Software Composition Analysis Loginsoft
Software Composition Analysis For Custom Applications Red Hawk Empower your software development with our software composition analysis. uncover and mitigate vulnerabilities in your codebase for a stronger security posture. Download and export a list of 15,080 companies that implement software composition analysis. data sourced and updated daily from job posting analysis across millions of listings worldwide.

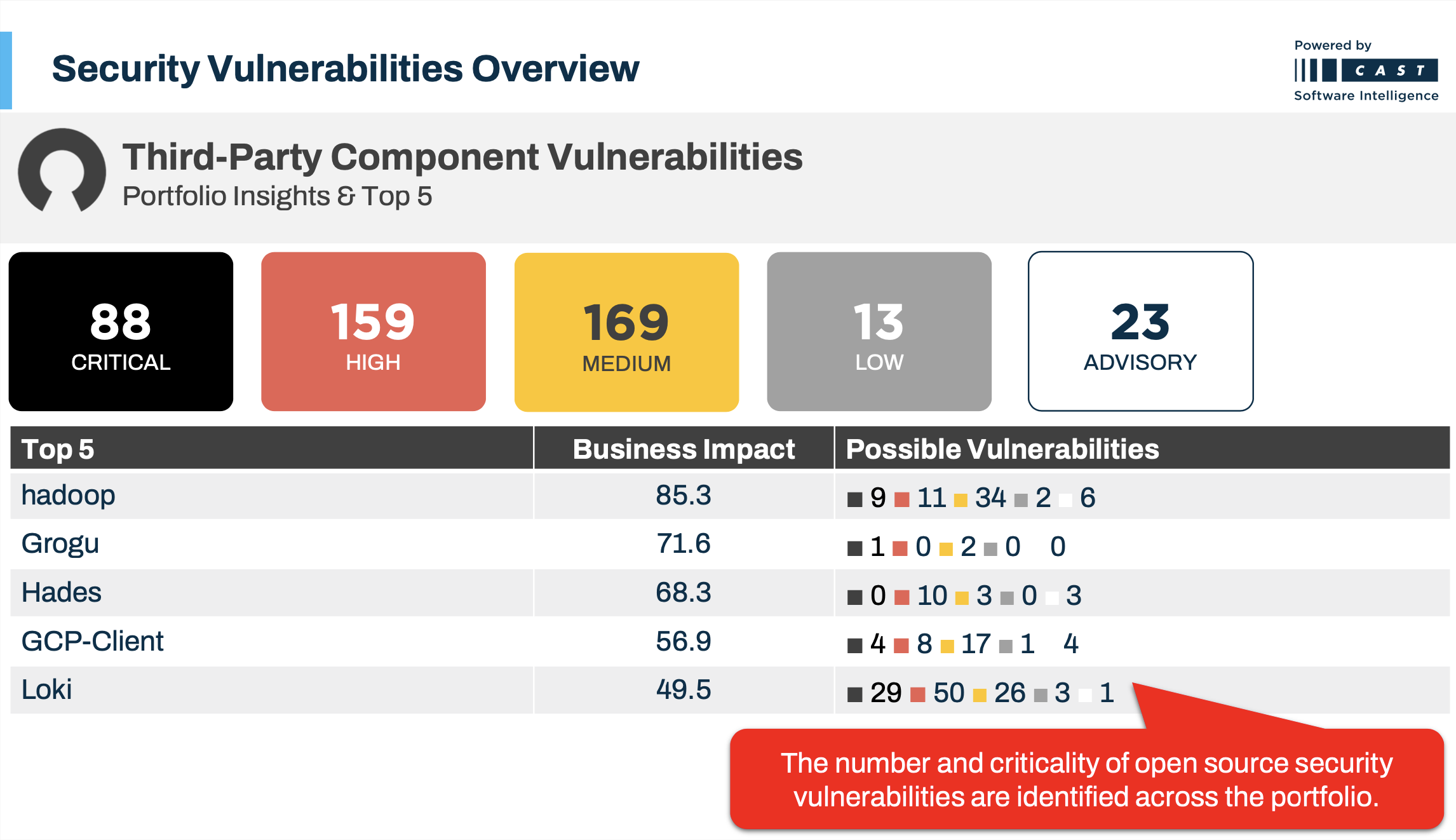
Xygeni S Software Composition Analysis Tool Xygeni In this blog, i will explore the top 10 sca tools for 2025, highlighting their primary use cases and key features. along with practical insights, i’ll share brief hands on experiences to help you understand how each tool fits into modern software security workflows. Software composition analysis (sca) is the process of analyzing software—most commonly software built from open source components—to ensure that is components are up to date, secure and in license compliance. The goal of sca is to identify potential security vulnerabilities, licensing issues, or outdated components in the software being developed or used. this article focuses on discussing software composition analysis (sca) in detail. Explore features such as open source component scanning, license compliance checks, and vulnerability management to ensure your software is built securely and efficiently.
Software Composition Analysis For Custom Applications Red Hawk The goal of sca is to identify potential security vulnerabilities, licensing issues, or outdated components in the software being developed or used. this article focuses on discussing software composition analysis (sca) in detail. Explore features such as open source component scanning, license compliance checks, and vulnerability management to ensure your software is built securely and efficiently. Software composition analysis (sca) is a practice in the fields of information technology and software engineering for analyzing custom built software applications to detect embedded open source software and detect if they are up to date, contain security flaws, or have licensing requirements. With over 20 years in the industry as a chief technology officer, i’ve tested and reviewed dozens of software composition analysis tools across real environments to evaluate accuracy, integration depth, and usability. In this article, we'll explore what software composition analysis is and how it fits into your organization’s broader security strategy. we'll walk through how sca works and discuss its benefits and challenges. A comprehensive list of software composition analysis tools. following repo contains a collection of sca tools which can be used to analyze risks in third party components which were used as part of code.

Software Composition Analysis Beginners Advanced Practitioners Software composition analysis (sca) is a practice in the fields of information technology and software engineering for analyzing custom built software applications to detect embedded open source software and detect if they are up to date, contain security flaws, or have licensing requirements. With over 20 years in the industry as a chief technology officer, i’ve tested and reviewed dozens of software composition analysis tools across real environments to evaluate accuracy, integration depth, and usability. In this article, we'll explore what software composition analysis is and how it fits into your organization’s broader security strategy. we'll walk through how sca works and discuss its benefits and challenges. A comprehensive list of software composition analysis tools. following repo contains a collection of sca tools which can be used to analyze risks in third party components which were used as part of code.

Software Composition Analysis Ibm Concert In this article, we'll explore what software composition analysis is and how it fits into your organization’s broader security strategy. we'll walk through how sca works and discuss its benefits and challenges. A comprehensive list of software composition analysis tools. following repo contains a collection of sca tools which can be used to analyze risks in third party components which were used as part of code.
Comments are closed.