Solution Cryptography Practice Question And Answer Studypool

Cryptography Answer Pdf Public Key Cryptography Cryptography Get help with homework questions from verified tutors 24 7 on demand. access 20 million homework answers, class notes, and study guides in our notebank. This document contains solutions to exercises from the textbook "cryptography theory and practice, second edition". it provides final answers for computational questions and detailed proofs for mathematical questions.

Solution Cryptography Practice Question And Answer Studypool Solution manual for cryptography theory and practice, 2nd edition. includes answers and proofs for exercises on classical cryptography, rsa, and more. This manual contains solutions to all of the review questions and homework problems in cryptography and network security, fourth edition. if you spot an error in a solution or in the wording of a problem, i would greatly appreciate it if you would forward the information via email to ws@shore. This manual contains solutions to the review questions and homework problems in cryptography and network security, eighth edition. if you spot an error in a solution or in the wording of a problem, i would greatly appreciate it if you would forward the information via email to wllmst@me . A comprehensive set of practice questions and answers covering various aspects of cryptography, including hashing algorithms, symmetric and asymmetric encryption, key sizes, block cipher modes, and more.
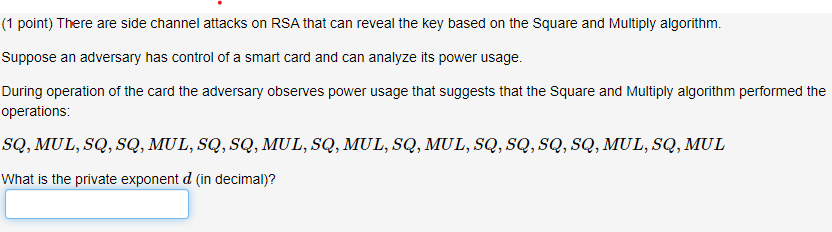
Cryptography Question Chegg This manual contains solutions to the review questions and homework problems in cryptography and network security, eighth edition. if you spot an error in a solution or in the wording of a problem, i would greatly appreciate it if you would forward the information via email to wllmst@me . A comprehensive set of practice questions and answers covering various aspects of cryptography, including hashing algorithms, symmetric and asymmetric encryption, key sizes, block cipher modes, and more. Our shop specializes in original publisher content, including solutions manuals, test banks, and comprehensive study guides that are ideal for university and college students across various subjects. The reader is warned that in practice it is often more efficient to use other ladder algorithms than traditional square and multiply, see chapter 3 of stam [579]. 6.4.12: the trick is to represent tn using the triple (tn 1, tn, tn−1) as above when n is odd, but (tn 2, tn 1, tn) when n is even. Part 1 select the case studies located in the course textbook at the end of chapters 21, 24, and answer the questions associated with those case studies in a cohesive, apa formatted paper. Starting with the origins of cryptography, it moves on to explain cryptosystems, various traditional and modern ciphers, public key encryption, data integration, message authentication, and digital signatures.

Cryptography And Network Security Question Bank Unit Answer Pdf Our shop specializes in original publisher content, including solutions manuals, test banks, and comprehensive study guides that are ideal for university and college students across various subjects. The reader is warned that in practice it is often more efficient to use other ladder algorithms than traditional square and multiply, see chapter 3 of stam [579]. 6.4.12: the trick is to represent tn using the triple (tn 1, tn, tn−1) as above when n is odd, but (tn 2, tn 1, tn) when n is even. Part 1 select the case studies located in the course textbook at the end of chapters 21, 24, and answer the questions associated with those case studies in a cohesive, apa formatted paper. Starting with the origins of cryptography, it moves on to explain cryptosystems, various traditional and modern ciphers, public key encryption, data integration, message authentication, and digital signatures.

Grade 6 Cryptography Problem Set Pdf Encryption Cipher Part 1 select the case studies located in the course textbook at the end of chapters 21, 24, and answer the questions associated with those case studies in a cohesive, apa formatted paper. Starting with the origins of cryptography, it moves on to explain cryptosystems, various traditional and modern ciphers, public key encryption, data integration, message authentication, and digital signatures.
Comments are closed.