Soc Vulnerability 1

Soc Vulnerability 1 Learn about the soc team and their processes. technology has made our lives more efficient, but with this efficiency comes more responsibility. modern day fears have come a long way from the. In this walkthrough on the systems as attack vectors room we learn how attackers exploit vulnerable and misconfigured systems, and how you can protect them.

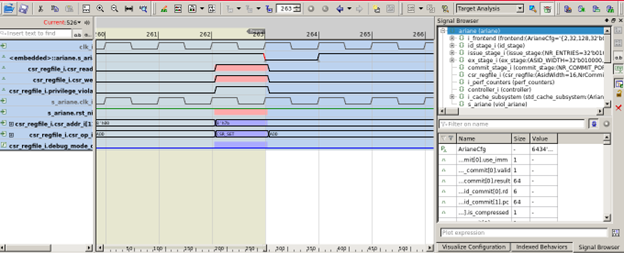
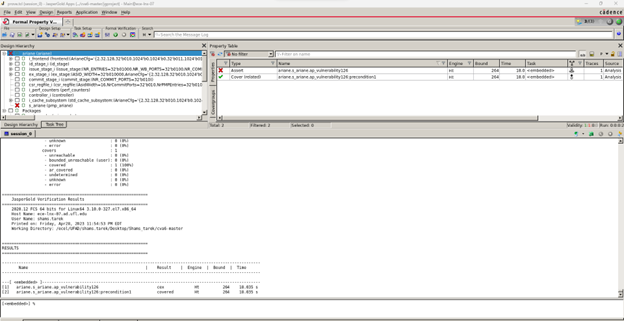
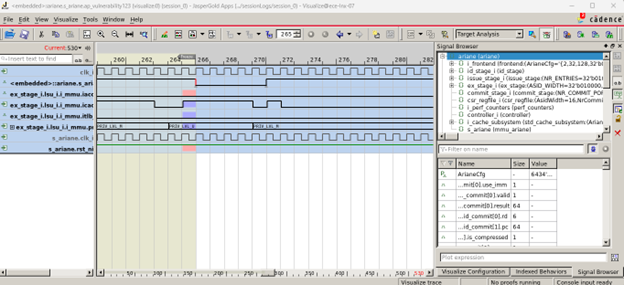
Soc Vulnerability 1 This path introduces a wide array of essential defensive security topics and real world analysis scenarios. by completing it, you will gain the knowledge and practical skills needed to become a successful soc level 1 analyst, or to better structure your existing expertise if you are already working in the field. In a system on chip (soc), software will commonly access the peripherals through a memory mapped register interface. thus, software can access only certain registers with respect to their privilege level hardcoded in the design. Security operations centers (socs) are structured in tiers to streamline incident management and enhance threat response efficiency. these tiers, typically categorized from tier 1 to tier 3, reflect escalating levels of expertise and accountability in cybersecurity workflows. Many organizations are now integrating vulnerability and exposure management into the soc, leveraging existing triage and incident response processes. this ensures faster detection, prioritization, and resolution using the same 24 7 monitoring and response capabilities.
Soc Vulnerability 4 Security operations centers (socs) are structured in tiers to streamline incident management and enhance threat response efficiency. these tiers, typically categorized from tier 1 to tier 3, reflect escalating levels of expertise and accountability in cybersecurity workflows. Many organizations are now integrating vulnerability and exposure management into the soc, leveraging existing triage and incident response processes. this ensures faster detection, prioritization, and resolution using the same 24 7 monitoring and response capabilities. From incident response to threat hunting, siem mastery to phishing detection, this guide equips you with the skills and knowledge to excel as a soc professional. In this blog, we will cover the concepts as well as the answers for the “soc fundamentals” room which is a part of the “cyber security 101” learning path. You are the level 1 analyst of your organization’s soc team. you receive an alert that a port scanning activity has been observed on one of the hosts in the network. • discuss mitigation strategy between soc, risk management, and it support teams. that can range from an immediate shutdown to wait till the next patching window, depending on many factors such as the triage result and the availability and impact of the patch workaround.
Soc Vulnerability 6 From incident response to threat hunting, siem mastery to phishing detection, this guide equips you with the skills and knowledge to excel as a soc professional. In this blog, we will cover the concepts as well as the answers for the “soc fundamentals” room which is a part of the “cyber security 101” learning path. You are the level 1 analyst of your organization’s soc team. you receive an alert that a port scanning activity has been observed on one of the hosts in the network. • discuss mitigation strategy between soc, risk management, and it support teams. that can range from an immediate shutdown to wait till the next patching window, depending on many factors such as the triage result and the availability and impact of the patch workaround.
Soc Vulnerability 5 You are the level 1 analyst of your organization’s soc team. you receive an alert that a port scanning activity has been observed on one of the hosts in the network. • discuss mitigation strategy between soc, risk management, and it support teams. that can range from an immediate shutdown to wait till the next patching window, depending on many factors such as the triage result and the availability and impact of the patch workaround.

Vulnerability Soc Prime
Comments are closed.