Solution Cyber Security Virtualization Studypool

Practical Guide Virtualization Security Pdf Virtualization In this paper, a discussion of computer virtualization will be given and the benefits of using virtual computers in the it industry. management and access to information, when stored on virtual facilities, makes it easier for the management and staff to handle tasks. After researching our problem on cyber security benefits due to virtualization, we found multiple solutions to improve the security system and efficiency of our data transmission in this virtualized networking system.

Virtualization Security A Complete Guide Cyberexperts We provide an exhaustive comparison of various techniques proposed by researchers to resolve virtualization specific vulnerabilities. to guide future research, we discussed generalized security. In this paper we address the security risks induced by virtualization in cloud services are analyzed and suggested a virtualization security framework and propose its solution approaches. In this article, we describe and compare these virtualization models, in order to establish a reference architecture of cloud infrastructure. we then analyze the security issues related to these models from the reference architecture, by considering related vulnerabilities and attacks. Learn virtualization security in cloud computing: hypervisor protection, vm hardening, threat mitigation for aws, azure & gcp. secure your cloud infrastructure today.
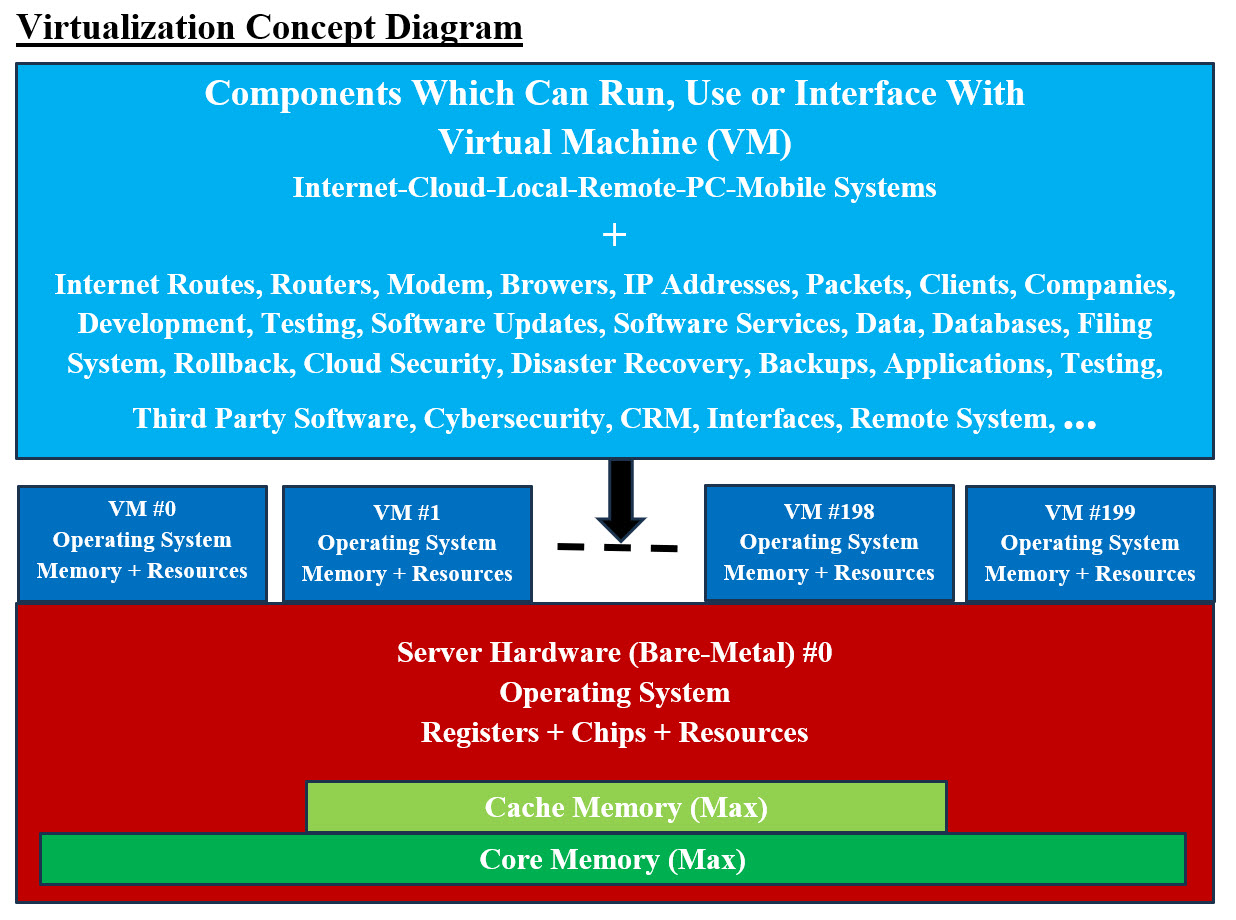
Using Virtualization In Cybersecurity In this article, we describe and compare these virtualization models, in order to establish a reference architecture of cloud infrastructure. we then analyze the security issues related to these models from the reference architecture, by considering related vulnerabilities and attacks. Learn virtualization security in cloud computing: hypervisor protection, vm hardening, threat mitigation for aws, azure & gcp. secure your cloud infrastructure today. Virtualization provides some significant security advantages compared to traditional server infrastructure, but it isn't risk free either. learn more about its risks. We provide an exhaustive comparison of various techniques proposed by researchers to resolve virtualization specific vulnerabilities. to guide future research, we discussed generalized security measures and requirements to be taken to achieve secure virtualized implementations. There are many forms of virtualization, distinguished primarily by computing architecture layer. this publication focuses on the form of virtualization known as full virtualization. in full virtualization, one or more oss and the applications they contain are run on top of virtual hardware. Our article emphasize on the assessment of virtualization specific vulnerabilities, security issues and possible solutions. in this article, a recent comprehensive survey on virtualization threats and vulnerabilities is presented.

Solution Cyber Security Virtualization Studypool Virtualization provides some significant security advantages compared to traditional server infrastructure, but it isn't risk free either. learn more about its risks. We provide an exhaustive comparison of various techniques proposed by researchers to resolve virtualization specific vulnerabilities. to guide future research, we discussed generalized security measures and requirements to be taken to achieve secure virtualized implementations. There are many forms of virtualization, distinguished primarily by computing architecture layer. this publication focuses on the form of virtualization known as full virtualization. in full virtualization, one or more oss and the applications they contain are run on top of virtual hardware. Our article emphasize on the assessment of virtualization specific vulnerabilities, security issues and possible solutions. in this article, a recent comprehensive survey on virtualization threats and vulnerabilities is presented.

Solution Cyber Security Virtualization Studypool There are many forms of virtualization, distinguished primarily by computing architecture layer. this publication focuses on the form of virtualization known as full virtualization. in full virtualization, one or more oss and the applications they contain are run on top of virtual hardware. Our article emphasize on the assessment of virtualization specific vulnerabilities, security issues and possible solutions. in this article, a recent comprehensive survey on virtualization threats and vulnerabilities is presented.

Virtualization Cloud Ciasys Www Ciasys Home
Comments are closed.