Software Supply Chain Security Programs Challenges Evaluating Tools

Software Supply Chain Security Programs Challenges Evaluating Tools If you’re implementing a software supply chain security program, be aware of the following challenges you may face, along with some questions to ask as you evaluate new tools and. Learn best practices and mistakes to avoid when implementing effective software supply chain security protocols.

5 Steps To Increase Your Software Supply Chain Security Program We’ll walk through the key tools you can use to secure your pipelines, emerging standards like slsa and sboms, and the real world challenges developers face while integrating supply chain security practices into their daily workflows. This guide expounds the principles and practices of this new approach, from foundational concepts to frameworks, tools, and defensive strategies necessary for contemporary software supply chain security. Understanding these challenges is the first step toward building effective supply chain security. the organizations that succeed don't just add more security tools, they fundamentally rethink how security integrates with development workflows. In this paper, we first introduce a taxonomy of ssc attacks and their corresponding mitigation controls, providing a structured understanding of the diverse threats facing software vendors and users, and the strategies to address them.

What Is Software Supply Chain Security And Why Does It Matter Understanding these challenges is the first step toward building effective supply chain security. the organizations that succeed don't just add more security tools, they fundamentally rethink how security integrates with development workflows. In this paper, we first introduce a taxonomy of ssc attacks and their corresponding mitigation controls, providing a structured understanding of the diverse threats facing software vendors and users, and the strategies to address them. It also provides in depth recommendations and key steps for prevention, mitigation, and resilience of software supply chain attacks. Introduction this report is based on a survey of it and security professionals responsible for software supply chain security. the survey reveals a cohort that overestimates the maturity of their software supply chain security efforts even as they grapple with significant challenges. We address the multifaceted challenges in securing the software supply chain, the limitations of current approaches, and how recent research contributes to the solution space. This article contains perspectives and knowledge obtained from intentional outreach with practitioners to understand their practical challenges and from extensive research efforts. we then provide an overview of current research efforts to secure the software supply chain.

Top 9 Software Supply Chain Security Tools Jit It also provides in depth recommendations and key steps for prevention, mitigation, and resilience of software supply chain attacks. Introduction this report is based on a survey of it and security professionals responsible for software supply chain security. the survey reveals a cohort that overestimates the maturity of their software supply chain security efforts even as they grapple with significant challenges. We address the multifaceted challenges in securing the software supply chain, the limitations of current approaches, and how recent research contributes to the solution space. This article contains perspectives and knowledge obtained from intentional outreach with practitioners to understand their practical challenges and from extensive research efforts. we then provide an overview of current research efforts to secure the software supply chain.

Top 9 Software Supply Chain Security Tools Jit We address the multifaceted challenges in securing the software supply chain, the limitations of current approaches, and how recent research contributes to the solution space. This article contains perspectives and knowledge obtained from intentional outreach with practitioners to understand their practical challenges and from extensive research efforts. we then provide an overview of current research efforts to secure the software supply chain.
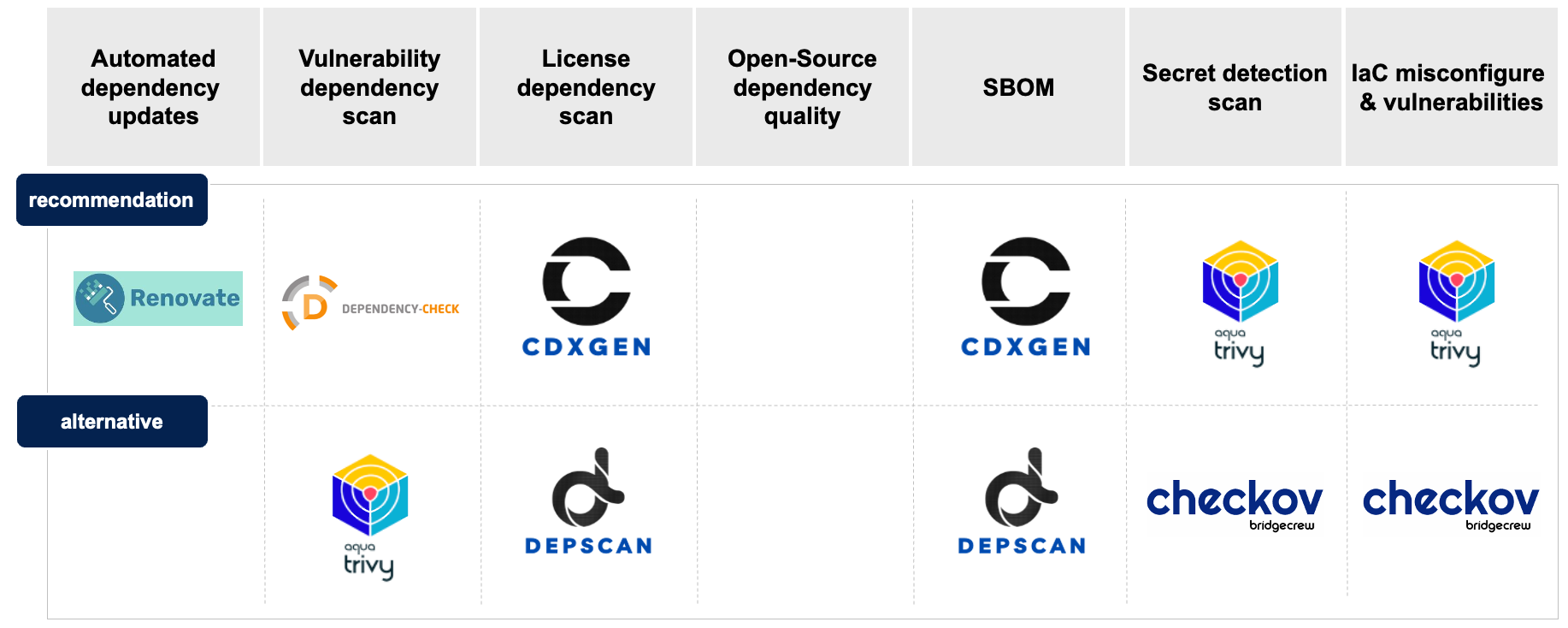
Open Source Tools For Software Supply Chain Security Senacor Blog
Comments are closed.