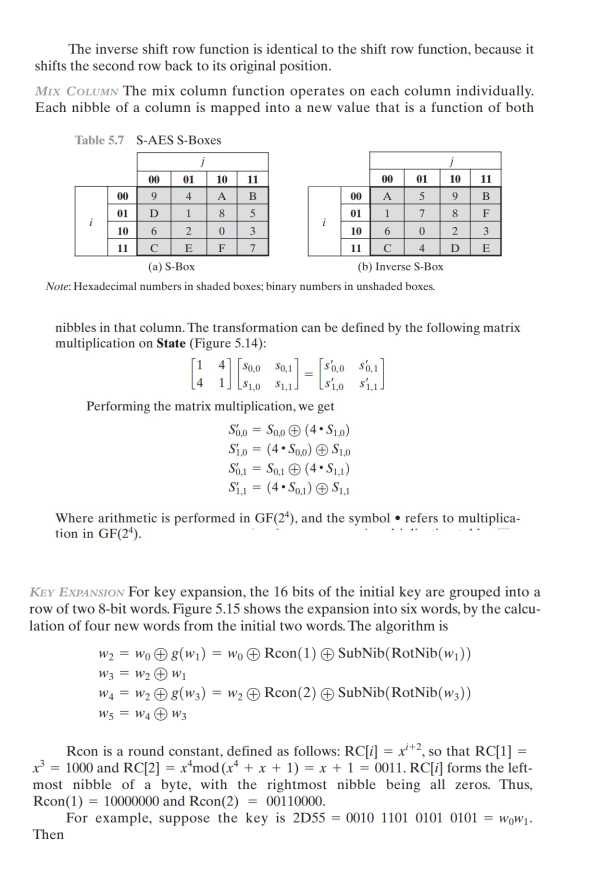
Implement S Aes Simplified Advanced Chegg In fact, the structure of s aes is exactly the same as aes. the differences are in the key size (16 bits), the block size (16 bits) and the number of rounds (2 rounds). In the world of cryptography, security and simplicity are often at odds. but what if there was a way to bridge the gap between understanding cryptography and actually doing robust encryption? a few months ago, i found out that there is a simplified version of aes, called simplified aes (s aes). Let's illustrate the aes encryption and aes decryption concepts through working source code in python. the first example below will illustrate a simple password based aes encryption (pbkdf2 aes ctr) without message authentication (unauthenticated encryption). The algorithms were implemented using c. the following sections show how an encryption or decryption can be calculated using the functions provided in this application report.
Comments are closed.