Solid State Identification And Authentication
Solid State Identification And Authentication Rogerio talks about markets and solutions for solid state authentication devices. By possessing a secured identity, we are given the freedom to access services that require proof of id, share and receive information from trustful sources, perform legal actions, and safeguard privacy – both, in the physical and virtual world.
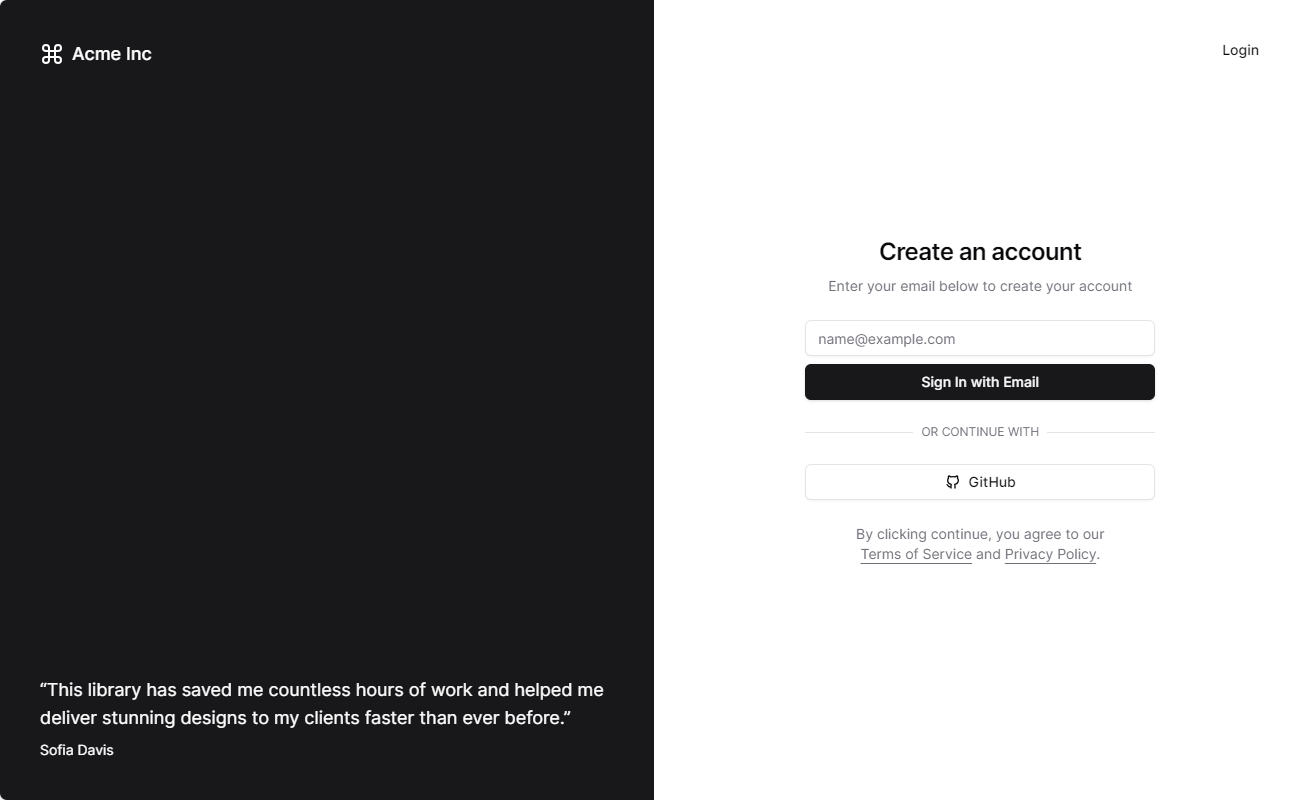
Example Shadcn Solid This chapter discusses the basic means of identification and authentication, the current technology used to provide i&a, and some important implementation issues. The pcie ssd verification environment can be ported to any pcie based ssds with minimal effort. samsung were familiar with the simulation vip it seemed to make sense to continue using it. In this work, we present a new smart hardware security engine that combines three different sources of entropy, ecg, heart rate variability (hrv), and sram based physical unclonable function (puf) to perform real time authentication and generate unique random signatures. Principal offices, employees, contractors, external service providers and system users are required to comply with these identification and authentication control standards.

Identification Vs Authentication What S The Difference In this work, we present a new smart hardware security engine that combines three different sources of entropy, ecg, heart rate variability (hrv), and sram based physical unclonable function (puf) to perform real time authentication and generate unique random signatures. Principal offices, employees, contractors, external service providers and system users are required to comply with these identification and authentication control standards. In this paper, we investigate the identification and authentication of wireless devices using the physical properties (physical layer authentication) in their transmission components, which generate specific analogical artifacts in their rf emissions. In this paper, we investigate the identification and authentication of wireless devices using the physical properties (physical layer authentication) in their transmission components, which. An on line sensor is used for fingerprint verification and is called “live scan fingerprint capture” and it is divided into 3 sub types: 1) ultrasound, 2) optical and 3) solid state fingerprint sensors. Solid state imaging device, and light detector and authentication equipment using the same download pdf.

State Of Authentication Report Secureauth In this paper, we investigate the identification and authentication of wireless devices using the physical properties (physical layer authentication) in their transmission components, which generate specific analogical artifacts in their rf emissions. In this paper, we investigate the identification and authentication of wireless devices using the physical properties (physical layer authentication) in their transmission components, which. An on line sensor is used for fingerprint verification and is called “live scan fingerprint capture” and it is divided into 3 sub types: 1) ultrasound, 2) optical and 3) solid state fingerprint sensors. Solid state imaging device, and light detector and authentication equipment using the same download pdf.
Comments are closed.