Solution Building A Threat Intelligence Program Studypool

Building Threat Intelligence Program Threat Intelligence Program It is based on material originally posted on the securosis blog, but has been enhanced, reviewed, and professionally edited. special thanks to chris pepper for editing and content support. this report is licensed by lookingglass cyber solutions. their support allows us to release it for free. Part 3 this week’s interactive assignment, you will continue building your concept map presentation you began in week 1 to illustrate and make connections between the concepts of computer systems.

Building A Threat Intelligence Program Growing The Program In a 4 page report, please discuss and provide greater details on the factors that can either contribute to the success or failure of the development of a commercial cyber threat intelligence program. In this in depth guide, we’ll walk you through the process of building a threat intelligence program tailored to your organization’s needs. let’s dive in! 1. defining your objectives and. Results the main results of this project were in the research, design and building of a cyber threat intelligence program. 27 sources were found and ranked, along with the building of a threat score card. Core objectives of a cti program the primary objective of cti is to provide actionable intelligence that reduces cyber risk. fit supports prevention, detection, response, and strategic planning across security operations.
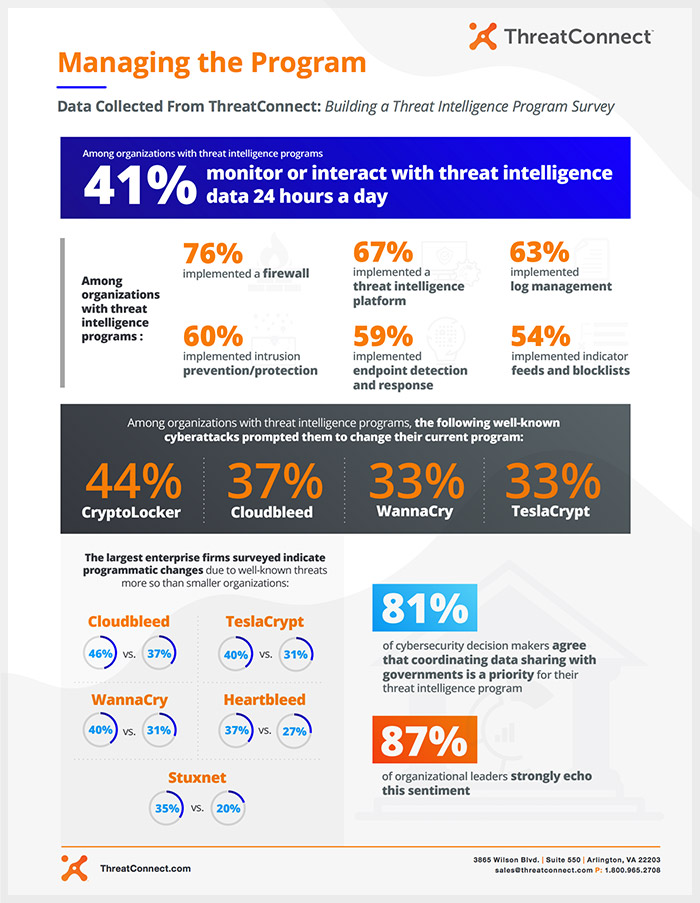
Building A Threat Intelligence Program Managing The Program Results the main results of this project were in the research, design and building of a cyber threat intelligence program. 27 sources were found and ranked, along with the building of a threat score card. Core objectives of a cti program the primary objective of cti is to provide actionable intelligence that reduces cyber risk. fit supports prevention, detection, response, and strategic planning across security operations. Those who describe their threat intelligence program as more mature than their competitors’ are often utilizing threat intelligence platforms to aggregate and monitor data in one place. This white paper provides a practical blueprint for building or strengthening a modern threat intelligence program. Thanks to the intelligence information, you can build necessary defense mechanisms before attacks and you can get the chance to be one step ahead of attackers. if you know others and know yourself, you will not be beaten in a hundred battles. This is a comprehensive guide that will teach you how to build a threat intelligence program from scratch. we'll go through each step of the process, and explain the different pieces of the.

Building A Threat Intelligence Program Securosis Those who describe their threat intelligence program as more mature than their competitors’ are often utilizing threat intelligence platforms to aggregate and monitor data in one place. This white paper provides a practical blueprint for building or strengthening a modern threat intelligence program. Thanks to the intelligence information, you can build necessary defense mechanisms before attacks and you can get the chance to be one step ahead of attackers. if you know others and know yourself, you will not be beaten in a hundred battles. This is a comprehensive guide that will teach you how to build a threat intelligence program from scratch. we'll go through each step of the process, and explain the different pieces of the.
Comments are closed.