Solved 2 Affine Cipher A Encrypt The Plaintext Message Chegg
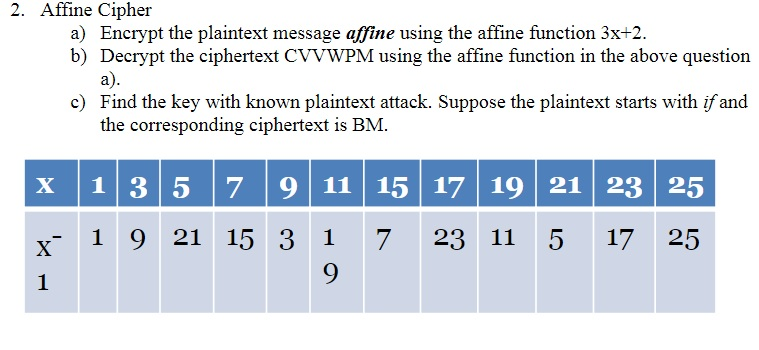
Solved 2 Affine Cipher A Encrypt The Plaintext Message Chegg Affine cipher a) encrypt the plaintext message affine using the affine function 3x 2. b) decrypt the ciphertext cvvwpm using the affine function in the above question a). In deciphering the ciphertext, we must perform the opposite (or inverse) functions on the ciphertext to retrieve the plaintext. once again, the first step is to convert each of the ciphertext letters into their integer values.
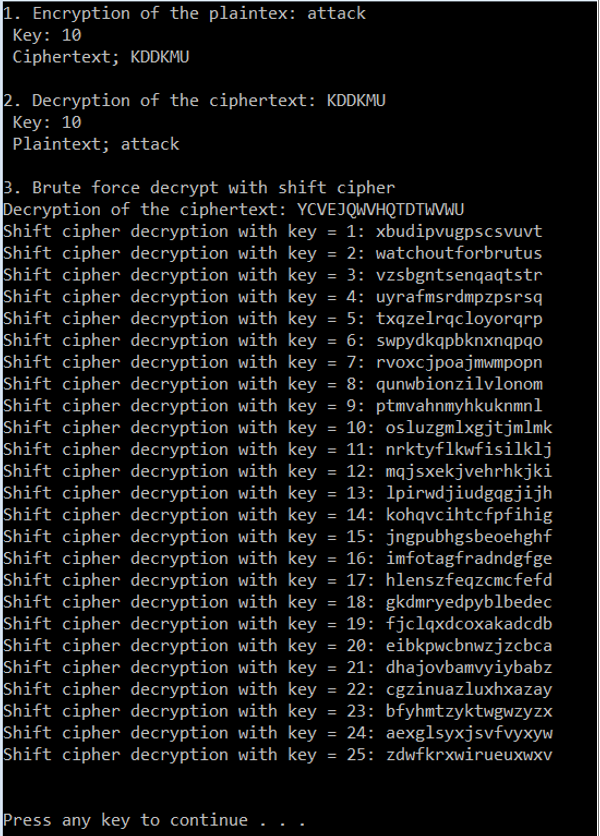
Solved Affine Cipher Encrypt The Plaintext Message Chegg You are trying to break an affine cipher mod 26 using a chosen plaintext attack. you choose the plaintext nonono, and the corresponding ciphertext is returned as wrwrwr. The affine cipher represents one of the oldest and most elegant mathematical approaches to encryption. combining multiplication and addition in modular arithmetic, it transforms plaintext into ciphertext using two numeric keys. Armed with the encrypting function (i.e., the "secret key" for the affine cipher), decrypting the message is straight forward just determine what each letter becomes under the function, and do the substitutions backwards. Answer to affine ciphers: 1. encrypt the plaintext message.
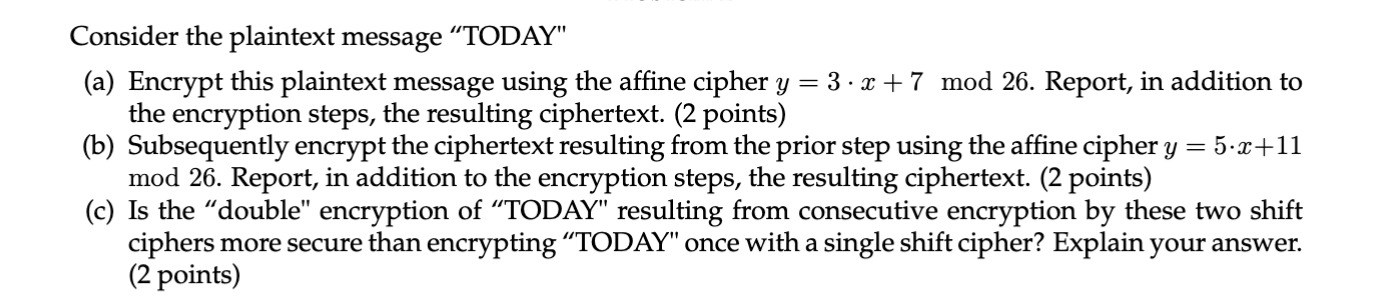
Solved Consider The Plaintext Message Today A Encrypt Chegg Armed with the encrypting function (i.e., the "secret key" for the affine cipher), decrypting the message is straight forward just determine what each letter becomes under the function, and do the substitutions backwards. Answer to affine ciphers: 1. encrypt the plaintext message. Suppose you encrypt using an affine cipher, then encrypt the encryp tion using another affine cipher (both are working mod 26). is there any advantage to doing this, rather than using a single affine cipher?!. Problem2: affine cipher the affine cipher is a type of monoalphabetic substitution cipher that employs modular arithmetic to encrypt the letters of a message. the encryption formula is c = (a * p b) mod n, where 'p' is the plaintext letter, 'c' is the ciphertext letter, 'n' is the modulus. 'a' and 'b' are keys, and. Prove that if a message in encrypted by an affine cipher, and then encrypted again by a differ nt affine cipher, this is equivalent to encrypting the message by a single, third affine cipher. here’s the best way to solve it. 2. the ciphertext crwwz was encrypted by an affine cipher. Examples are provided to illustrate the encryption and decryption process. practice problems are included at the end to encrypt and decrypt plaintexts using given affine cipher keys.
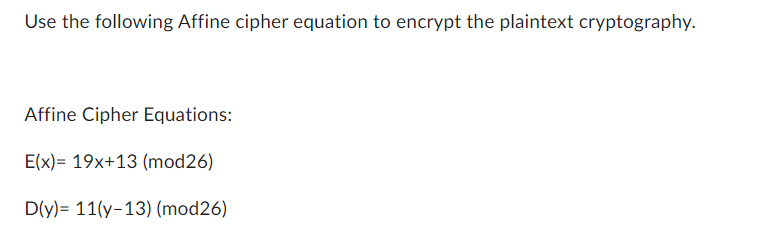
Solved Use The Following Affine Cipher Equation To Encrypt Chegg Suppose you encrypt using an affine cipher, then encrypt the encryp tion using another affine cipher (both are working mod 26). is there any advantage to doing this, rather than using a single affine cipher?!. Problem2: affine cipher the affine cipher is a type of monoalphabetic substitution cipher that employs modular arithmetic to encrypt the letters of a message. the encryption formula is c = (a * p b) mod n, where 'p' is the plaintext letter, 'c' is the ciphertext letter, 'n' is the modulus. 'a' and 'b' are keys, and. Prove that if a message in encrypted by an affine cipher, and then encrypted again by a differ nt affine cipher, this is equivalent to encrypting the message by a single, third affine cipher. here’s the best way to solve it. 2. the ciphertext crwwz was encrypted by an affine cipher. Examples are provided to illustrate the encryption and decryption process. practice problems are included at the end to encrypt and decrypt plaintexts using given affine cipher keys.
Comments are closed.