Solution Cryptography And Network Security Full Notes To Understand
Cryptography And Network Security Notes Pdf Cryptography can reformat and transform our data, making it safer on its trip between computers. the technology is based on the essentials of secret codes, augmented by modern mathematics that protects our data in powerful ways. An assault on system security that derives from an intelligent threat; that is, an intelligent act that is a deliberate attempt (especially in the sense of a method or technique) to evade security services and violate the security policy of a system.

Network Security Cryptography Full Notes Pdf Network security model exhibits how the security service has been designed over the network to prevent the opponent from causing a threat to the confidentiality or authenticity of the information that is being transmitted through the network. This repository is dedicated to providing detailed and well organized lecture notes for the "cryptography and network security" course. each lecture note is designed to help students understand fundamental concepts and practical implementations essential for understanding a particular topic. One of the most specific security mechanisms in use is cryptographic techniques. encryption or encryption like transformations of information are the most common means. These two developments lead to ‘computer security’ and ‘network security’, where the computer security deals with collection of tools designed to protect data and to thwart hackers.
Cryptography And Network Security Principles And Practice Araavat One of the most specific security mechanisms in use is cryptographic techniques. encryption or encryption like transformations of information are the most common means. These two developments lead to ‘computer security’ and ‘network security’, where the computer security deals with collection of tools designed to protect data and to thwart hackers. The paper discusses key challenges in cryptography, specifically focusing on the generation of random keys and their distribution for secure communication. several encryption methodologies, such as transposition ciphers and steganography, are explored, along with their implications and weaknesses. Loading…. Computer security generic name for the collection of tools designed to protect data and to prevent hackers. network security measures to protect data during their transmission. internet security measures to protect data during their transmission over a collection of interconnected networks. Comprehensive solutions manual for the 8th edition of cryptography and network security by william stallings, covering key concepts, problems, and exercises in modern cryptographic techniques and netw.
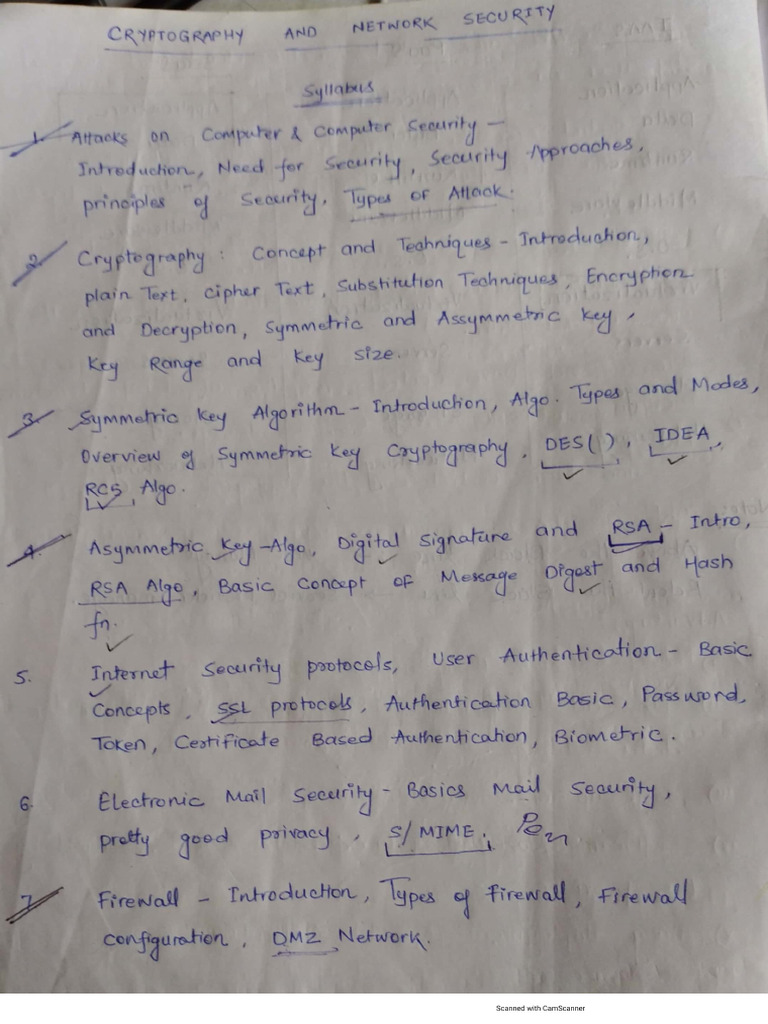
Cryptography And Network Security Notes Pdf The paper discusses key challenges in cryptography, specifically focusing on the generation of random keys and their distribution for secure communication. several encryption methodologies, such as transposition ciphers and steganography, are explored, along with their implications and weaknesses. Loading…. Computer security generic name for the collection of tools designed to protect data and to prevent hackers. network security measures to protect data during their transmission. internet security measures to protect data during their transmission over a collection of interconnected networks. Comprehensive solutions manual for the 8th edition of cryptography and network security by william stallings, covering key concepts, problems, and exercises in modern cryptographic techniques and netw.
Comments are closed.