Solved 5 We May Generalize The Affine Cipher To A Hill Chegg

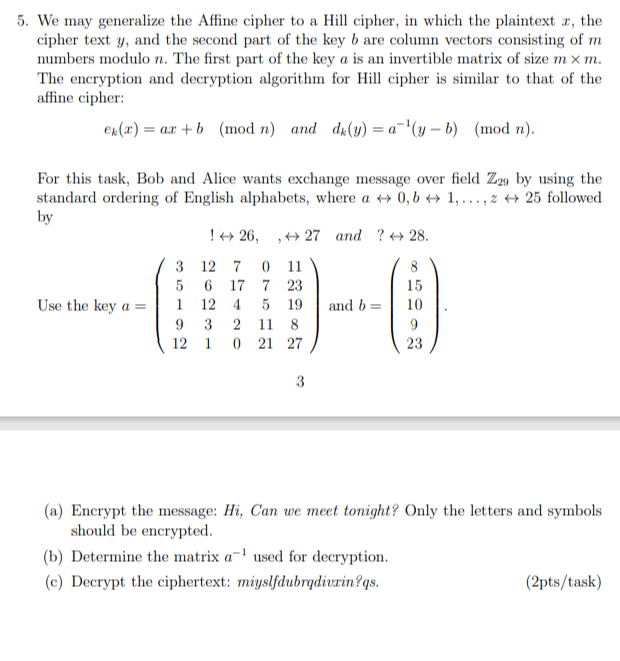
Hill Cipher Problem Pdf Cryptography Secure Communication The encryption and decryption algorithm for hill cipher is similar to that of the affine cipher: please read the question carefully and solve all 3 parts (a,b,c). We may generalize the affine cipher to a hill cipher, in which the plaintext, the ciphertext y, and the second part of the key b are column vectors consisting of m numbers modulo n.
Solved 5 We May Generalize The Affine Cipher To A Hill Chegg Hill disrupts monogram frequency more than monoalphabetic ciphers because letters influence each other within a block. however, it is still structured: ciphertext remains alphabetic and often has more uniform looking distributions than caesar affine. Master the hill cipher through comprehensive step by step examples that progress from simple 2x2 matrix encryption to advanced 3x3 implementations and cryptanalysis techniques. these examples provide complete calculations, demonstrating every stage of the encryption and decryption process. The questions cover topics like cryptanalysis techniques for affine ciphers, possible keys in cryptosystems, modes of operation for block ciphers, hill cipher encryption, vigenere cipher analysis, feistel networks, and more. Hill cipher is a polygraphic substitution cipher based on linear algebra. in this method, each letter of the alphabet is represented by a number modulo 26, commonly using the scheme a = 0, b = 1, …, z = 25.
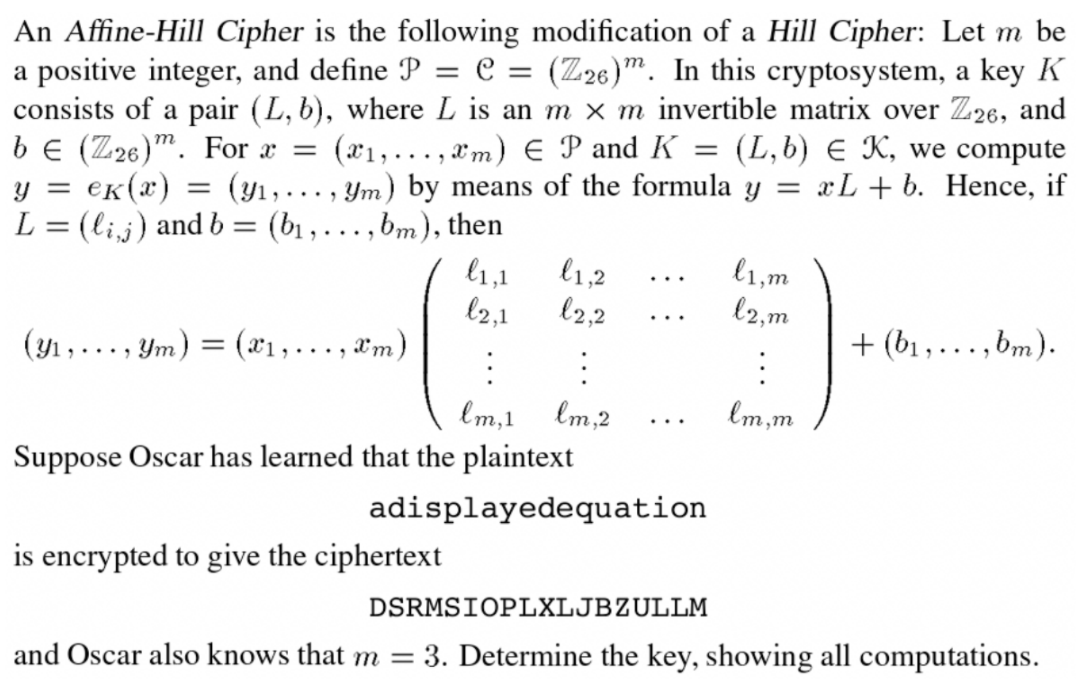
Solved An Affine Hill Cipher Is The Following Modification Chegg The questions cover topics like cryptanalysis techniques for affine ciphers, possible keys in cryptosystems, modes of operation for block ciphers, hill cipher encryption, vigenere cipher analysis, feistel networks, and more. Hill cipher is a polygraphic substitution cipher based on linear algebra. in this method, each letter of the alphabet is represented by a number modulo 26, commonly using the scheme a = 0, b = 1, …, z = 25. Hill cipher is a polyalphabetic cipher created by extending the affine cipher, using linear algebra and modular arithmetic via a numeric matrix that serves as an encryption and decryption key. We convert the numbers to characters, column wise and obtain the original message: dea r m om sen d m one y that is: dear mom send money note that the number of characters in the original message is 19, which is not a multiple of 3. In the examples given, we shall walk through all the steps to use this cipher to act on digraphs and trigraphs. it can be extended further, but this then requires a much deeper knowledge of the background mathematics. We may generalize the affine cipher to a hill cipher, in which the plaintext x, the cipher text y, and the second part of the key b are column vectors consisting of m numbers modulo n.
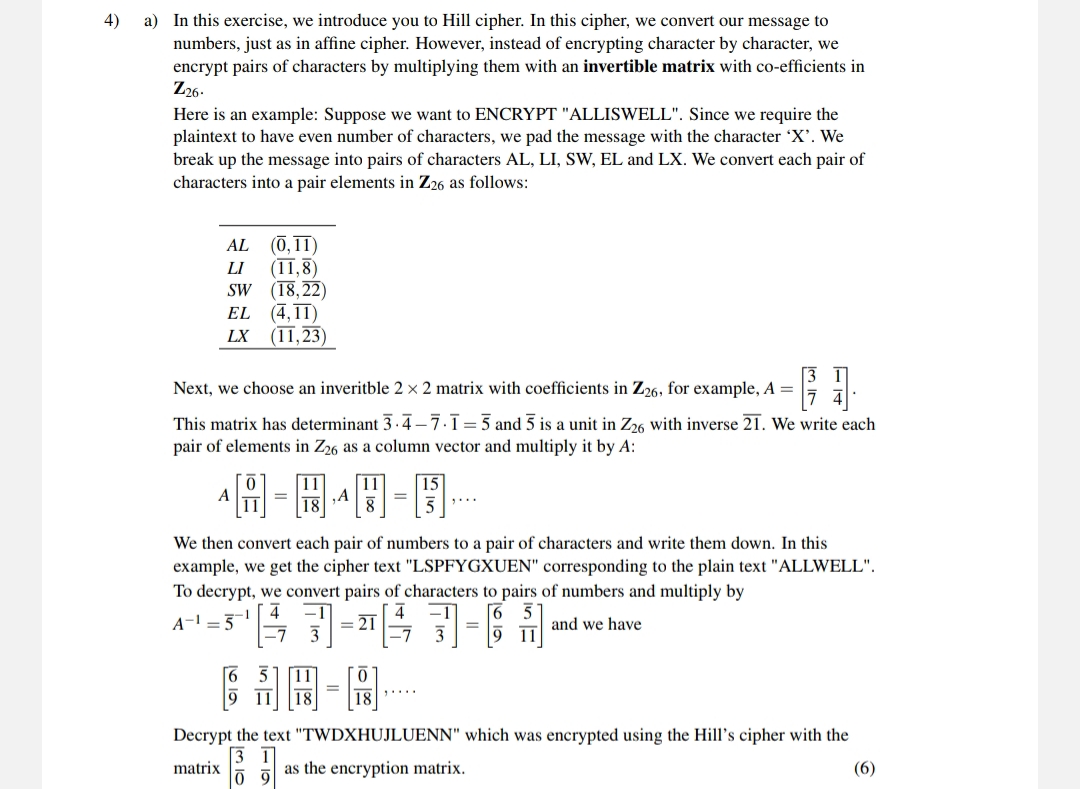
Solved A In This Exercise We Introduce You To Hill Cipher Chegg Hill cipher is a polyalphabetic cipher created by extending the affine cipher, using linear algebra and modular arithmetic via a numeric matrix that serves as an encryption and decryption key. We convert the numbers to characters, column wise and obtain the original message: dea r m om sen d m one y that is: dear mom send money note that the number of characters in the original message is 19, which is not a multiple of 3. In the examples given, we shall walk through all the steps to use this cipher to act on digraphs and trigraphs. it can be extended further, but this then requires a much deeper knowledge of the background mathematics. We may generalize the affine cipher to a hill cipher, in which the plaintext x, the cipher text y, and the second part of the key b are column vectors consisting of m numbers modulo n.
Comments are closed.