Soc Vulnerability 5
Soc Vulnerability 5 Detect vulnerabilities: a vulnerability is a weakness that an attacker can exploit to carry out things beyond their permission level. a vulnerability might be discovered in any device’s. Many organizations are now integrating vulnerability and exposure management into the soc, leveraging existing triage and incident response processes. this ensures faster detection, prioritization, and resolution using the same 24 7 monitoring and response capabilities.
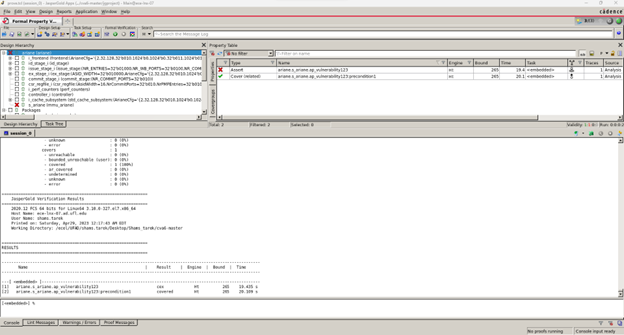
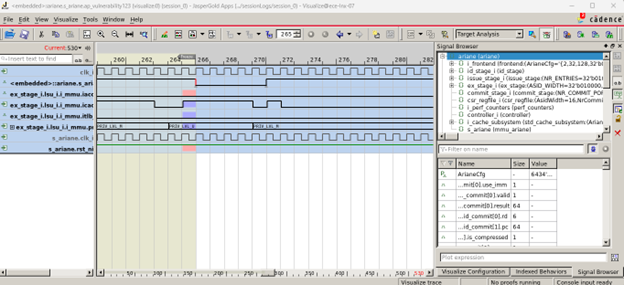
Soc Vulnerability 5 This vulnerability allows any attacker to access supervisor or machine level memory pages from user level privilege mode without generating any data access error. Critical security – february 2026 – cve 2026 2699 and cve 2026 2701.the progress sharefile team recently confirmed critical security vulnerabilities in sharefile storage zones controller v5 version deployments for customer managed zones. On march 31, 2026, a threat actor hijacked the npm account of the lead axios maintainer and published two malicious versions of one of the world’s most. Due to the increasing complexity of modern system on chips (socs) and the diversity of the attack surface, popular soc verification approaches used in industry.

Soc Vulnerability 1 On march 31, 2026, a threat actor hijacked the npm account of the lead axios maintainer and published two malicious versions of one of the world’s most. Due to the increasing complexity of modern system on chips (socs) and the diversity of the attack surface, popular soc verification approaches used in industry. These vulnerable systems are meant to be representative "implementations" of the case that designer integrator mistakes result in vulnerabilities described at a high level in cwe cve databases. the benchmark socs are based on open source risc v socs, namely neorv32 and ibex. You can view cve vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time. The august 2025 f5 breach exposed big ip source code and internal vulnerability data, giving attackers a roadmap to future exploits. learn how soc teams can identify exposure, secure management interfaces, patch fast, and hunt for early compromise indicators before adversaries strike. Sql injection is a web security vulnerability that occurs when an attacker is able to manipulate a sql query by injecting malicious input through user input fields, such as forms or url.

Soc Vulnerability 1 These vulnerable systems are meant to be representative "implementations" of the case that designer integrator mistakes result in vulnerabilities described at a high level in cwe cve databases. the benchmark socs are based on open source risc v socs, namely neorv32 and ibex. You can view cve vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time. The august 2025 f5 breach exposed big ip source code and internal vulnerability data, giving attackers a roadmap to future exploits. learn how soc teams can identify exposure, secure management interfaces, patch fast, and hunt for early compromise indicators before adversaries strike. Sql injection is a web security vulnerability that occurs when an attacker is able to manipulate a sql query by injecting malicious input through user input fields, such as forms or url.
Comments are closed.