Software Security Ppt
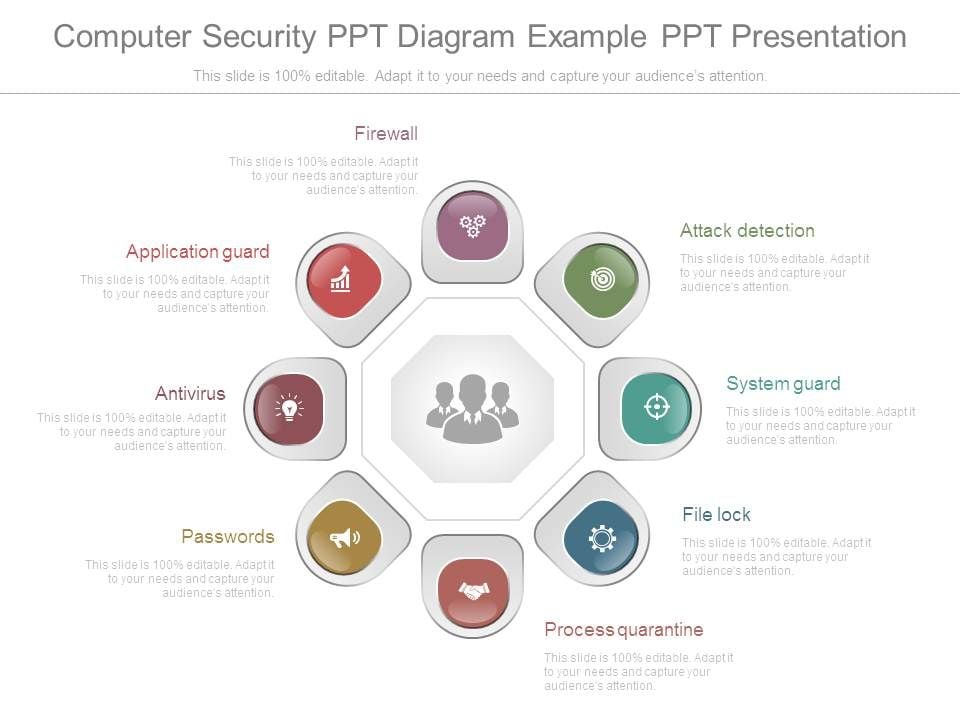
Computer Security Ppt Diagram Example Ppt Presentation The document discusses software security, detailing its role in both providing and undermining security through various principles, methods, and technologies. The document discusses the importance of software security and its basic components. it introduces software security, explaining that it aims to prevent undesirable behaviors by considering threats from malicious adversaries.

Ppt Software Security Powerpoint Presentation Free Download Id The solution • secure software development life cycle • deployment • monitor software in the field for security breaks • update software as needed • apply knowledge gained from attacks to improve security process and risk analysis for other projects. Boost your presentations with software security powerpoint templates crafted for clarity and engagement. examples include: main advantages of software security testing, web based. Security of a system depends on its threat model. least privilege, separation, and trust as concepts. security relies on abstractions to reduce complexity. reading assignment: butler lampson, protection, doi.acm.org 10.1145 775265.775268 . mathias payer (purdue university) cs 527 software security 2017 25 26 summary and conclusion. View software security intro.ppt from it ict502 at addis ababa university. cap6135: malware and software vulnerability analysis software security introduction cliff zou spring.
Ppt Software Security Powerpoint Presentation Free Download Id Security of a system depends on its threat model. least privilege, separation, and trust as concepts. security relies on abstractions to reduce complexity. reading assignment: butler lampson, protection, doi.acm.org 10.1145 775265.775268 . mathias payer (purdue university) cs 527 software security 2017 25 26 summary and conclusion. View software security intro.ppt from it ict502 at addis ababa university. cap6135: malware and software vulnerability analysis software security introduction cliff zou spring. Building secure software systems. learned how to apply best software security practices to various software artifacts throughout the software life cycle in an iterative approach. People will always concentrate on functionality first, and worry about security later (if at all) conclusions to prevent security problems, you must understand the security requirements & the threats that attackers pose aka threat modeling think like an attacker! know the technologies you use operating system programming language & platform. Start your meetings with eye popping presentations with software security presentation templates and google slides. What are the threats and vulnerabilities we’re up against? what are the resources and tools available to attackers? * security in software development life cycle source: gary mcgraw, software security, security & privacy magazine, ieee, vol 2, no. 2, pp. 80 83, 2004.

Software System Model Powerpoint Templates Slides And Graphics Building secure software systems. learned how to apply best software security practices to various software artifacts throughout the software life cycle in an iterative approach. People will always concentrate on functionality first, and worry about security later (if at all) conclusions to prevent security problems, you must understand the security requirements & the threats that attackers pose aka threat modeling think like an attacker! know the technologies you use operating system programming language & platform. Start your meetings with eye popping presentations with software security presentation templates and google slides. What are the threats and vulnerabilities we’re up against? what are the resources and tools available to attackers? * security in software development life cycle source: gary mcgraw, software security, security & privacy magazine, ieee, vol 2, no. 2, pp. 80 83, 2004.

Chapter 2 Software Security Full Slides Ppt Start your meetings with eye popping presentations with software security presentation templates and google slides. What are the threats and vulnerabilities we’re up against? what are the resources and tools available to attackers? * security in software development life cycle source: gary mcgraw, software security, security & privacy magazine, ieee, vol 2, no. 2, pp. 80 83, 2004.
Comments are closed.