Soc Tools Siem Edr Xdr Mdr And Soar Explained

Edr Vs Xdr Vs Siem Vs Mdr Vs Soar Pdf Security Computer Security Edr, mdr, xdr, siem, soar — which tool will strengthen your security? find out how each fits your needs and helps protect from threats. We explain the key technical terms in incident detection and response – mdr, soc, edr, xdr, soar and siem.
Soc Tools Siem Edr Xdr Mdr And Soar Explained Infosec Guardians Explore ndr, mdr, xdr, edr, siem, and soar. understand these key cybersecurity acronyms and their roles in protecting your network from cyber threats. As a leader in the edr market and a pioneer in emerging xdr technology, we are often asked to clarify what it means and how it can ultimately help deliver better customer outcomes. this post aims to clarify some common questions around xdr and differences compared to edr, siem, and soar. In this blog, we’ll break down six key cybersecurity technologies — soar, siem, edr, xdr, ndr, and mdr — and demonstrate their synergy through a real world scenario. In today’s complex cybersecurity landscape, understanding the roles of av, edr, xdr, mdr, siem, soar, and mssps is essential for building a resilient defense strategy. this guide breaks down what each tool does, how they differ, and how they integrate into a unified security architecture.

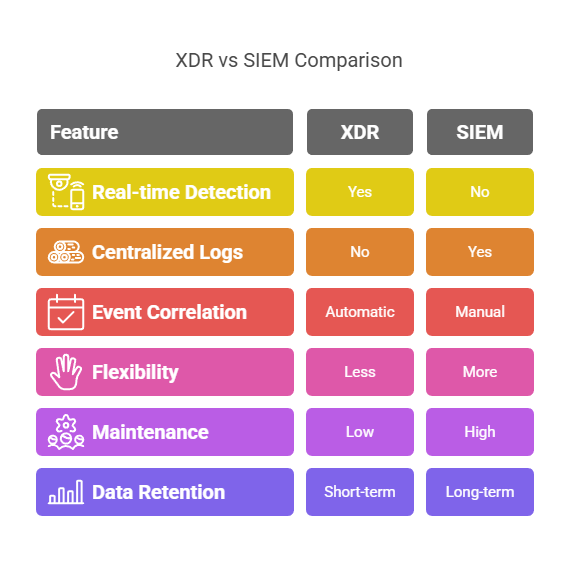
Edr Mdr Xdr Siem Soar Cybersecurity Tools Compared In this blog, we’ll break down six key cybersecurity technologies — soar, siem, edr, xdr, ndr, and mdr — and demonstrate their synergy through a real world scenario. In today’s complex cybersecurity landscape, understanding the roles of av, edr, xdr, mdr, siem, soar, and mssps is essential for building a resilient defense strategy. this guide breaks down what each tool does, how they differ, and how they integrate into a unified security architecture. Clear comparison of siem, xdr, mdr, and soar: what each does, how they differ, and which combination fits your threat detection strategy. Among the array of cybersecurity acronyms, edr, xdr, ndr, mdr, siem, and soar stand out as essential tools for detecting, responding to, and mitigating security incidents. In this article, we delve into the key characteristics and distinctions between soc, siem, edr, ndr, xdr, and mdr. Mature soc operations benefit from integrated platforms combining siem, soar, edr, and threat intelligence, enabling sophisticated threat detection and automated response workflows.

Edr Mdr Xdr Siem Soar Cybersecurity Tools Compared Clear comparison of siem, xdr, mdr, and soar: what each does, how they differ, and which combination fits your threat detection strategy. Among the array of cybersecurity acronyms, edr, xdr, ndr, mdr, siem, and soar stand out as essential tools for detecting, responding to, and mitigating security incidents. In this article, we delve into the key characteristics and distinctions between soc, siem, edr, ndr, xdr, and mdr. Mature soc operations benefit from integrated platforms combining siem, soar, edr, and threat intelligence, enabling sophisticated threat detection and automated response workflows.

Edr Mdr Xdr Siem Soar Cybersecurity Tools Compared In this article, we delve into the key characteristics and distinctions between soc, siem, edr, ndr, xdr, and mdr. Mature soc operations benefit from integrated platforms combining siem, soar, edr, and threat intelligence, enabling sophisticated threat detection and automated response workflows.
Edr Mdr Xdr Siem Soar Cybersecurity Tools Compared
Comments are closed.